What is going on?
On January 6th, 2025, the Workplace of Civil Rights (OCR) revealed a brand new set of cybersecurity necessities as a part of the Discover of Proposed Rulemaking (NPRM) within the Federal Register. The proposal mandates that healthcare organizations strengthen their cybersecurity defenses, transitioning from a reactive method to a risk-based focus. As soon as finalized, it’ll end in an replace to the Safety Rule of the Well being Insurance coverage Portability and Accountability Act (HIPAA).
What’s the HIPAA Safety Rule and the Proposed Replace?
The HIPAA Safety Rule established nationwide requirements to guard people’ digital private well being data (ePHI) that’s created, acquired, used or maintained by a coated entity. It required the implementation of applicable administrative, bodily, and technical safeguards to make sure the confidentiality, integrity, and safety of digital protected well being data. Nonetheless, the present HIPAA Safety Rule has confirmed inadequate and is outdated. A major overhaul was wanted to handle at this time’s quickly evolving menace panorama.
That is the aim of the HIPAA Safety Rule Replace. The proposed replace goals to realize the next outcomes:
- Strengthen the Safety Rule
- Deal with the rise in cyberattacks and breaches in healthcare
- Shift from reactive and preventative approaches to a cyber resilience mindset
Why does it matter?
This can be a important replace within the healthcare sector, because the replace removes the addressable implementation specs definition (thought-about non-obligatory) which means that every one implementation specs will now be necessary.
Some examples of newly required implementation specs embrace community segmentation, encryption, and multi-factor authentication (MFA). Moreover, the brand new rule replace emphasizes a risk-based method to safety, which can require organizations to revise inside processes and undertake applicable applied sciences to help this shift. This locations elevated stress on IT and community safety groups to adapt shortly with the intention to meet the brand new compliance necessities.
Certainly one of HIPAA’s key callouts is particularly targeted on community segmentation. The safety rule replace describes community segmentation as a “bodily or digital division of a community into a number of segments, creating boundaries between the operational and IT networks to scale back dangers, reminiscent of threats attributable to phishing assaults”. The first goal of community segmentation is to forestall and include lateral motion by attackers inside an setting.
How can Cisco Safe Workload assist my group keep compliant?
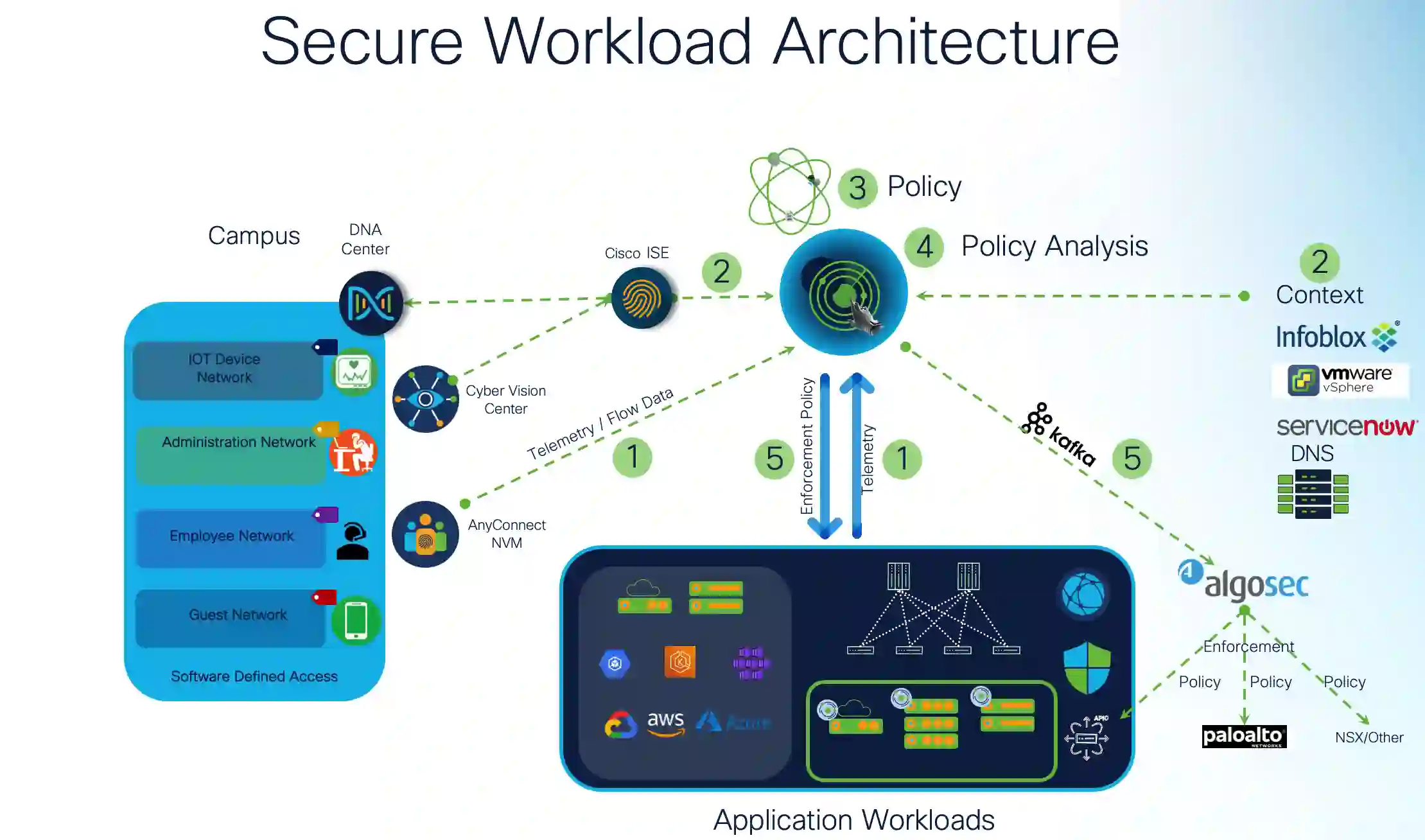
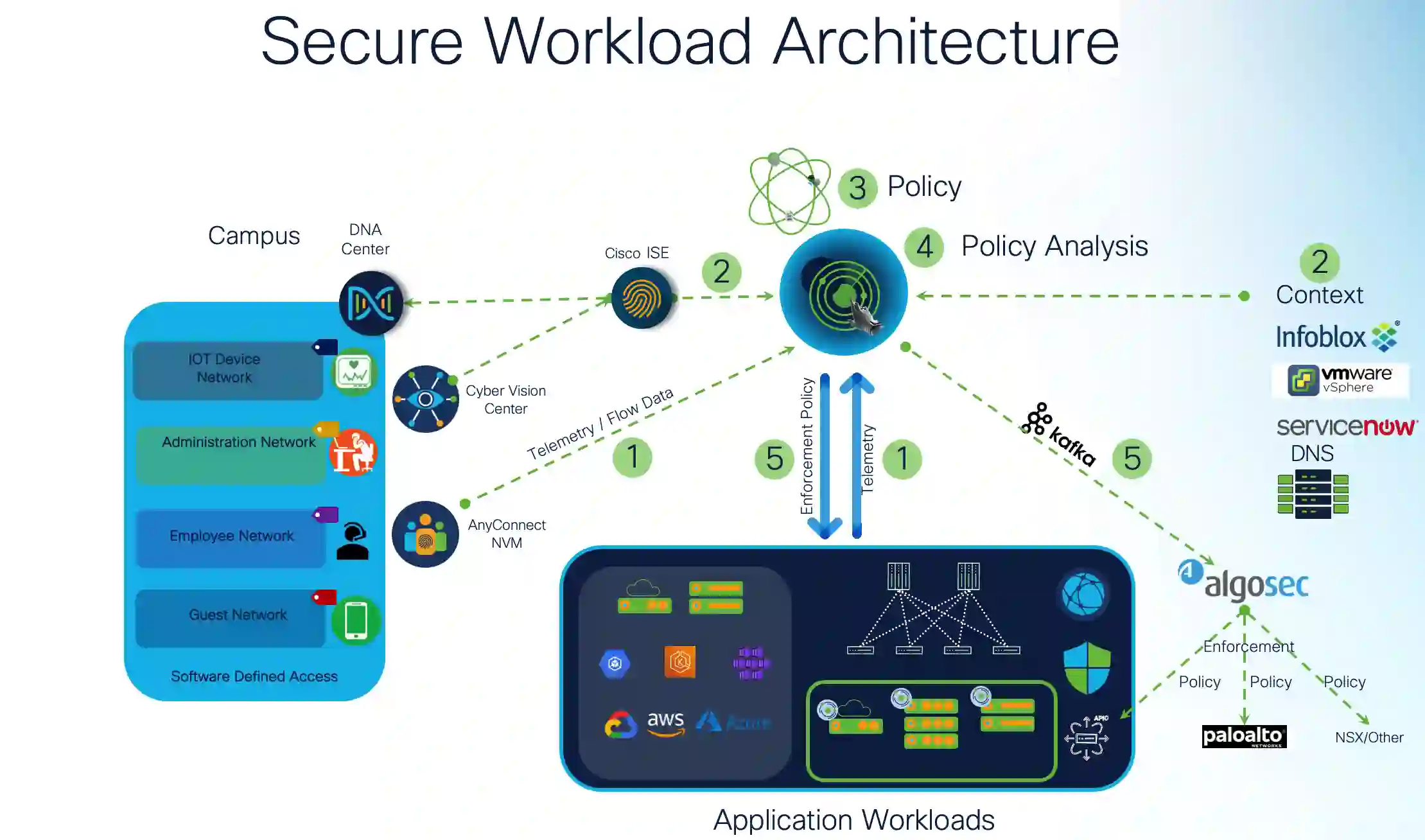
Cisco Safe Workload seamlessly delivers zero belief micro-segmentation to your software workloads throughout any location, any infrastructure and any kind issue workload from a single console. With complete visibility into each workload interplay and highly effective AI/ML pushed coverage lifecycle automation, Safe Workload reduces the assault floor, prevents lateral motion, identifies workload habits anomalies, helps quickly remediate threats, and repeatedly displays compliance.
