Cybercriminals impersonate the trusted e-signature model and ship faux Docusign notifications to trick folks into freely giving their private or company knowledge
27 Might 2025
•
,
5 min. learn

Bear in mind once you used to need to print, signal, scan, electronic mail and/and even fax each time you wished to signal and ship an official doc? At this time, a lot of the exhausting work is finished behind the scenes by cloud app suppliers like Docusign.
However like all tech manufacturers, as soon as it has reached a important mass of customers, cybercriminals will search for methods to abuse it for their very own ends. Docusign claims to have 1.6 million clients world wide, together with 95% of the Fortune 500, and over one billion customers. That has put it firmly within the crosshairs of menace actors. Learn on to know find out how to hold your workers secure from Docusign-themed phishing.
How does Docusign phishing work?
Social engineering is among the largest threats to your online business. Based on Verizon, phishing is now an preliminary entry vector for 19% of knowledge breaches, whereas a whopping 60% function a “human aspect.” As a trusted and widely known model, Docusign is a pure selection for menace actors trying to harvest company logins and probably monetize assaults in different methods.
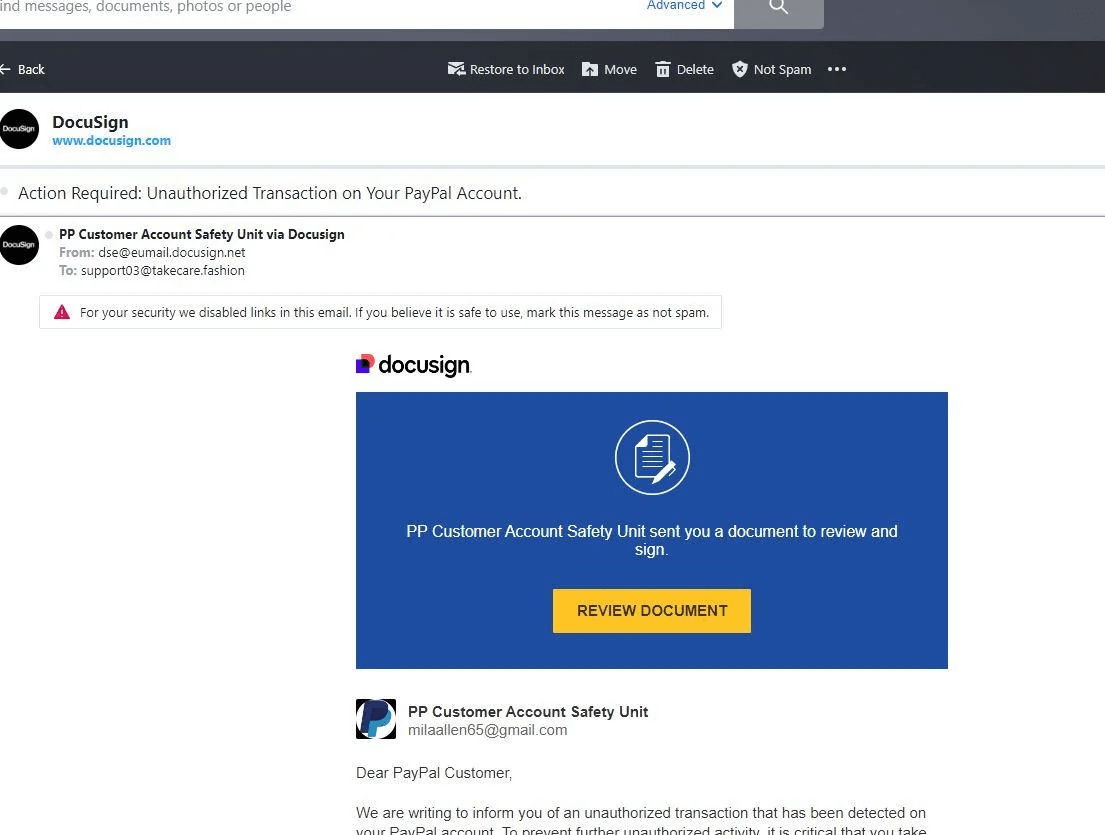
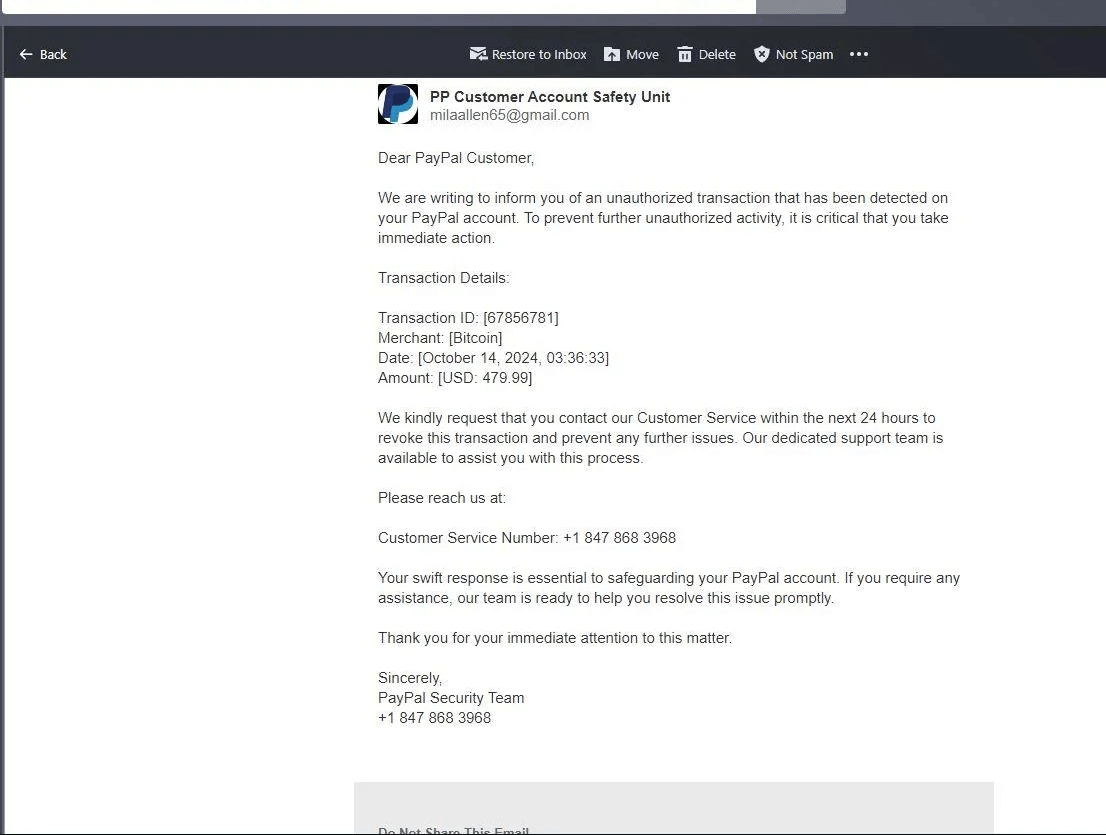
Victims will sometimes obtain an electronic mail with a spoofed Docusign “envelope” requesting that they click on on a big yellow field to “overview doc.” There may additionally be an attachment that includes a QR code. Each actions may result in the identical consequence: the sufferer is taken to a phishing web site comparable to a faux Microsoft login web page, and requested to enter private and/or monetary info.
QR codes are additionally standard as they require the person to scan with their cell system, which can not have safety software program put in to forestall them from being taken to a malicious web page. Both method, a focused phishing assault like this might additionally allow menace actors to achieve a vital foothold in company networks, in addition to for privilege escalation, lateral motion and knowledge exfiltration/ransomware.
