
Risk actors have been utilizing a number of web sites promoted by way of Google advertisements to distribute a convincing PDF modifying app that delivers an info-stealing malware referred to as TamperedChef.
The marketing campaign is a component of a bigger operation with a number of apps that may obtain one another, a few of them tricking customers into enrolling their system into residential proxies.
Greater than 50 domains have been recognized to host deceiving apps signed with fraudulent certificates issued by a minimum of 4 totally different corporations.
The marketing campaign seems to be widespread and well-orchestrated because the operators waited for the advertisements to run their course earlier than activating the malicious parts within the purposes, researchers say.
Full replace delivers infostealer
A technical evaluation from cybersecurity companies firm Truesec describes the method of TamperedChef infostealer being delivered to a person’s system.
The researchers found that the malware was delivered by way of a number of web sites that promoted a free instrument referred to as AppSuite PDF Editor.
Based mostly on web information, the investigators decided that the marketing campaign began on June 26, when lots of the web sites concerned have been both registered or began to promote AppSuite PDF Editor.
Nevertheless, the researchers discovered that the malicious app had been verified by way of the VirusTotal malware scanning companies on Could fifteenth.
It seems that this system behaved usually till August twenty first, when it obtained an replace that activated malicious capabilities constructed to gather delicate information like credentials and internet cookies.
In accordance with Truesec, TamperedChef infostealer is delivered with the “-fullupdate” argument for the PDF editor’s executable.
The malware checks for varied safety brokers on the host. It additionally queries the databases of put in internet browsers utilizing the DPAPI (Information Safety Software Programming Interface) – a part in Home windows that encrypts delicate information.
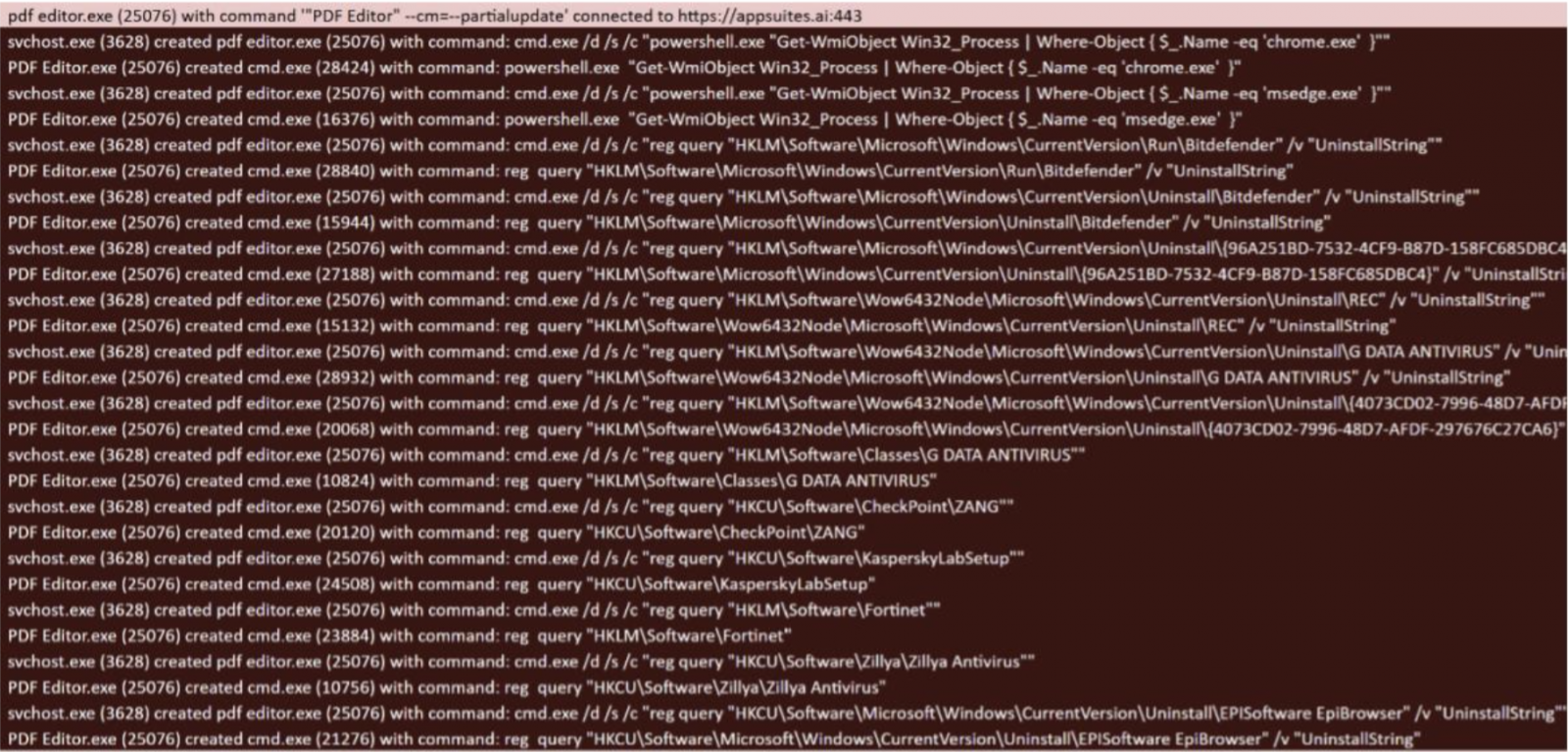
supply: Truesec
Digging deeper for the distribution methodology, Truesec researchers discovered proof suggesting that the risk actor spreading TamperedChef inside AppSuites PDF Editor relied on Google promoting to advertise the computer virus.
“Truesec has noticed a minimum of 5 totally different google marketing campaign IDs which suggests a widespread marketing campaign” – Truesec
The risk actor possible had a technique to maximise the variety of downloads earlier than activating the malicious part in AppSuites PDF Editor, as they delivered the infostealer simply 4 days earlier than the everyday expiration interval of 60 days for a Google advert marketing campaign.
