Amazon SageMaker introduced a brand new characteristic that you need to use so as to add {custom} tags to assets created by way of an Amazon SageMaker Unified Studio challenge. This helps you implement tagging requirements that conform to your group’s service management insurance policies (SCPs) and helps allow price monitoring reporting practices on assets created throughout the group.
As a SageMaker administrator, you possibly can configure a challenge profile with tag configurations that might be pushed right down to initiatives that presently use or will use that challenge profile. The challenge profile is ready as much as go both required key and worth tag pairings or go the important thing of the tag with a default worth that may be modified throughout challenge creation. All tags handed to the challenge will consequence within the assets created by that challenge being tagged. This gives you with a governance mechanism that enforces that challenge assets have the anticipated tags throughout all initiatives of the area.
The primary launch of {custom} tags for challenge assets is supported by way of an utility programming interface (API), by way of Amazon DataZone SDKs. On this submit, we take a look at use circumstances for {custom} tags and find out how to use the AWS Command Line Interface (AWS CLI) so as to add tags to challenge assets.
What we hear from prospects
As prospects proceed to construct and collaborate utilizing AWS instruments for mannequin improvement, generative AI, information processing, and SQL analytics, they see the necessity to carry management and visibility into the assets being created. To assist connectivity to those AWS instruments from SageMaker Unified Studio initiatives, many various kinds of assets throughout AWS companies must be created. These assets are created by way of AWS CloudFormation stacks (by way of challenge surroundings deployment) by the Amazon SageMaker service. From prospects we hear the next use circumstances:
- Clients must implement that tagging practices conform to firm insurance policies by way of using AWS controls, equivalent to SCPs, for useful resource creation. These controls block the creation of assets except particular tags are positioned on the useful resource.
- Clients may begin with insurance policies to implement that the right tags are positioned when assets are created with the extra purpose of standardizing on useful resource reporting. By inserting identifiable info on assets when created, they implement consistency and completeness when performing price attribution reporting and observability.
Buyer Swiss Life makes use of SageMaker as a single answer for cataloging, discovery, sharing, and governance of their enterprise information throughout enterprise domains. They require all assets have a set of necessary tags for his or her finance group to invoice organizations throughout their firm for the AWS assets created.
“The launch of challenge useful resource tags for Amazon SageMaker permits us to carry visibility to the prices incurred throughout our accounts. With this functionality we’re in a position to meet the useful resource tagging tips of our firm and believe in attributing prices throughout our multi-account setup for the assets created by Amazon SageMaker initiatives.”
– Tim Kopacz, Software program Developer at Swiss Life
Conditions
To get began with {custom} tags, you have to have the next assets:
- A SageMaker Unified Studio area.
- An AWS Identification and Entry Administration (IAM) entity with privileges to make AWS CLI calls to the area.
- An IAM entity licensed to make adjustments to the area IAM provisioning function. If SageMaker created this for you, it is going to be known as
AmazonSageMakerProvisioning-. The provisioning function provisions and manages assets outlined within the chosen blueprints in your account.
The right way to arrange challenge useful resource tags
The next steps define how one can configure {custom} tags to your SageMaker Unified Studio challenge assets:
- (Elective) Replace the SageMaker provisioning function to allow particular tag keys.
- Create a brand new challenge profile with challenge useful resource tags configured.
- Create a brand new challenge with challenge useful resource tags.
- Replace an present challenge with challenge useful resource tags.
- Validate that the assets are tagged.
(Elective) Replace a SageMaker provisioning function to allow tag key values
The AmazonSageMakerProvisioning- function has an AWS managed coverage with situation aws:TagKeys permitting tags to be created by this function provided that the tag key begins with AmazonDataZone. For this instance, we are going to change the tag key to start with completely different strings. Skip to Create a brand new challenge profile with challenge useful resource tags configured when you don’t want tag keys to have a distinct construction (equivalent to begins with, incorporates, and so forth)
- Open the AWS Administration Console and go to IAM.
- Within the navigation pane, select Roles.
- Within the checklist, select AmazonSageMakerProvisioning-
. - Select the Permissions tab.
- Select Add permissions, after which select Create inline coverage.