Cisco Safe Workload may also help your group keep compliant with the HIPAA Safety Rule Replace in two key areas:
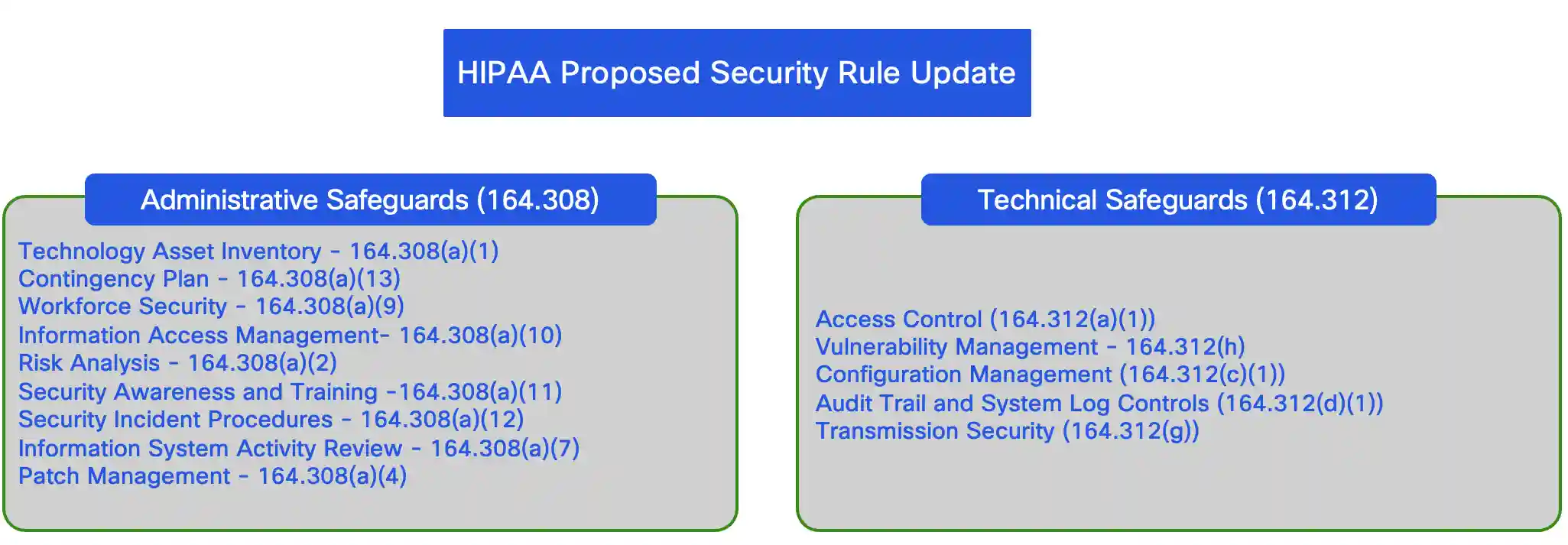
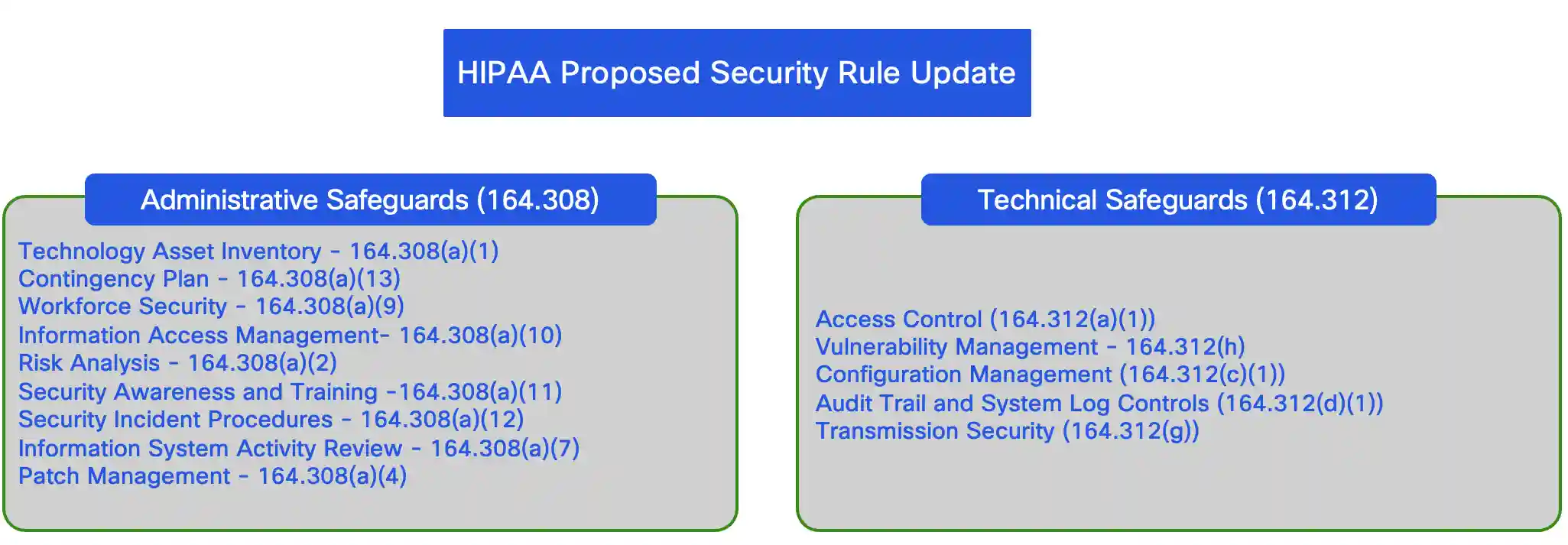
Administrative Safeguards: Discuss with the insurance policies and procedures designed to handle the choice, growth, implementation, and upkeep of safety measures to guard ePHI and handle workforce conduct.
Technical Safeguards: Embody the know-how and associated insurance policies that defend ePHI and management entry to it.
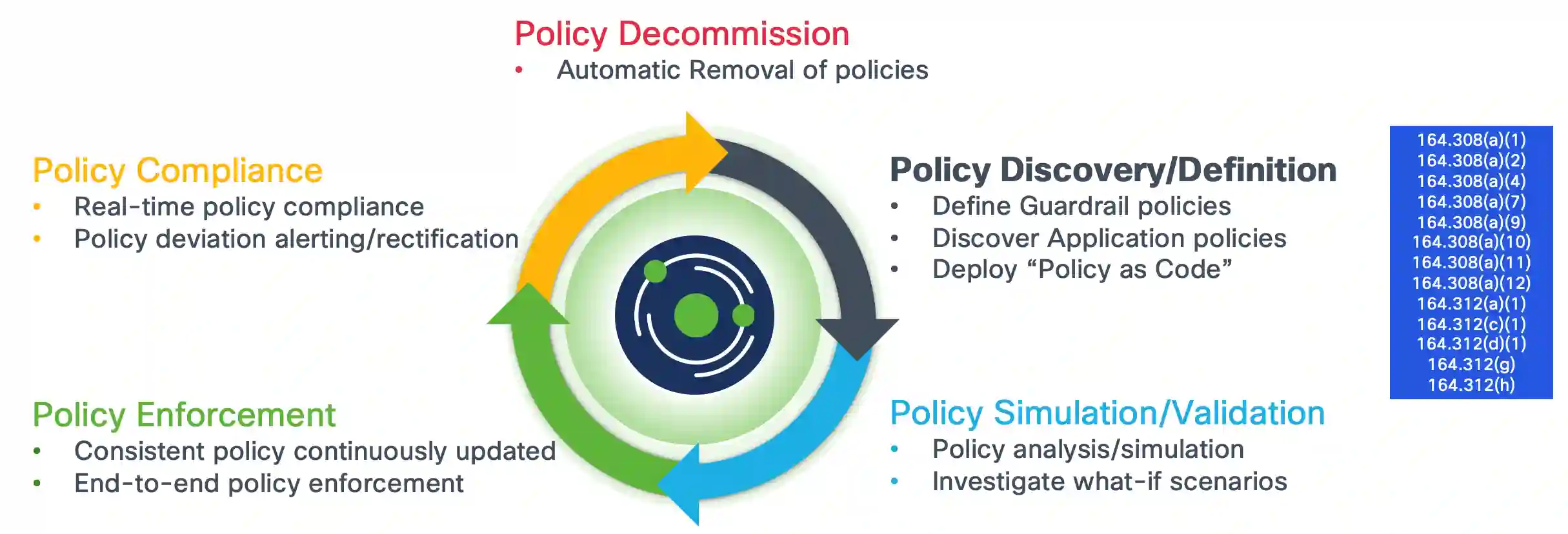
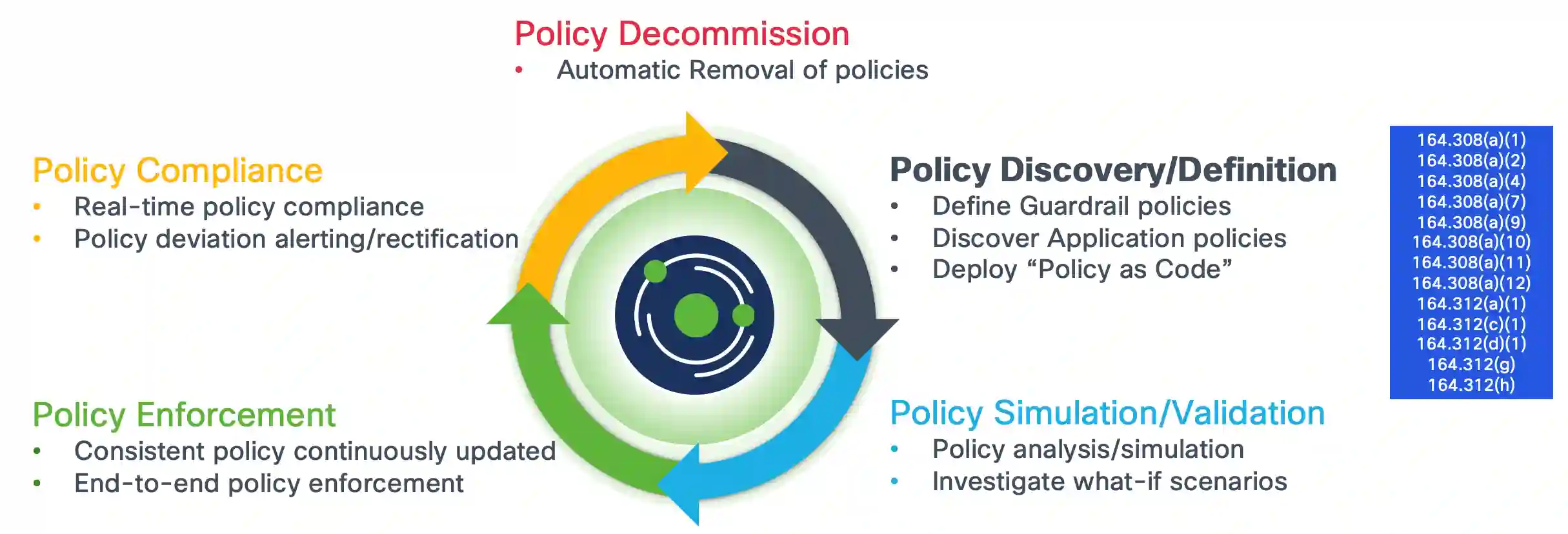
The illustration under highlights the related CFRs (Code of Federal Rules) the place Safe Workload supplies capabilities that both fulfill or complement the outlined requirements and implementation specs.
