Cybersecurity researchers have disclosed a malicious marketing campaign that leverages search engine marketing (web optimization) poisoning methods to ship a recognized malware loader known as Oyster (aka Broomstick or CleanUpLoader).
The malvertising exercise, per Arctic Wolf, promotes pretend web sites internet hosting trojanized variations of reputable instruments like PuTTY and WinSCP, aiming to trick software program professionals trying to find these applications into putting in them as an alternative.
“Upon execution, a backdoor often known as Oyster/Broomstick is put in,” the corporate mentioned in a quick printed final week.
“Persistence is established by making a scheduled job that runs each three minutes, executing a malicious DLL (twain_96.dll) by way of rundll32.exe utilizing the DllRegisterServer export, indicating the usage of DLL registration as a part of the persistence mechanism.”
The names of a number of the bogus web sites are listed beneath –
- updaterputty[.]com
- zephyrhype[.]com
- putty[.]run
- putty[.]guess, and
- puttyy[.]org
It is suspected that the menace actors behind the marketing campaign may be focusing on different IT instruments to ship the malware, making it crucial that customers keep on with trusted sources and official vendor websites to obtain the mandatory software program.
The disclosure comes as black hat web optimization poisoning methods are getting used to recreation search outcomes related to synthetic intelligence (AI)-related key phrases to unfold Vidar, Lumma, and Legion Loader.
These web sites come fitted with JavaScript code that checks for the presence of ad blockers and gathers info from the sufferer’s browser, earlier than initiating a redirection chain that finally takes the sufferer to a phishing web page internet hosting a ZIP archive.
“The ultimate obtain pages on this marketing campaign ship Vidar Stealer and Lumma Stealer as password-protected ZIP archives, with the password offered on the ultimate downloading web page,” Zscaler ThreatLabz mentioned. “As soon as extracted, they comprise an 800MB NSIS installer, a deceptively massive measurement meant to seem reputable and bypass detection techniques with file measurement limitations.”
The NSIS installer is then used to execute an AutoIt script that is finally liable for launching the stealer payloads. The supply mechanism for Legion Loader, in distinction, leverages an MSI installer to deploy the malware by way of a batch script.
The same web optimization poisoning marketing campaign has been noticed to raise phishing pages when customers seek for the names of common net functions to direct customers to pretend Cloudflare CAPTCHA verify pages that make use of the notorious ClickFix technique to drop RedLine Stealer by way of Hijack Loader.
In keeping with information compiled by Kaspersky, small- and medium-sized companies (SMBs) are being more and more focused by cyber assaults that ship malware disguised as common AI and collaboration instruments like OpenAI ChatGPT, DeepSeek, Cisco AnyConnect, Google Drive, Microsoft Workplace, Microsoft Groups, Salesforce, and Zoom.
“Between January and April 2025 alone, round 8,500 small and medium-sized enterprise customers had been focused by cyberattacks during which malware or probably undesirable software program was disguised as these common instruments,” the Russian cybersecurity firm mentioned.
Zoom accounted for about 41% of the full variety of distinctive information, adopted by Outlook and PowerPoint at 16% every, Excel at 12%, Phrase at 9%, and Groups at 5%. The variety of distinctive malicious information mimicking ChatGPT elevated by 115% to 177 within the first 4 months of 2025.
Whereas the pattern of abusing pretend search engine listings to benefit from customers’ implicit in common manufacturers is a widely known tactic, current campaigns have hijacked searches for tech assist pages linked to Apple, Financial institution of America, Fb, HP, Microsoft, Netflix, and PayPal to serve reputable pages by way of sponsored ends in Google – however with an ingenious twist.
“Guests are taken to the assistance/assist part of the model’s web site, however as an alternative of the real cellphone quantity, the hijackers show their scammy quantity as an alternative,” Malwarebytes mentioned.
That is achieved by the use of a way known as search parameter injection to point out inside a search bar a quantity that is underneath the attacker’s management with a purpose to give the impression that it is an official search consequence throughout the assist heart pages and deceive unsuspecting customers into calling them.