- Below Coverage editor, choose JSON.
- Enter the next coverage. Add the strings beneath the situation
aws:TagKeys. On this instance, tag keys starting with ACME or tag keys with the precise match of CostCenter might be created by the function.
It’s doable to scope down the particular AWS service tag and un-tag permissions primarily based on which blueprints or capabilities are getting used.
Create a brand new challenge profile with challenge useful resource tags configured
Use the next steps to create a brand new SQL Analytics challenge profile with {custom} tags. The instance makes use of AWS CLI instructions.
- Open the AWS CloudShell console.
- Create a challenge profile utilizing the next CLI command.
- The
project-resource-tagsparameter consists ofkey(tag key),worth(tag worth), andisValueEditable(boolean indicating if the tag worth may be modified throughout challenge creation or replace). - The
allow-custom-project-resource-tagsparameter set totruepermits the challenge creator to create extra key-value pairs. The important thing wants to adapt to the inline coverage of theAmazonSageMakerProvisioning-function. - The
project-resource-tags-descriptionparameter is an outline subject for challenge useful resource tags. The max character restrict is 2,048. The outline must be handed in each timecreate-project-profileorupdate-project-profileis named.
- The
This challenge profile can have the tag ACME-Software = SageMaker positioned on all initiatives related to the challenge profile and can’t be modified by the challenge creator. The tag CostCenter = 123 can have the worth modified by the challenge creator as a result of the isValueEditable property is ready to true.
Grant permissions for customers to make use of the challenge profile throughout challenge creation. Within the Authorization part of the challenge profile set both Chosen customers or teams or Permit all customers and teams.
The usage of the allow-custom-project-resource-tags parameter means the challenge creator can add their very own tags (key-value pair). The important thing should conform to the situation examine within the coverage of the provisioning function (AmazonSageMakerProvisioning-). If the allow-custom-project-resource-tagsparameter is modified to false after a challenge created tags, tags created by the challenge might be eliminated throughout the subsequent challenge replace.
Updates to the challenge profile
Updates to challenge useful resource tags are doable by way of the update-project-profile command. The command will substitute all values within the project-resource-tags part so remember to embrace the exhaustive set of tags. Updates to the challenge profile are mirrored in initiatives after operating the update-project command or when a brand new challenge is created utilizing the challenge profile. The next instance provides a brand new tag, ACME-BusinessUnit = Retail.
There are 3 ways to work with the project-resource-tags parameter when updating the challenge profile.
- Passing a non-empty checklist of challenge useful resource tags will substitute the tags presently configured on the challenge profile.
- Passing an empty checklist of challenge useful resource tags will filter out all beforehand configured tags:
--project-resource-tags '[]'
- Not together with the challenge useful resource tag parameter will preserve beforehand configured tags as-is.
Create a brand new challenge with challenge useful resource tags
The next steps stroll you thru creating a brand new challenge that inherits tags from the challenge profile and lets the challenge creator modify one of many tag values.
- Create a challenge utilizing the next instance CLI command.
- Modify the
CostCentertag worth utilizing the--resource-tagsparameter. Tags configured on the challenge profile the place theisValueEditableattribute isfalsemight be pushed to the challenge robotically.
Replace present challenge with challenge useful resource tags
For present initiatives related to the challenge profile, you have to replace the challenge for the brand new tags to be utilized.
- Replace the challenge utilizing the next instance CLI command.
- On this situation, an editable worth must be up to date and a brand new tag added. Tag
CostCentercan have its default worth overwritten as“789”and the brand newACME-Division = Financetag might be added.
Venture stage tags (these not configured from the challenge profile) must be handed throughout challenge replace to be preserved. For tags with isValueEditable = true configured from the challenge profile, any override beforehand set must be utilized or the worth will revert to the default from the challenge profile.