Safe Workload Key Capabilities and HIPAA Mapping:
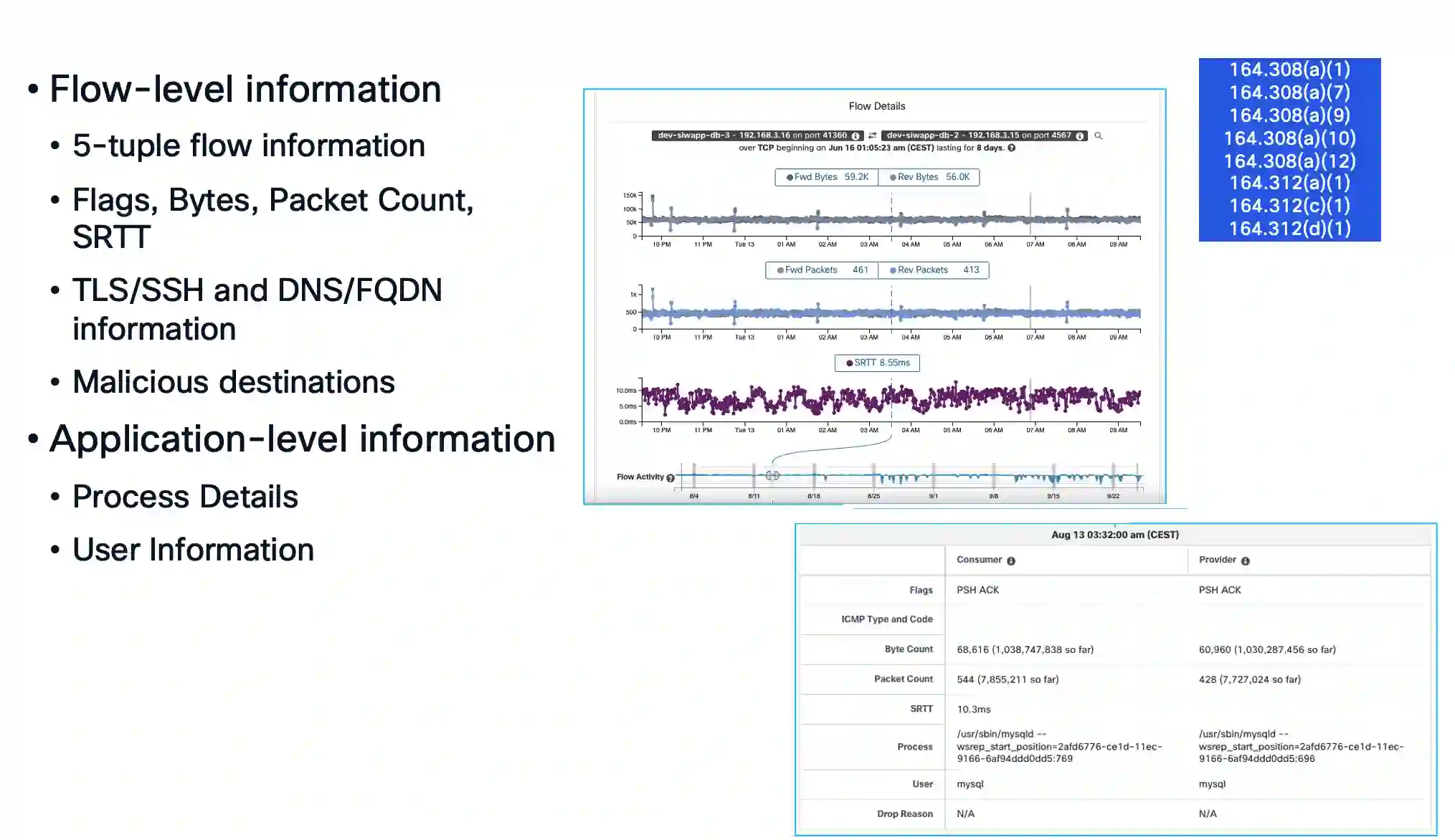
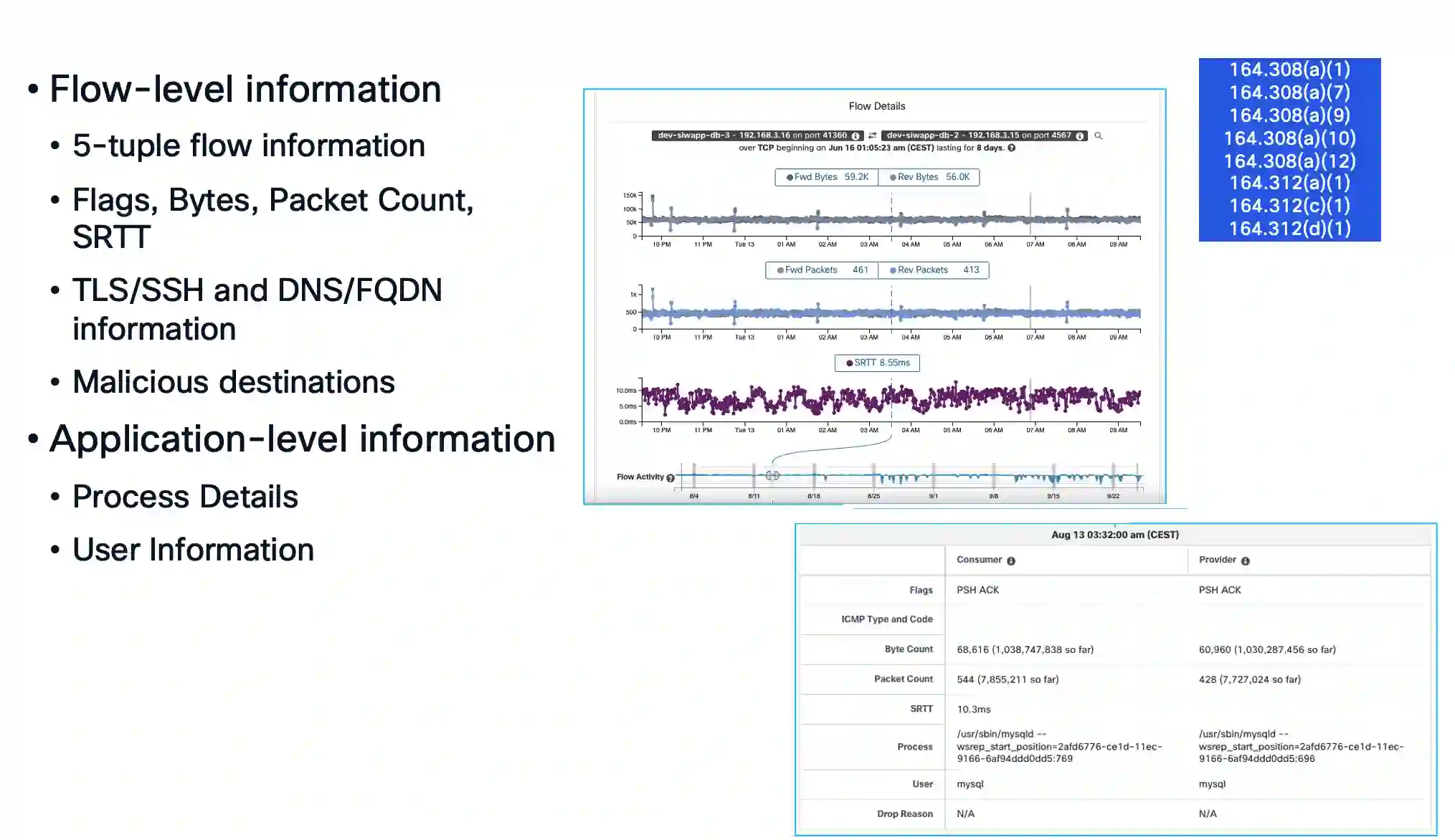
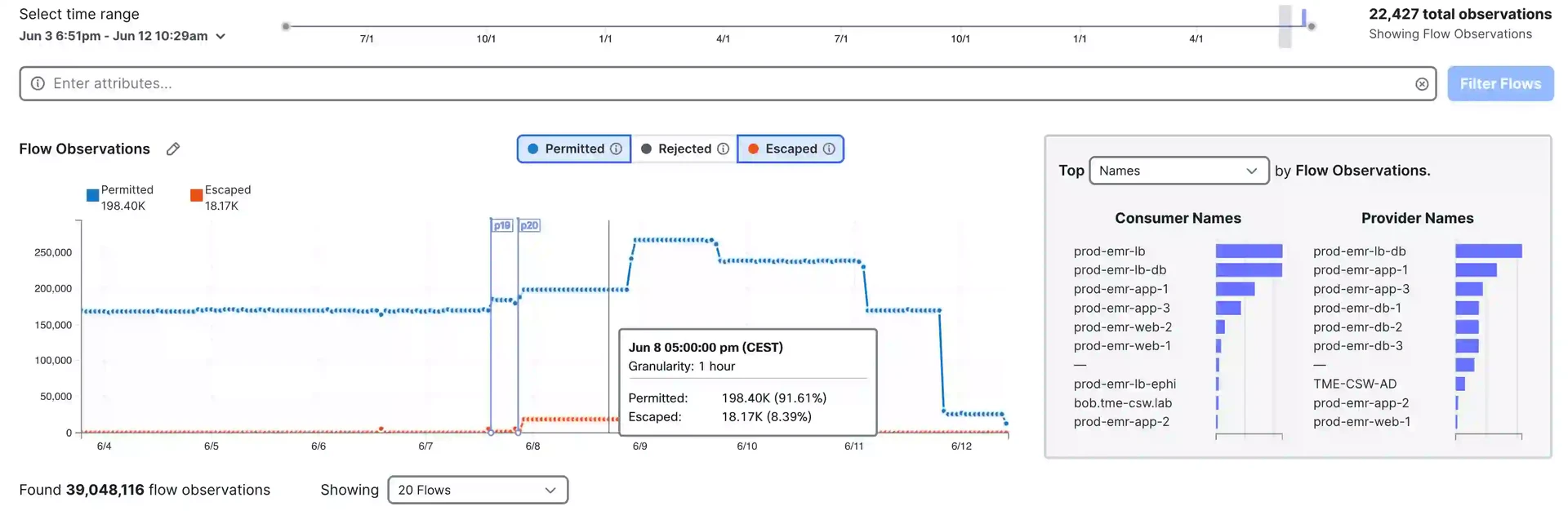
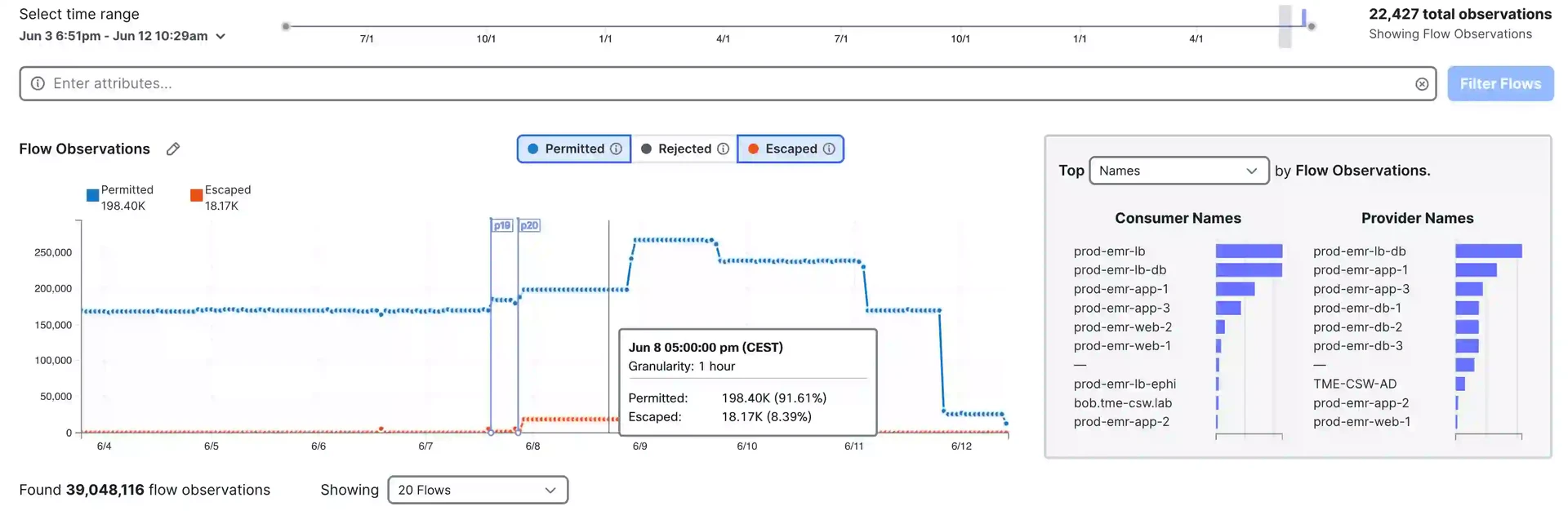
1. Utility Move Observability
Cisco Safe Workload supplies deep visibility into software workload community telemetry (e.g., 5-tuple community flows, SRTT), providing detailed stream insights reminiscent of TLS/SSH variations, algorithms, and ciphers. This helps establish weak or out of date transmission protocols—important for securing data-in-transit communications, as explicitly referenced in CFR 164.312(g). As well as, Safe Workload delivers wealthy process-level telemetry, enabling safety groups to know which processes and customers generated particular site visitors flows. This visibility empowers community and safety groups to precisely map software habits and attribute site visitors to the originating providers and processes.