What makes the assault significantly insidious is that the parameters added to the proper of the particular assist heart area (e.g., “Name us 1-***-***-**** without spending a dime”) aren’t seen within the sponsored search consequence, thereby giving no purpose for customers to suspect something is amiss.
It isn’t simply Google’s promoting platform. Menace actors have additionally been caught serving pretend adverts on Fb to phish for cryptocurrency pockets restoration phrases and spreading malware at the side of Pi2Day, a yearly occasion linked to the Pi Community group.
The malware, unfold by way of adverts urging customers to put in a brand new model of the Pi Community desktop app for Home windows, comes with capabilities to steal saved credentials and crypto pockets keys, log person enter, and obtain extra payloads, all of the whereas evading detection.
Romanian cybersecurity firm Bitdefender mentioned the exercise is probably the work of a single menace actor that is “operating parallel fraud schemes on Meta to maximise attain, monetary acquire, and focusing on effectivity.”
It does not finish right here, for phony web sites impersonating AI, VPN providers, and different well-known software program manufacturers have been discovered to ship Poseidon Stealer on macOS techniques and a loader dubbed PayDay Loader, which then acts as a conduit for Lumma Stealer on Home windows machines. The exercise has been codenamed Darkish Companions by safety researcher g0njxa.
PayDay Loader depends on Google Calendar hyperlinks as a lifeless drop resolver to extract the command-and-control (C2) server and acquire obfuscated JavaScript code engineered to load the Lumma Stealer payload and siphon delicate information.
Apparently, the e-mail deal with used to create the Google Calendar occasions (“echeverridelfin@gmail[.]com”) was additionally noticed in reference to a malicious npm bundle known as “os-info-checker-es6.” This means that the Darkish Companions actors have doubtless experimented with totally different supply mechanisms.
“The PayDay Loader has a Node.js stealer module to exfiltrate cryptocurrencies pockets information to an exterior C2,” g0njxa mentioned. “Utilizing the ADM-ZIP library for Node.js , the PayDay Loader is ready to discover, pack, and ship pockets info to a hard-coded C2 host.”
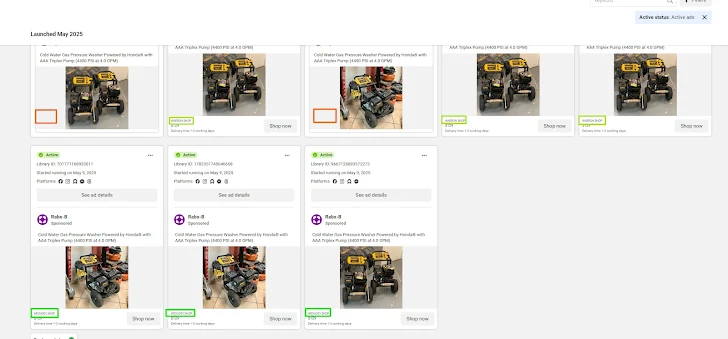
These campaigns go hand in hand with an ongoing phenomenon the place scammers and cybercriminals arrange sprawling networks comprising 1000’s of internet sites to spoof common manufacturers and commit monetary fraud by promoting actual merchandise which might be by no means delivered. One such community, dubbed GhostVendors by Silent Push, buys Fb adverts area to advertise over 4,000 sketchy websites.
The malicious Fb Market adverts are run for a number of days, after which they’re stopped, successfully deleting all traces of them from the Meta Ad Library. It is price stating that Meta has solely retained adverts on social points, elections, and politics for the previous seven years.
“This helped to verify a recognized Meta ad library coverage existed, and highlighted that probably these menace actors had been profiting from this by quickly launching and stopping adverts for related merchandise on totally different pages,” Silent Push researchers mentioned.
One other community noticed by the corporate, focusing on English and Spanish language customers with pretend market adverts, is assessed to be the work of Chinese language menace actors. These web sites are primarily designed to steal bank card info entered on fee pages, whereas claiming to course of the orders. A number of the bogus websites additionally embrace Google Pay buy widgets to allow funds.
“This pretend market marketing campaign primarily targets shoppers with a phishing menace that exploits main manufacturers, well-known organizations, and the celebrity of some political figures,” Silent Push mentioned.