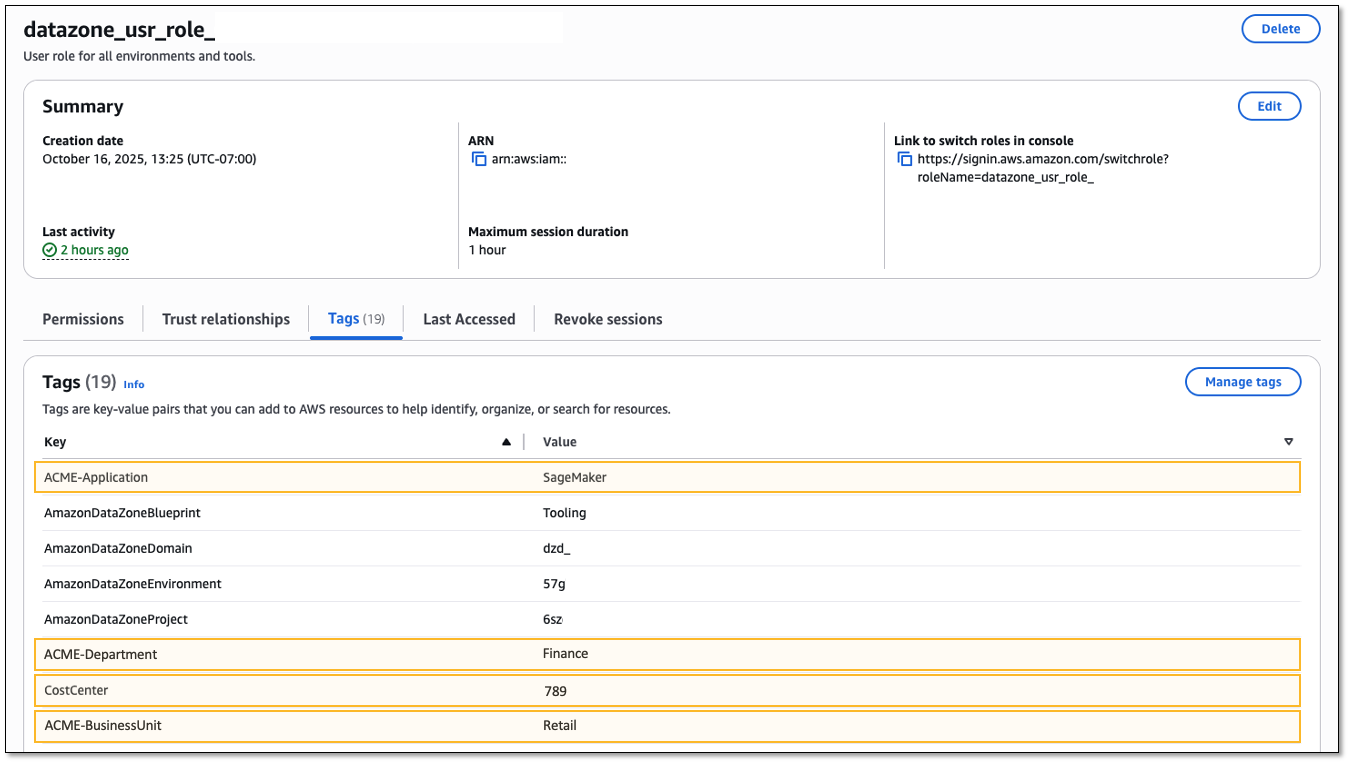
Validating assets are tagged
Validate that tags are positioned appropriately. An instance useful resource that’s created by the challenge is the challenge IAM function. Viewing the tags for this function ought to present the tags configured from the challenge profile.
- Open SageMaker Unified Studio to get the challenge function from the Venture particulars part of the challenge. The function title begins with
datazone_usr_role_. - Open the IAM console.
- Within the navigation pane, select Roles.
- Seek for the challenge IAM function.
- Choose the Tags tab.
Conclusion
On this submit, we mentioned tagging associated use circumstances from prospects and walked by way of getting began with {custom} tags in Amazon SageMaker to position tags on the assets created by the challenge. By giving directors a option to configure challenge profiles with standardized tag configurations, now you can assist guarantee constant tagging practices throughout all SageMaker Unified Studio initiatives whereas sustaining compliance with SCPs. This characteristic addresses two important buyer wants: implementing organizational tagging requirements by way of automated governance mechanisms and enabling correct price attribution reporting throughout multi-service deployments.
To study extra, go to Amazon SageMaker, then get began with Venture useful resource tags.
Concerning the authors