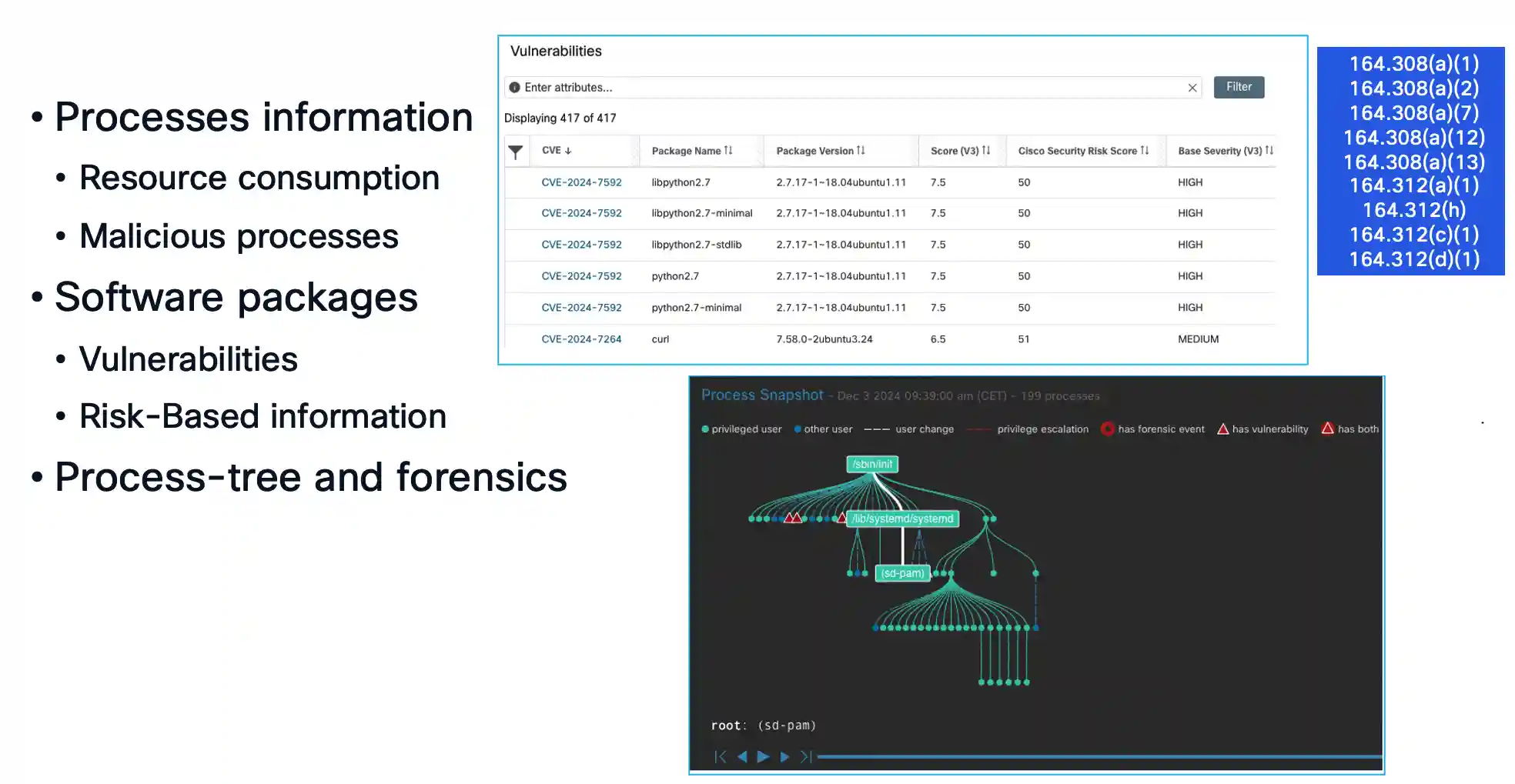
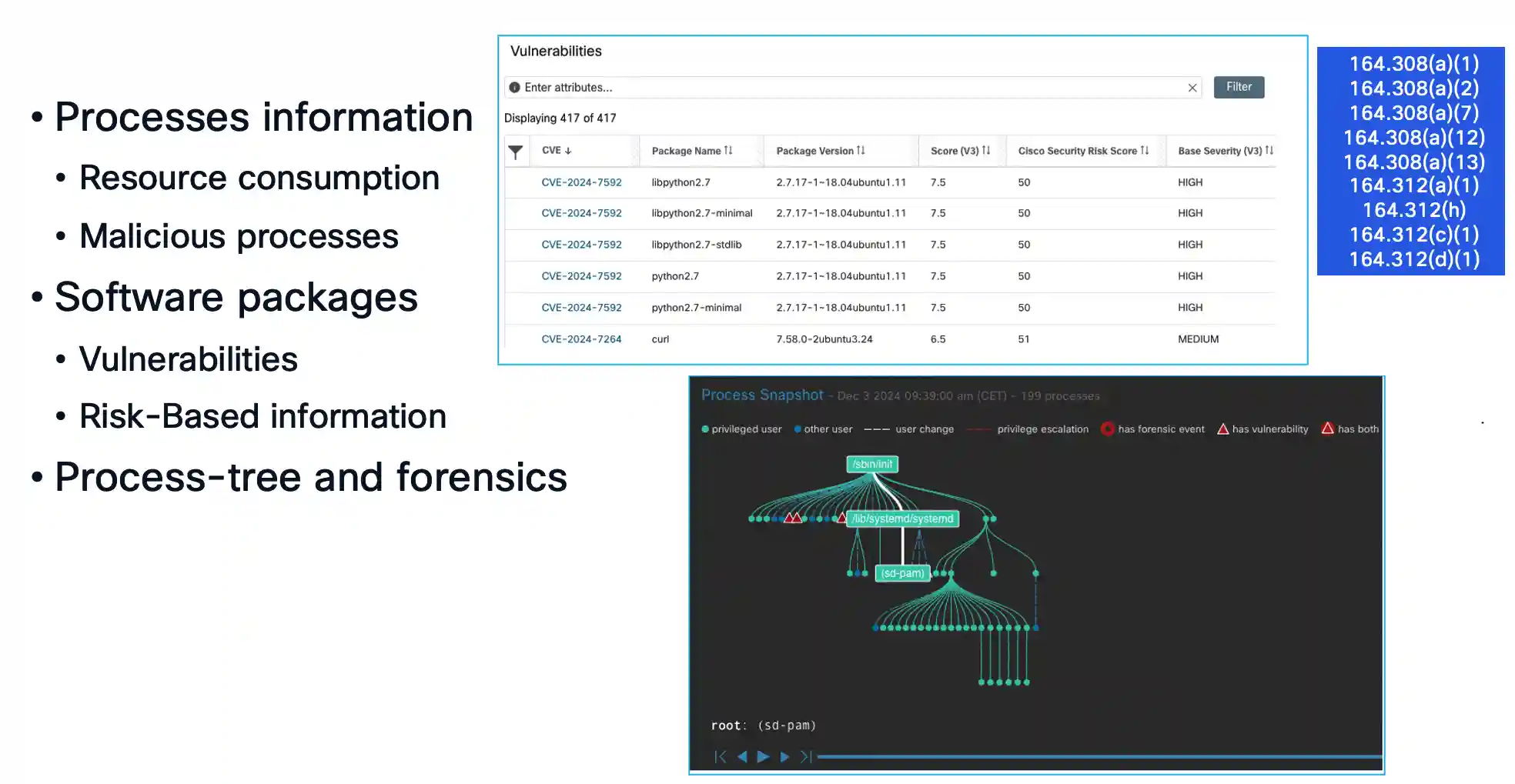
2. Workload Runtime Observability
Cisco Safe Workload supplies complete visibility into the runtime state of your workload setting. It studies key runtime metrics reminiscent of course of useful resource consumption, detection of malicious or suspicious processes, put in software program packages, recognized vulnerabilities, and their related threat ranges.
Moreover, Safe Workload allows Safety Operations groups to detect irregular habits by monitoring process-level exercise over time. These capabilities instantly help compliance with CFR 164.308(a)(7), 164.312(c)(2), 164.312(d)(2), and 164.312(h)(2).