Wanting additional into AppSuites PDF Editor, the researchers discovered that totally different variations of this system have been signed by certificates “from a minimum of 4 corporations,” amongst them ECHO Infini SDN BHD, GLINT By J SDN. BHD, and SUMMIT NEXUS Holdings LLC, BHD.
Becoming a member of a residential proxy
Truesec discovered that the operator of this marketing campaign has been energetic since a minimum of August 2024 and promoted different instruments, together with OneStart and Epibrowser browsers.
It’s price noting that OneStart is often flagged as a probably undesirable program (PUP), which is usually the time period for adware.
Nevertheless, researchers at managed detection and response firm Expel additionally investigated incidents involving AppSuites PDF Editor, ManualFinder, and OneStart, all “dropping extremely suspicious information, executing surprising instructions, and turning hosts into residential proxies,” which is nearer to malware-like habits.
They discovered that OneStart can obtain AppSuite-PDF (signed by an ECHO INFINI SDN. BHD certificates), which may fetch PDF Editor.
“The preliminary downloads for OneStart, AppSuite-PDF, and PDF Editor are being distributed by a big advert marketing campaign promoting PDFs and PDF editors. These advertisements direct customers to one in all many web sites providing downloads of AppSuite-PDF, PDF Editor, and OneStart,” Expel.
The code-signing certificates used on this marketing campaign have already been revoked, however the threat remains to be current for present installations.
In some situations of PDF Editor, the app would present customers a message asking for permission to make use of their machine as a residential proxy in return for utilizing the instrument without cost.
The researchers word that the proxy community supplier could also be a respectable entity not concerned within the marketing campaign and that the operator of PDF Editor is capitalizing as associates.
It seems that whoever is behind PDF Editor is making an attempt to maximise their revenue on the expense of customers worldwide.
Even when the applications on this marketing campaign are thought of PUPs, their capabilities are typical of malware and ought to be handled as such.
The researchers warn that the operation they uncovered entails extra apps, a few of them not but weaponized, able to distributing malware or suspicious information, or executing instructions surreptitiously on the system.
Each stories from Truesec and Expel [1, 2] embody a big set of indicators of compromise (IoCs) that might assist defenders defend customers and property from getting contaminated.



