Lengthy missed as a risk floor, many organizations have turn into more and more involved about their community infrastructure and attackers utilizing these gadgets together with residing off the land (LOTL) strategies to perform their numerous nefarious targets: A kind of actors, dubbed Salt Hurricane, made headlines earlier this 12 months and introduced this usually uncared for risk floor to the forefront in lots of peoples’ minds.
The Cisco Talos evaluation of Salt Hurricane noticed that the risk actors, usually utilizing legitimate stolen credentials, accessed core networking infrastructure in a number of cases after which used that infrastructure to gather a wide range of info, leveraging LOTL strategies. A few of the suggestions to detect and/or defend your environments embrace:
- Monitor your atmosphere for uncommon adjustments in conduct or configuration.
- Profile (fingerprint by way of NetFlow and port scanning) community gadgets for a shift in floor view, together with new ports opening/closing and site visitors to/from (not traversing).
- The place potential, develop NetFlow visibility to establish uncommon volumetric adjustments.
- Encrypt all monitoring and configuration site visitors (SNMPv3, HTTPS, SSH, NETCONF, RESTCONF).
- Stop and monitor for publicity of administrative or uncommon interfaces (e.g., SNMP, SSH, HTTP(s)).
Beneath, we are going to look at how a few of these monitoring and detection actions may be achieved with Cisco Safe Community Analytics (SNA).
Community Risk Detection with Cisco Safe Community Analytics