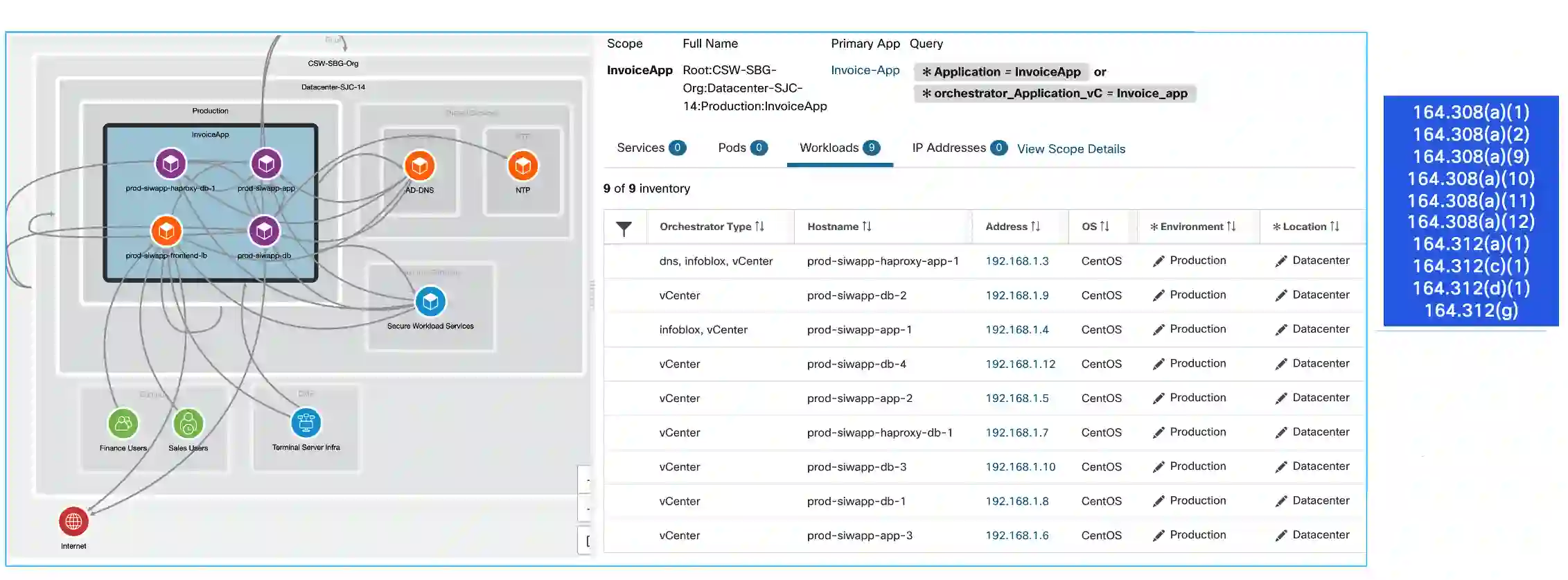
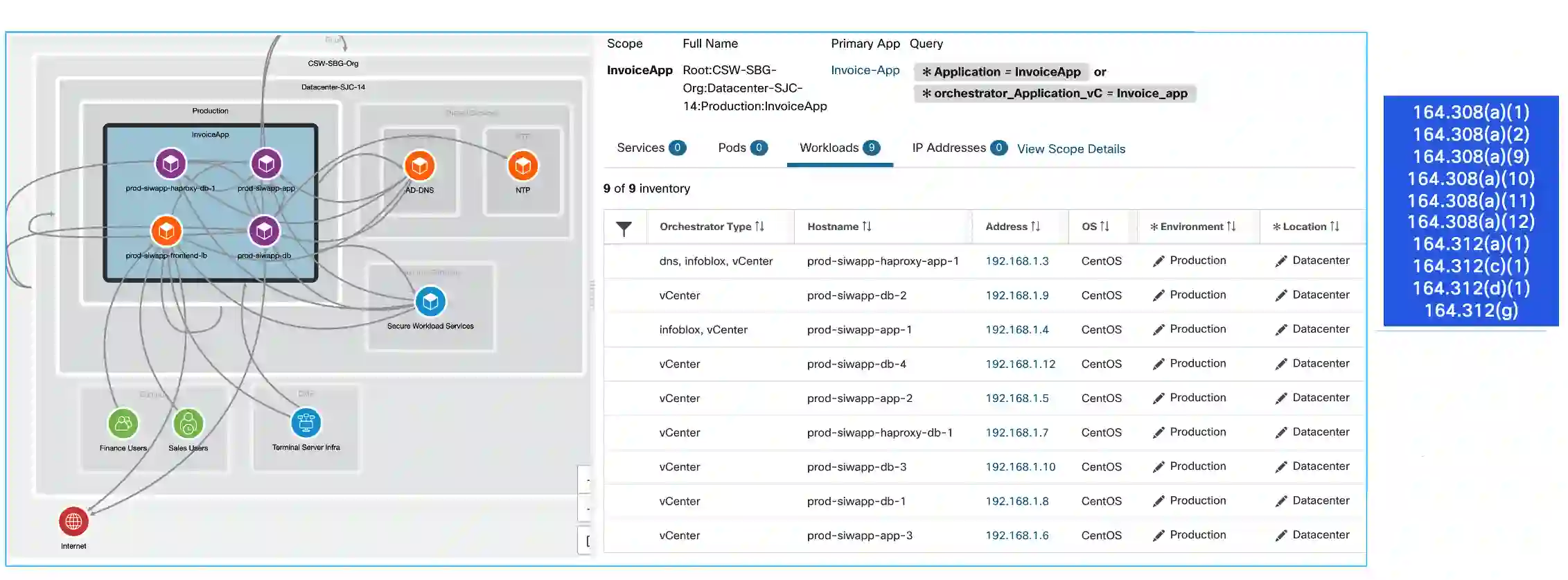
3. Utility Community Map
One of the crucial important updates within the proposed rule is the requirement to develop a community map that illustrates the motion of protected well being data (PHI) throughout techniques. That is explicitly referenced in CFR 164.308(a)(1)(B) below the Expertise Asset Stock.
This can be a core functionality of Cisco Safe Workload, which may robotically generate a community map that visualizes communication patterns between the group’s software workloads—enabling community and community safety groups to trace PHI stream and establish potential publicity factors.


4. Asset Stock
The up to date HIPAA Safety Rule locations sturdy emphasis on sustaining a complete know-how asset stock, as outlined in CFR 164.308(a)(1)(A). This requirement is foundational for monitoring techniques that deal with digital protected well being data (ePHI). Moreover, CFR 164.312(a)(1)(2) mandates that every asset be assigned a singular identifier as a part of the implementation specs.
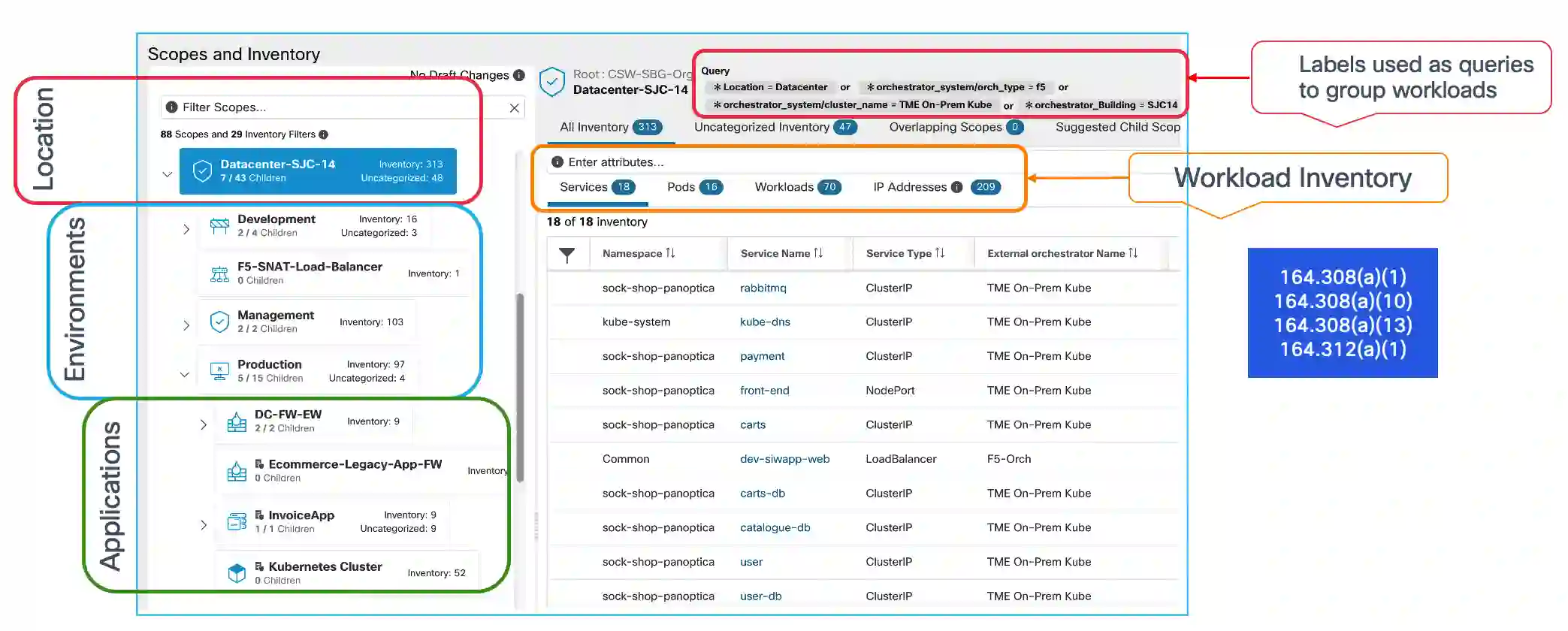
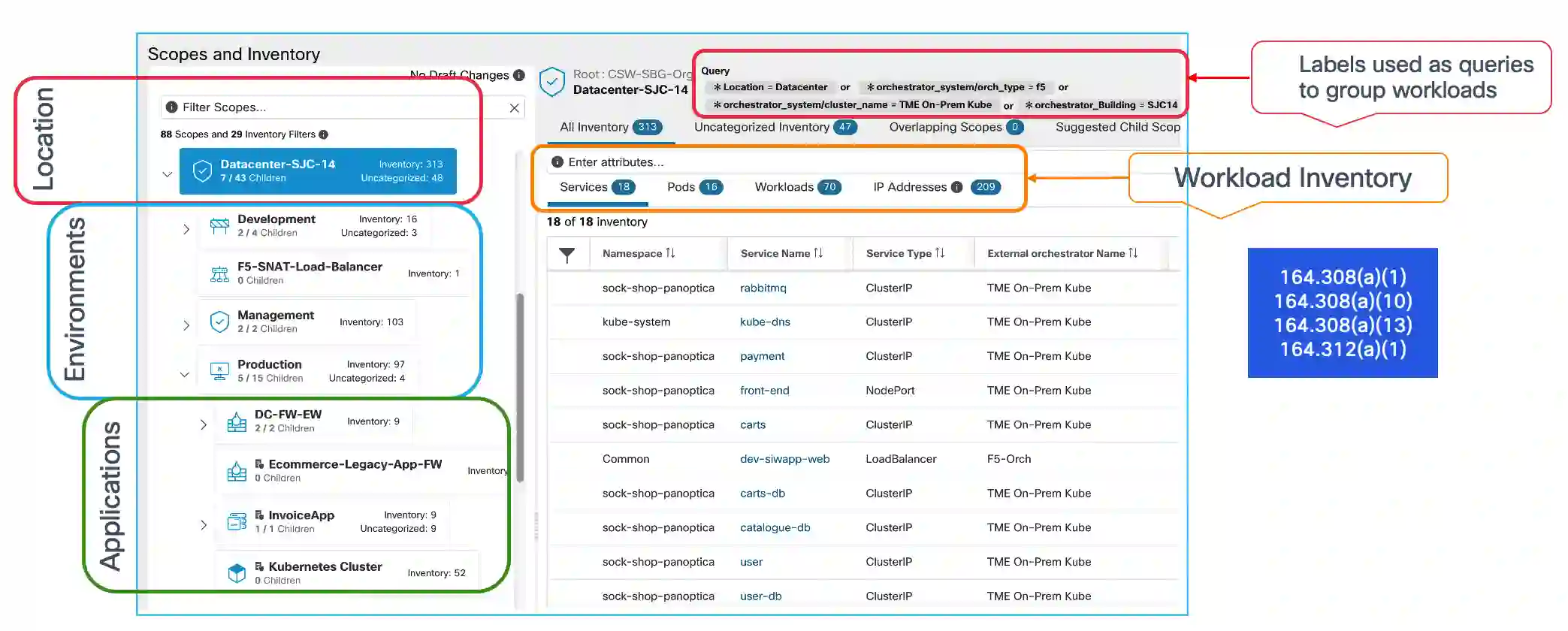
Cisco Safe Workload enhances this requirement by enabling community and safety groups to establish and label software workloads with as much as 32 customized labels instantly on the system. It additionally helps deep integration with exterior techniques of document, together with:
- Administrative Safeguard
- IPAMs (e.g., Infoblox)
- CMDBs (e.g., ServiceNow)
- Virtualization platforms (e.g., VMware vCenter)
- DNS servers
- Cloud suppliers
- Load balancers (e.g., F5, Citrix)
- Consumer and endpoint identification techniques (e.g., Cisco Safe Shopper, Cisco ISE, Lively Listing, Entra ID)
This allows organizations to construct and preserve a dynamic, real-time stock of property concerned within the dealing with of ePHI.