Some examples
Over the previous few months, incidents have emerged of:
- “Official” Docusign envelopes that spoof invoices from suppliers, in a bid to trick corporations into transferring cash.
- Faux bill scams impersonating US state and municipal businesses and designed to trick suppliers into wiring cash.
- Cybercriminals should not spoofing faux Docusign emails, however as a substitute registering actual accounts with the corporate, and utilizing its APIs to ship out official envelopes spoofing standard manufacturers.
- Common phishing emails spoofing the Docusign model and taking the person to phishing login pages. These may mimic company HR and payroll departments, and even exterior entities like municipal authorities.
- Refund scams which cite a faux transaction and attempt to pressure the sufferer into calling a quantity in the event that they need to cancel it. As soon as on the telephone, they’ll be persuaded at hand over their private/monetary/card particulars to assert the ‘refund’.
Instance of a rip-off abusing folks’s belief in Docusign for knowledge theft (Supply: Reddit)
Staying secure
Happily, there’s lots you are able to do to maintain your self and your organization secure from Docusign threats. From an organization’s perspective, the primary plan of action is to pay attention to the dangers and replace your phishing consciousness packages to make sure workers are capable of spot the warning indicators of a rip-off electronic mail. Simulation instruments needs to be customizable sufficient to assist this.
Issues employees needs to be taught to look out for embrace:
- Vacation spot URLs: hover over any hyperlinks/buttons in Docusign emails to examine the vacation spot URLs are official.
- Safety codes: these ought to function on any official Docusign electronic mail (within the “alternate check in methodology” part) and permit the person to entry a doc immediately on the Docusign web site moderately than comply with hyperlinks in an electronic mail.
- Attachments: there needs to be no attachments in an preliminary Docusign electronic mail. Solely as soon as a doc has been signed will you obtain a completed model of it by way of attachment.
- Spelling, grammatical and tonal errors: are one other tell-tale signal of a phishing electronic mail.
- An electronic mail signature and sender identify/electronic mail handle that don’t match.
Layer up defenses on high of the safety consciousness piece by together with issues like:
- Multi-factor authentication (MFA) for all company accounts, which can make it more durable for hackers to entry your knowledge, even when they do handle to steal your logins.
- Password hygiene, together with use of sturdy, distinctive passwords for every account, saved in a password supervisor.
- A multi-layered safety instrument from a good vendor like ESET, which, amongst different issues, detects malicious attachments, prevents customers from following hyperlinks to phishing websites, and permits directors to manually outline electronic mail filtering situations and actions.
- Up to date coverage to induce customers to not open attachments or comply with hyperlinks in any unsolicited emails, and solely entry Docusign docs by way of the safety code.
- Altering inner enterprise processes relating to fund transfers, in order that any massive sums are topic to further scrutiny.
- Encouraging customers to report all suspicious Docusign-themed emails to your IT/safety staff and to [email protected].
What to do should you fall sufferer
If the worst occurs and an worker does click on via on a Docusign rip-off, you as an admin might want to work via a particular set of actions, together with:
- Reset passwords for the impacted person, together with any accounts that they might have reused credentials throughout
- Run a malware scan on the sufferer’s machine to detect and take away any malicious code
- Isolate the system from the community to comprise the “blast radius” of an assault
- Monitor the darkish net for indicators of knowledge theft/leakage
- Monitor the sufferer’s accounts for uncommon exercise
- Dig deeper with forensics to know what the attacker wished and whether or not they managed to achieve elevated inner entry
- Use the occasion as a studying second for workers: encouraging them to report suspicious emails quickly and to be on their guard typically about unsolicited emails
After all, Docusign isn’t simply utilized by companies. You may need been uncovered to it in a private capability when shopping for a home or finishing tax paperwork. In that case, most of the ideas above will nonetheless stand you in good stead. Digital signing apps are a terrific time-saver. However be sure you don’t get caught out by scammers exploiting your belief in these apps.