By means of the gathering of community metadata, predominately NetFlow/IPFIX, Cisco SNA offers enterprise-wide community visibility and behavioral analytics to detect anomalies indicative of risk actor exercise, such because the LOTL strategies utilized by a few of these refined risk actors. With slightly tuning and a few customization, the analytics and risk detections may be made to reliably establish risk actors misusing community gear.
In tuning SNA for some of these detections, we’re going to do three main duties:
- Configure Host Teams for Infrastructure
- Create Customized Safety Occasions and Position Insurance policies
- Create a Community Diagram for Monitoring
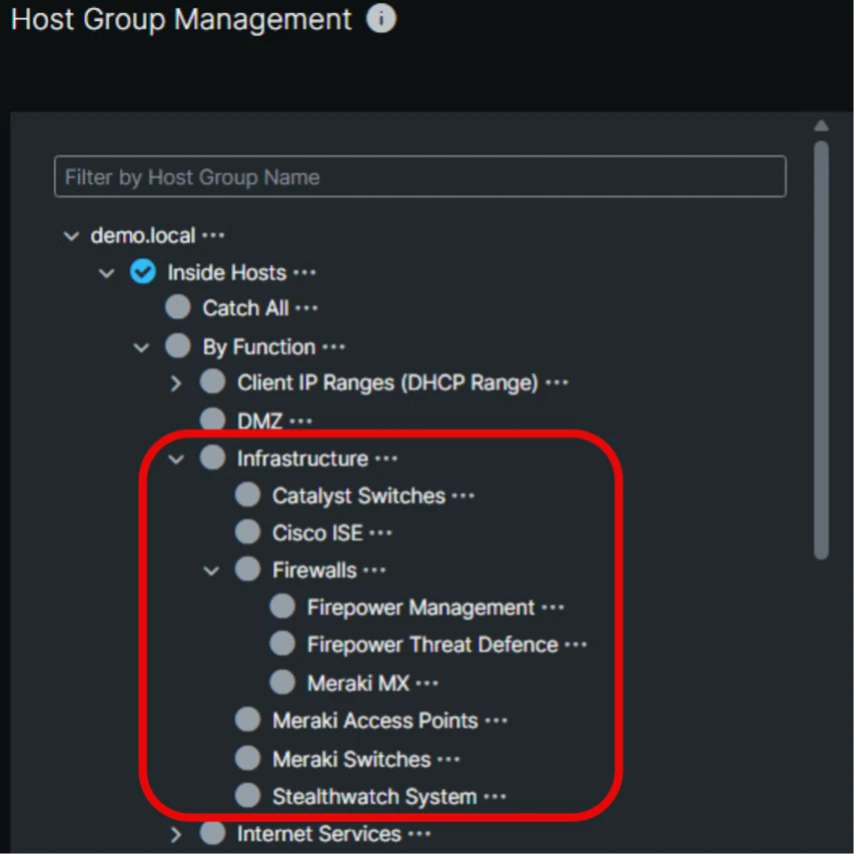
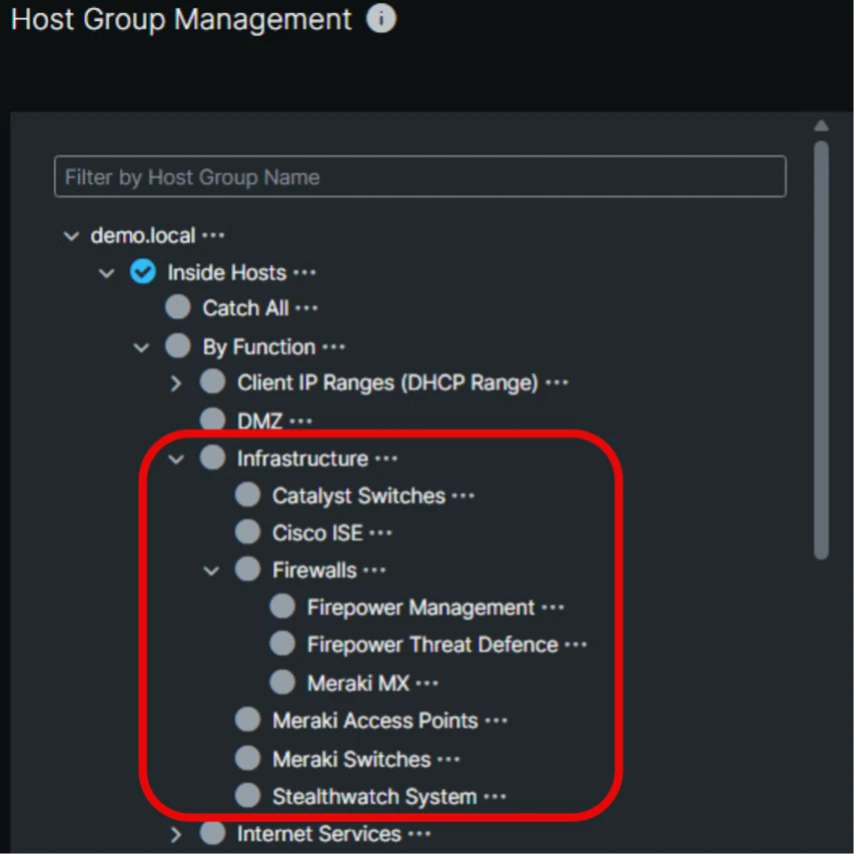
1. Configure Host Teams for Infrastructure
- Outline Host Teams in SNA to categorize your community infrastructure gadgets comparable to routers, switches, and bounce hosts. This grouping permits centered monitoring and simpler identification of suspicious communications involving essential infrastructure.
2. Create Customized Safety Occasions and Position Insurance policies
- Leverage risk intelligence from Cisco Talos, together with indicators of compromise (IOCs) and behavioral patterns described within the Salt Hurricane evaluation.
- Construct Customized Safety Occasions in SNA to detect suspicious or forbidden communications, comparable to uncommon or forbidden site visitors patterns. Examples embrace monitoring for workers connecting to the infrastructure host teams, the usage of deprecated administration protocols comparable to telnet and suspicious communication between community administration planes (ex. SSH classes between switches).