5. Entry Management
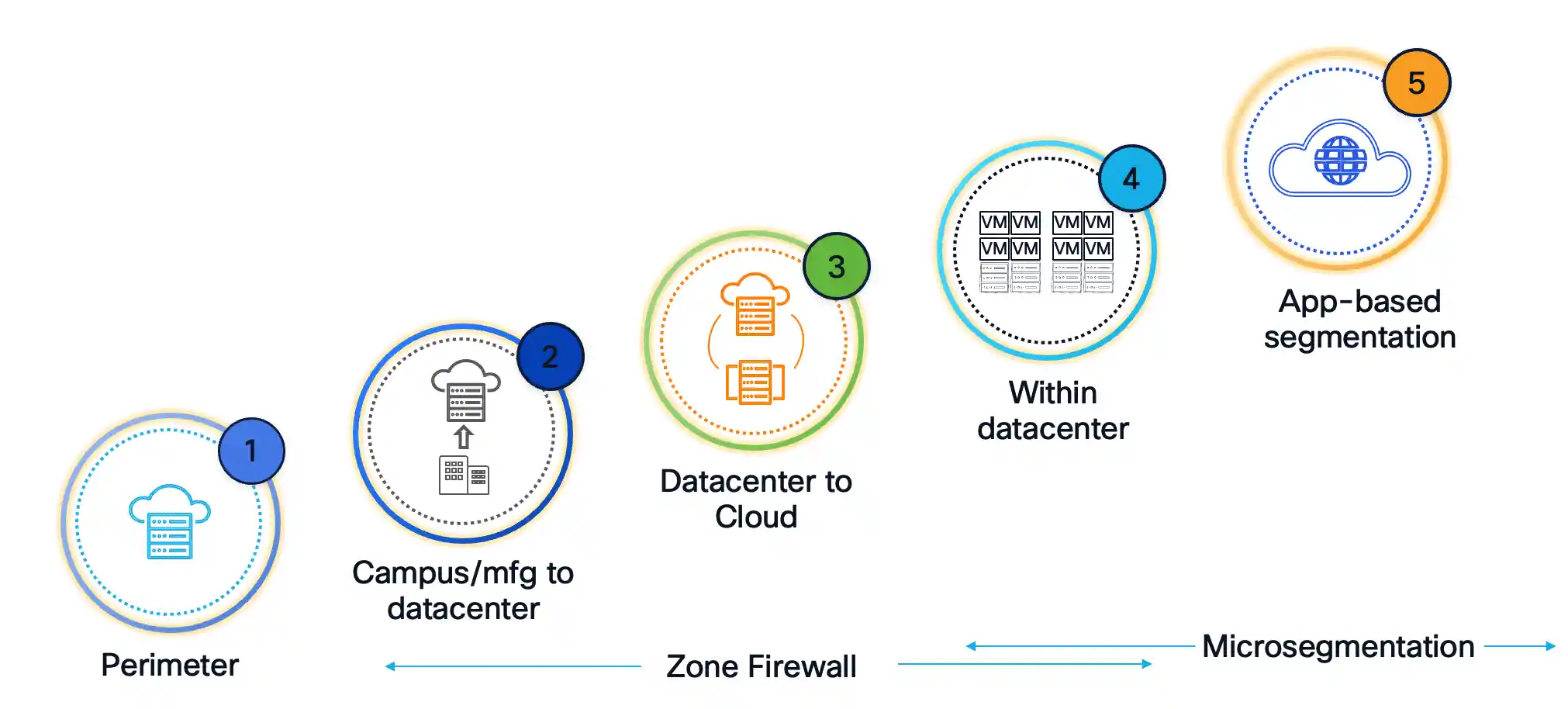
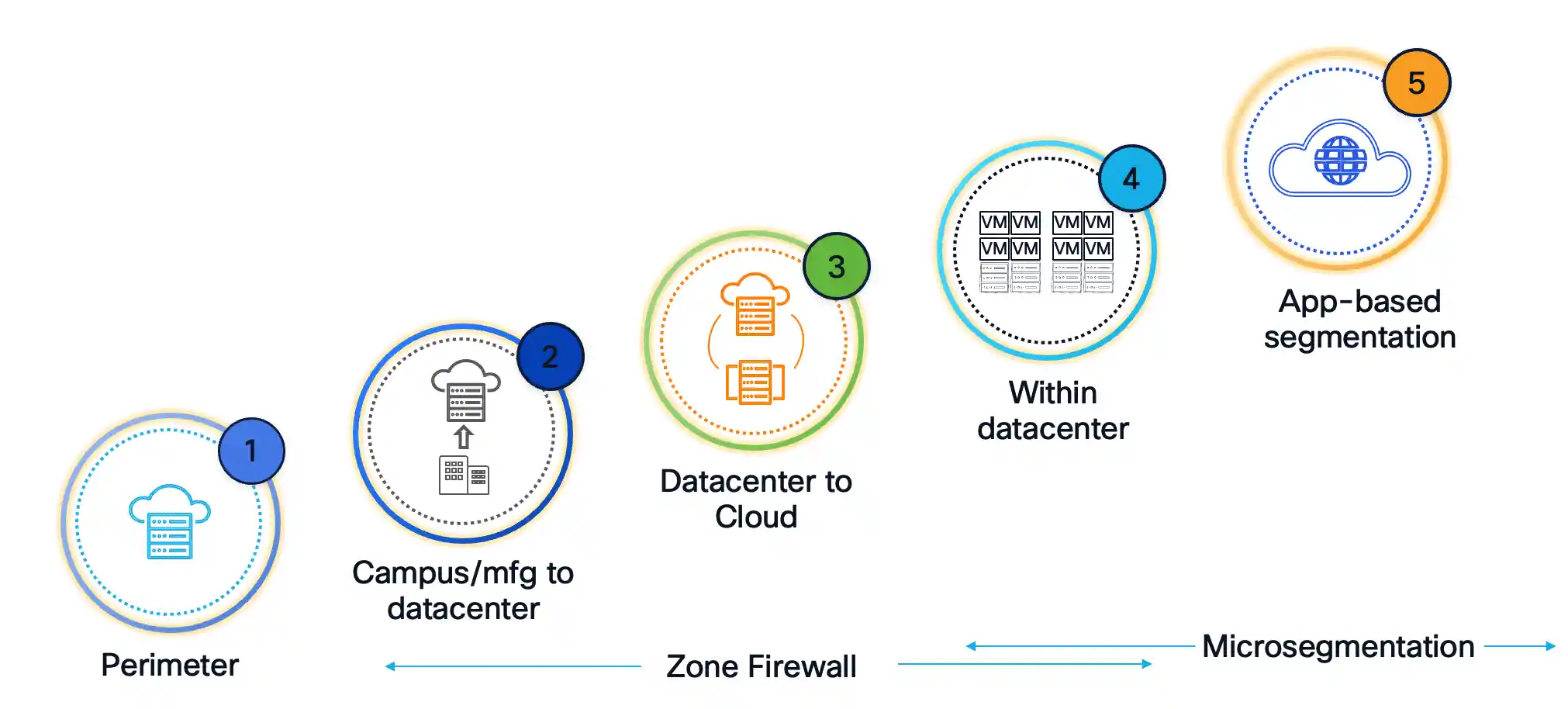
Segmentation is a key pillar within the proposed HIPAA Safety Rule Replace, emphasizing the necessity to implement community segmentation to forestall the lateral motion of malicious actors. This requirement is explicitly referenced within the implementation specification below 164.312(a)(1)(2)(vi).
Cisco Safe Workload gives versatile and adaptive segmentation capabilities, starting from macro-segmentation and zone-based firewall segmentation to micro-segmentation on the workload stage—even right down to process-level segmentation, if wanted. This method allows organizations to implement entry controls that align with their present structure whereas assembly HIPAA’s evolving safety expectations.