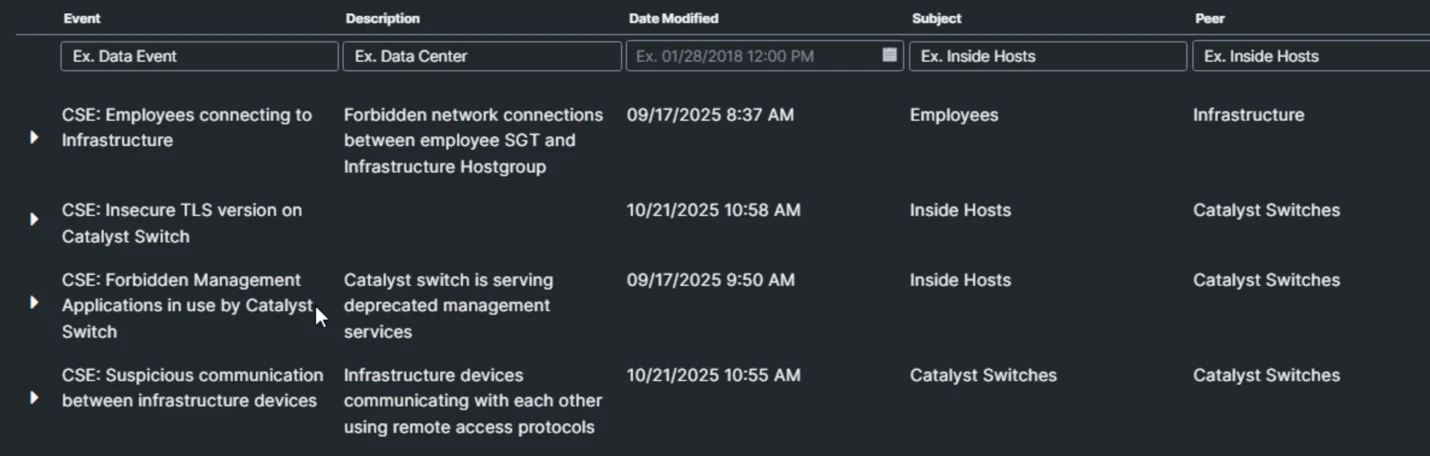
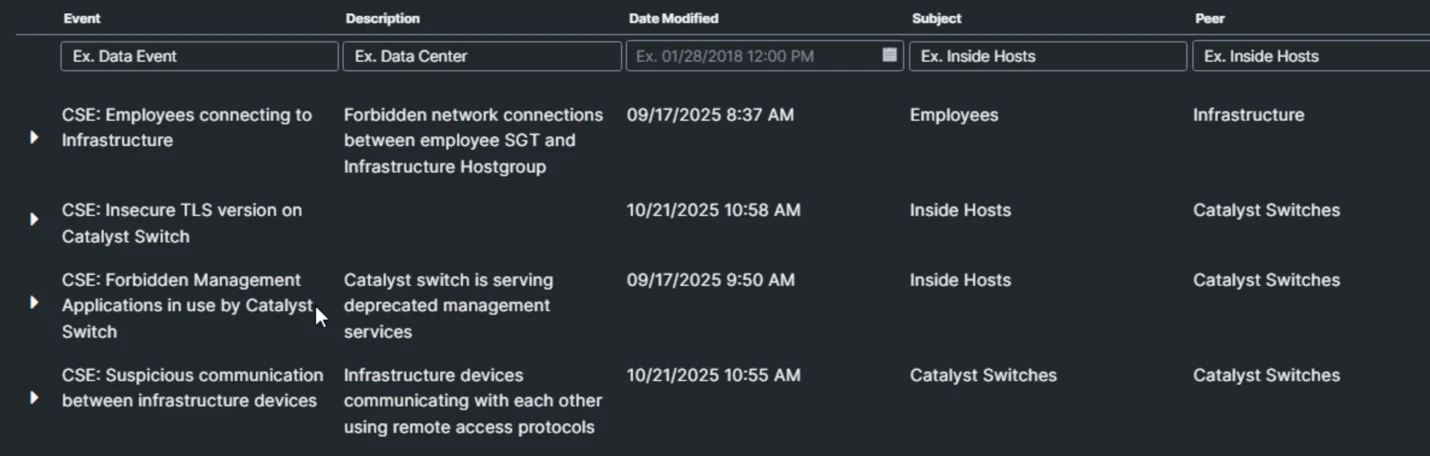
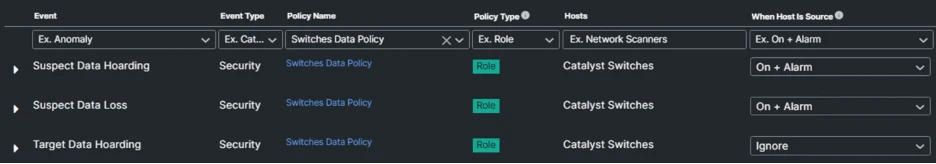
- Outline Position Insurance policies to additional tune the core occasions to higher detect suspicious and/or anomalous exercise by swap administration that will point out lateral motion, information hoarding, and/or exfiltration.
3. Develop a Community Diagram for Monitoring
- Use SNA’s community diagram characteristic to create a community topology visualization to simulate an in depth diagram of your infrastructure hosts and their communication paths. This visible assist helps in shortly recognizing anomalous lateral actions or sudden information flows involving bounce hosts or infrastructure gadgets.


Monitoring for Risk Actor Exercise
Now that we’ve tooled a number of the detection system, we start energetic monitoring. Keep in mind that at any time you may at all times return and tweak the customized safety occasions or modify the alarm thresholds within the function coverage to higher monitor your atmosphere. In the end, when monitoring for the LOTL exercise expressed by these risk actors, we’re watching community administration airplane site visitors and/or different (usually unmonitored) infrastructure gadgets for suspicious and/or malicious seeming exercise. It’s at all times value noting that your individual safety coverage can have important affect on what is set to be suspicious and/or malicious.