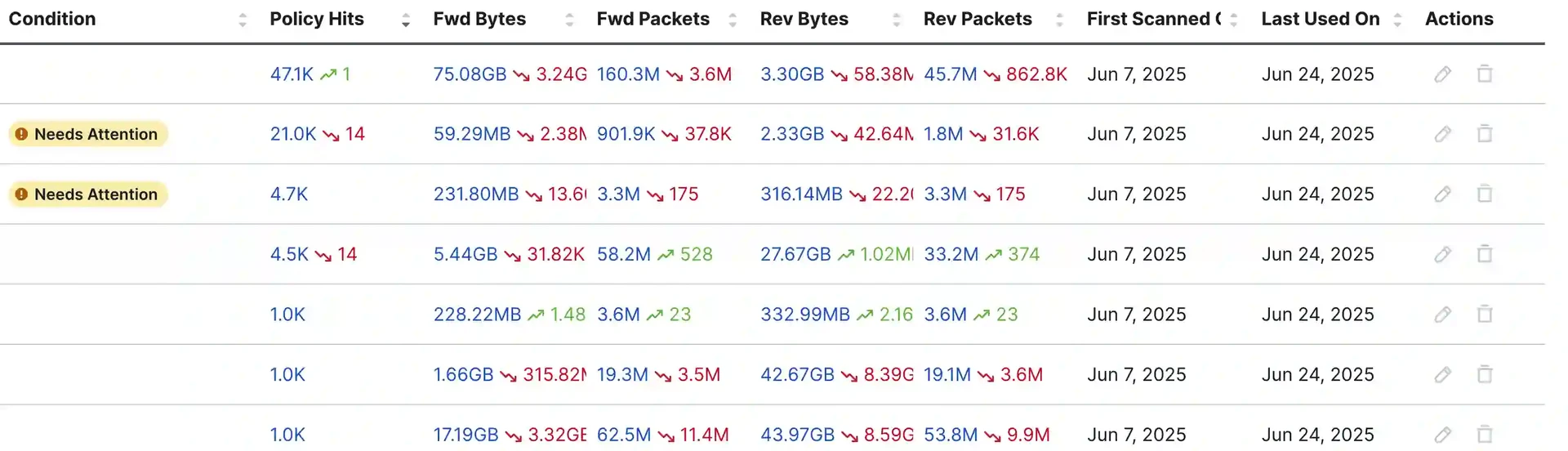
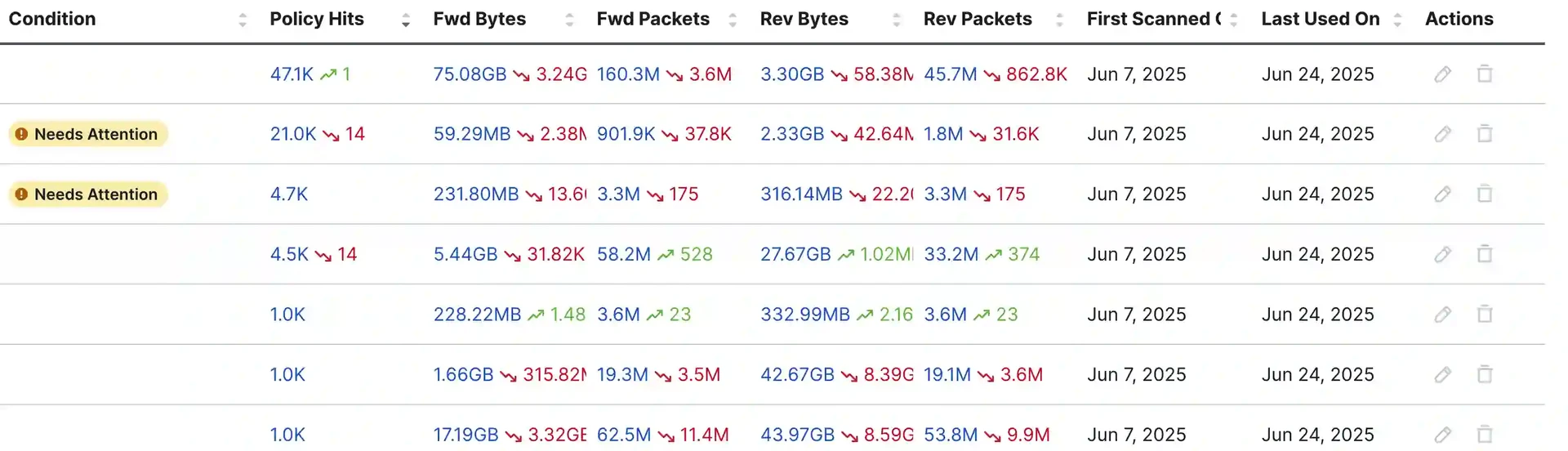
6. Coverage Lifecycle Administration
Historically, segmentation efforts have targeted on the place to implement insurance policies. Nonetheless, the true problem lies in figuring out the suitable stage of granularity and managing the whole coverage lifecycle—particularly in environments with a rising variety of coverage managers and enforcement factors.
That is the place Cisco Safe Workload really excels. Designed from the bottom as much as automate coverage lifecycle administration, it leverages a dynamic, intent-based coverage engine to outline, validate, implement, and repeatedly monitor energetic insurance policies. As soon as a coverage is not wanted, it may be cleanly decommissioned, decreasing operational overhead and minimizing threat.
7. Utility Dependency Mapping
Defining insurance policies for software workloads shouldn’t be a trivial process—particularly when community and safety groups lack visibility into software communication patterns. That’s why the Cisco Safe Workload Coverage Engine consists of software dependency mapping, which robotically discovers the communication flows and dependencies every software requires to operate.
This functionality is foundational, serving because the spine for different implementation specs. It allows the creation of a dwelling coverage that may be dynamically deployed into the community to implement efficient and correct segmentation.
8. Coverage Evaluation
Given the distributed nature of contemporary software workloads, which could be deployed at any time throughout on-premises or multi-cloud environments, it’s critically essential to know and validate coverage intent each earlier than and after enforcement.
With Coverage Evaluation, Cisco Safe Workload evaluates supposed insurance policies in opposition to actual community site visitors flows to make sure accuracy earlier than deployment and repeatedly displays compliance after enforcement.
Moreover, Safe Workload options an AI-driven coverage engine that gives deep insights into the dwelling coverage state, together with:
- Coverage traits
- Anomalies or circumstances that require consideration (e.g. coverage overshadowing, overly broad guidelines)
This helps safety groups refine coverage definitions and preserve exact, risk-aligned enforcement throughout dynamic environments.
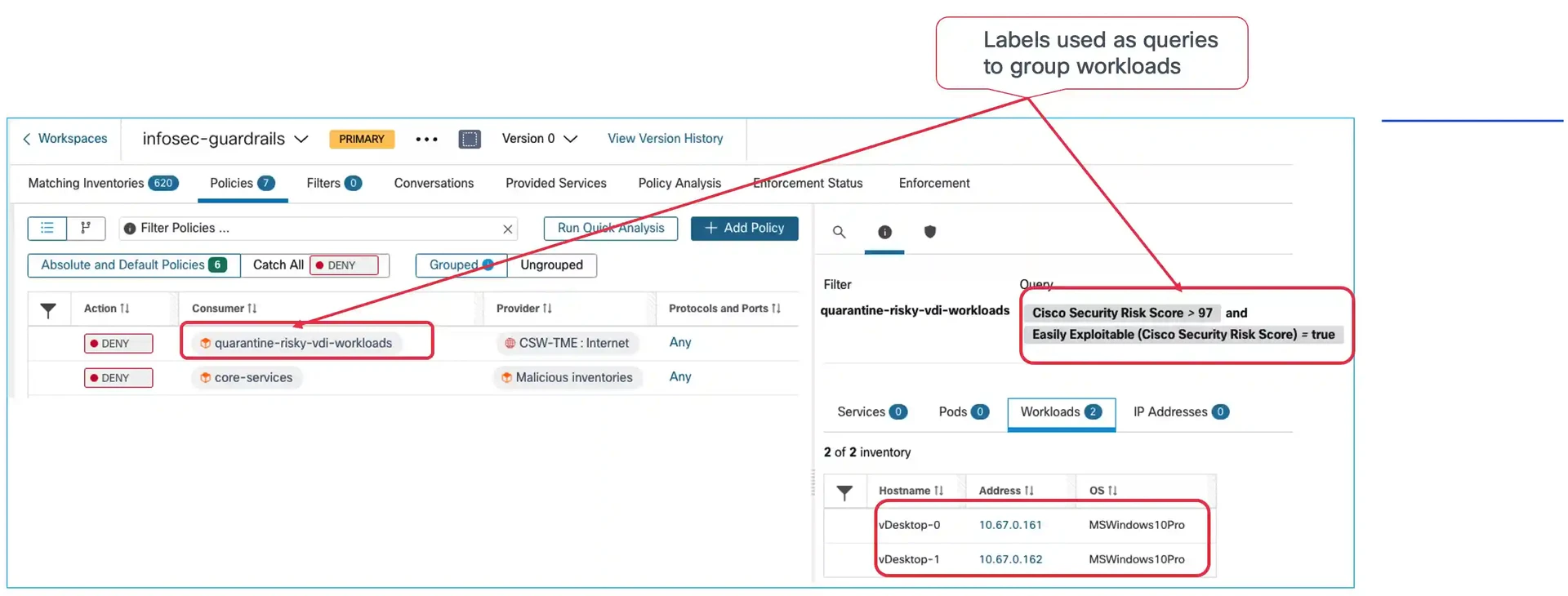
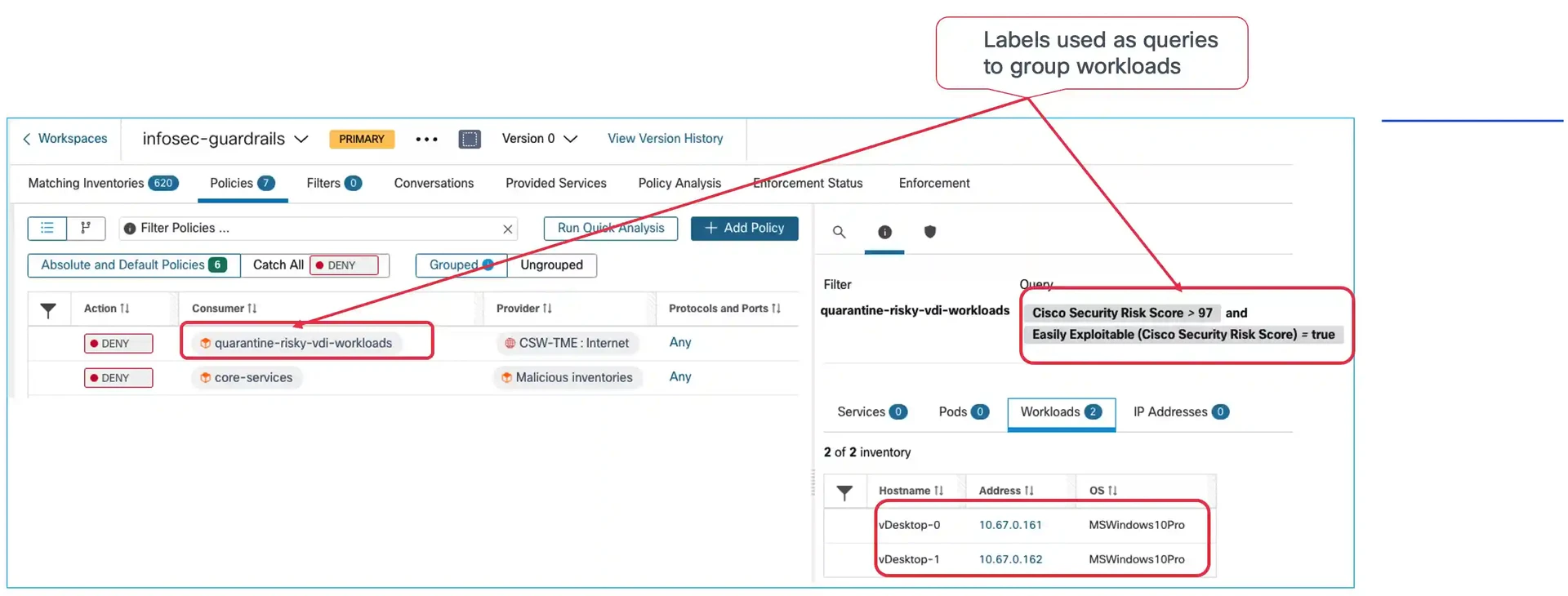
9. Quarantine/Blast-Radius Competition
CFR 164.308(a)(12)(B) —below the Safety Incident Procedures customary—requires organizations to have the potential to reply to safety incidents successfully. Cisco Safe Workload allows speedy threat mitigation in important eventualities. For instance, if a high-risk vulnerability is found, particular workloads could be swiftly quarantined from the community. Within the case of a ransomware outbreak, Safe Workload permits groups to shortly isolate affected workloads, containing the blast radius and stopping lateral motion throughout the setting.