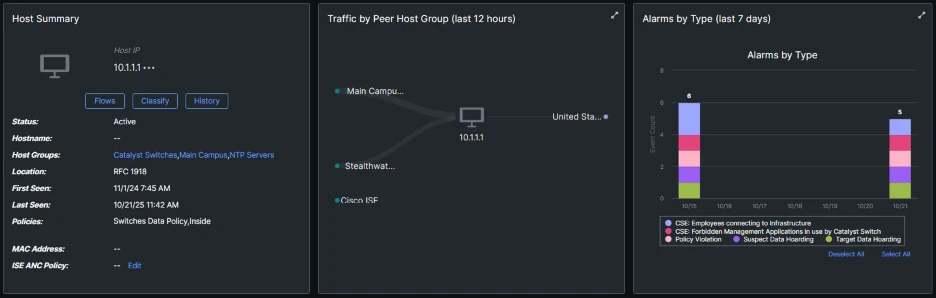
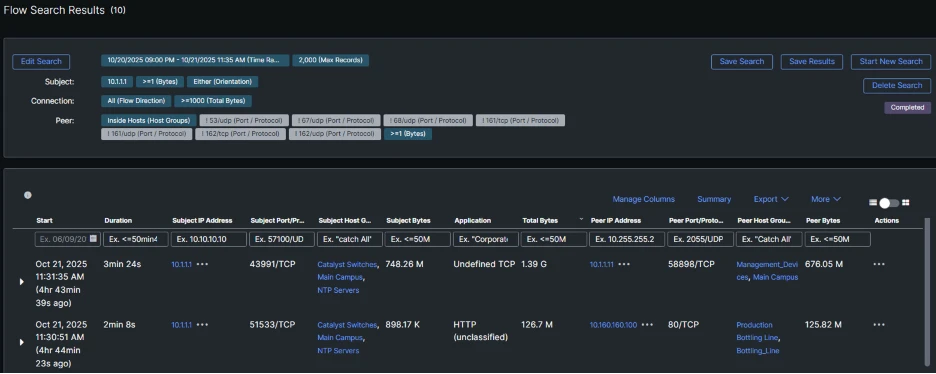
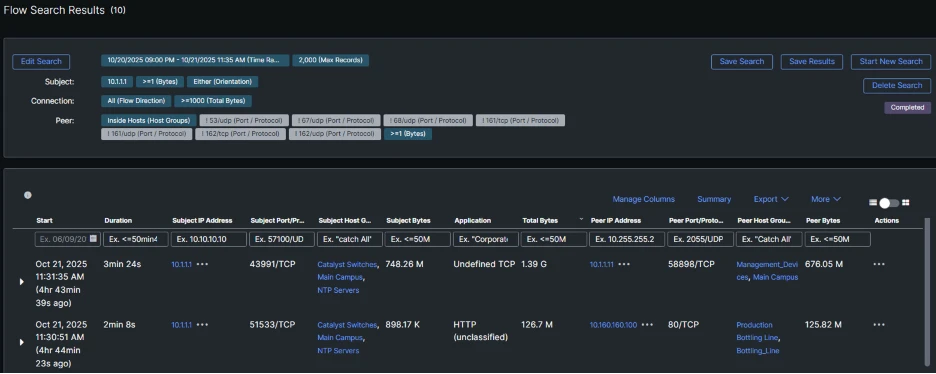
When Alarms happen, you may view them within the host web page: within the instance beneath, the host [10.1.1.1] belonging to the host group Catalyst Switches has expressed quite a few coverage violations: the customized safety occasions above in addition to Information Hoarding (gathering loads of information from an inside system) and Goal Information Hoarding (sending massive quantities of information to a different system), indicating {that a} malicious actor is remotely accessing this system and utilizing its administration airplane to obtain and ahead site visitors.
Digging into the movement data for the safety occasions related to the above swap confirms that it downloaded a considerable amount of information from the Bottling Line and uploaded it to an unmonitored administration desktop.
Conclusion
With some intelligent tooling, Cisco SNA may be successfully used to monitor infrastructure and, by the evaluation of community conduct evaluation, detect refined risk actors within the atmosphere. Forms of residing of the land strategies SNA may be efficient at detecting on infrastructure embrace:
- Unauthorized or suspicious logins to community gadgets.
- Suspicious lateral motion between infrastructure hosts.
- Information hoarding, forwarding and different uncommon information flows.
- Information exfiltration makes an attempt by unmonitored hosts within the community
Alerts generated by SNA are enriched with context comparable to consumer id, system, location, and timestamps, enabling safety groups to research and reply successfully.
To study extra about how Cisco SNA may help you detect superior threats like Salt Hurricane and defend your community infrastructure, go to the Cisco Safe Community Analytics product web page and discover demos and sources.
We’d love to listen to what you suppose! Ask a query and keep linked with Cisco Safety on social media.
Cisco Safety Social Media