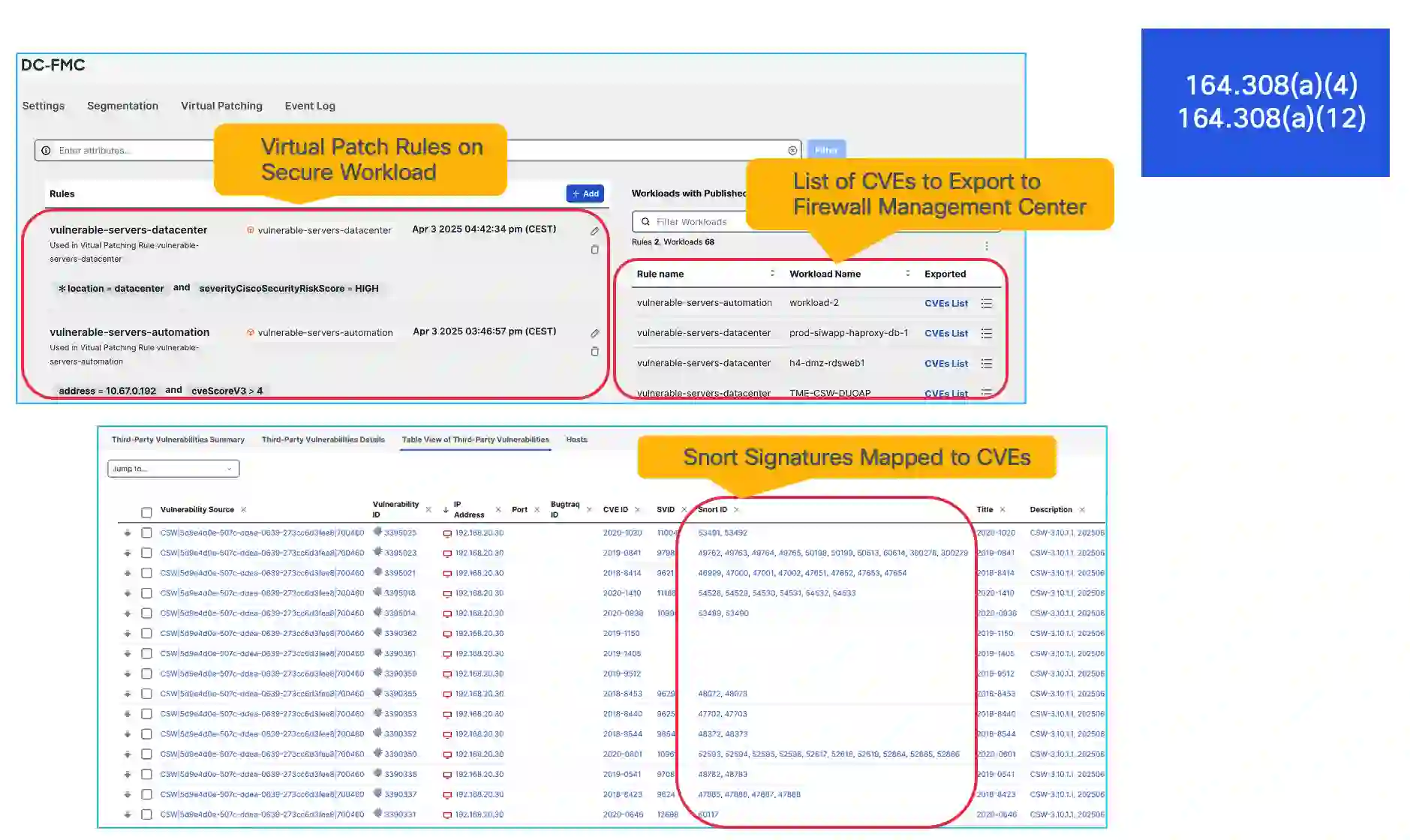
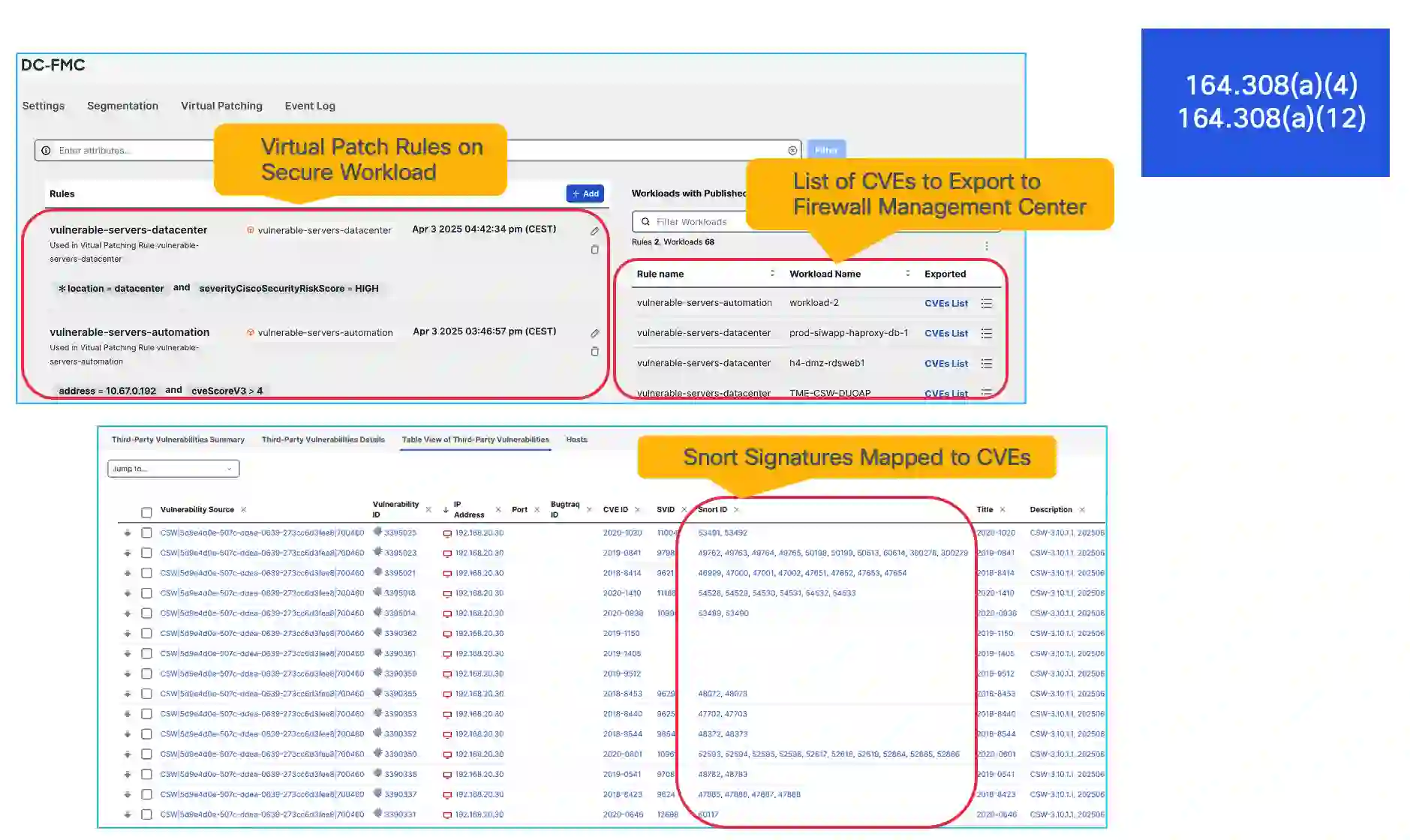
10. Compensating Controls
In each group, there are conditions the place sure dangers can’t be instantly mitigated, or the place an alternate technique of threat discount is important. CFR 164.308(a)(4) particularly highlights the significance of patch administration in such circumstances. Whereas Cisco Safe Workload shouldn’t be a patching or vulnerability administration instrument, it may well complement this customary by leveraging vulnerability knowledge from workloads and integrating with Cisco Safe Firewall Administration Middle. This integration allows the automated deployment of applicable IPS guidelines to assist defend in opposition to recognized vulnerabilities and potential exploits—appearing as an efficient compensating management when patching shouldn’t be instantly possible.
Turning Compliance into Significant Outcomes with Cisco Safe Workload
Though the up to date HIPAA Safety Rule has but to take impact, now’s the time for regulated entities to proactively assess their safety posture and readiness. Navigating evolving compliance necessities doesn’t need to be complicated—with the suitable instruments; it turns into a strategic benefit.
Cisco Safe Workload empowers your group to implement clever, policy-driven segmentation of software workloads, serving to you align with upcoming HIPAA mandates and preserve a resilient, compliant safety framework.
Need to be taught extra? Go to the Cisco Safe Workload product web page.
We’d love to listen to what you assume! Ask a query and keep linked with Cisco Safety on social media.
Cisco Safety Social Media
Share:


