Decryption is a basic pillar in combating trendy cyber threats, empowering organizations to scrutinize encrypted internet visitors and reveal hid dangers. In an period the place nearly all on-line communications are encrypted, together with these exploited by cybercriminals, sturdy decryption insurance policies are important for recognizing and blocking malware, figuring out command and management networks, and stopping internet software assaults. Nevertheless, configuring decryption insurance policies could be complicated and difficult as a consequence of a number of components.
Challenges in Configuring Decryption Insurance policies
Decryption guidelines have to strike a steadiness between granularity and ease. Extremely granular guidelines can present exact management over which visitors is decrypted, however they’ll additionally turn into complicated and troublesome to handle. Simplicity aids in simpler administration and reduces the danger of misconfiguration. The order through which decryption guidelines are evaluated is vital. Guidelines are sometimes processed from prime to backside, and the primary matching rule is utilized. This implies extra particular guidelines must be positioned greater to make sure they’re utilized earlier than extra basic guidelines.
Networks are dynamic, with frequent modifications in functions, providers, and consumer behaviors. Decryption guidelines have to be repeatedly up to date to adapt to those modifications and stay efficient in addressing new threats and visitors patterns. Decryption guidelines typically work together with different insurance policies, corresponding to entry management and intrusion prevention. You will need to take into account these interdependencies to make sure that modifications in decryption guidelines don’t inadvertently impression different safety measures. Misconfigured decryption guidelines can result in false positives, the place respectable visitors is incorrectly decrypted or blocked, and false negatives, the place malicious visitors passes via with out inspection. Correct matching standards are important to reduce these points.
Every decryption rule that’s utilized to visitors consumes system sources. Overloading the system with too many complicated guidelines can degrade efficiency, so you will need to optimize rule configurations to steadiness safety wants with accessible sources.
Decryption guidelines have to be configured to deal with quite a lot of encryption protocols and cipher suites. Guaranteeing compatibility with the newest requirements, corresponding to TLS 1.3, is essential to sustaining safety and performance. Decrypting visitors from websites associated to non-public, finance or healthcare can increase privateness issues, necessitating cautious coverage configuration to bypass such visitors.
Regardless of these challenges, Cisco’s Safe Firewall 7.7 presents options Clever Decryption Bypass as a part of enhanced Decryption Wizard to simplify coverage creation and optimize useful resource utilization, making decryption extra manageable and efficient, specializing in decryption capabilities to make sure safety visibility and effectiveness.
Decryption Coverage Wizard: Key Options and Capabilities
Cisco Safe Firewall 7.7 addresses these challenges with superior decryption capabilities, significantly via enhancements to the Decryption Coverage Wizard. These options make it simpler to create efficient insurance policies whereas sustaining safety, efficiency, and privateness.
Clever Decryption Bypass
The Clever Decryption Bypass characteristic makes use of Cisco’s Encrypted Visibility Engine (EVE) to investigate encrypted visitors and decide danger ranges with out the necessity for decryption. EVE leverages metadata extracted from TLS Consumer Hiya packets corresponding to TLS variations, cipher suite, TLS extensions and so forth. This info helps in figuring out the appliance, even when the payload is encrypted.
By utilizing superior machine studying algorithms, EVE can detect anomalies and classify visitors. These algorithms be taught from identified patterns of each respectable and malicious visitors, enabling the identification of potential threats. EVE creates fingerprints based mostly on identified visitors patterns of particular functions or providers. These fingerprints permit EVE to acknowledge visitors varieties and assess whether or not they’re typical or anomalous. By assessing the danger degree related to numerous visitors varieties, it determines which connections can safely bypass decryption.
Primarily based on EVE’s danger evaluation, the firewall can then:
- Bypass Decryption: For low-risk connections, particularly these going to trusted web sites (decided by URL Class Status of the vacation spot).
- Apply Decryption Insurance policies: Use a “consumer menace” situation, based mostly on EVE’s evaluation, to selectively decrypt higher-risk visitors.
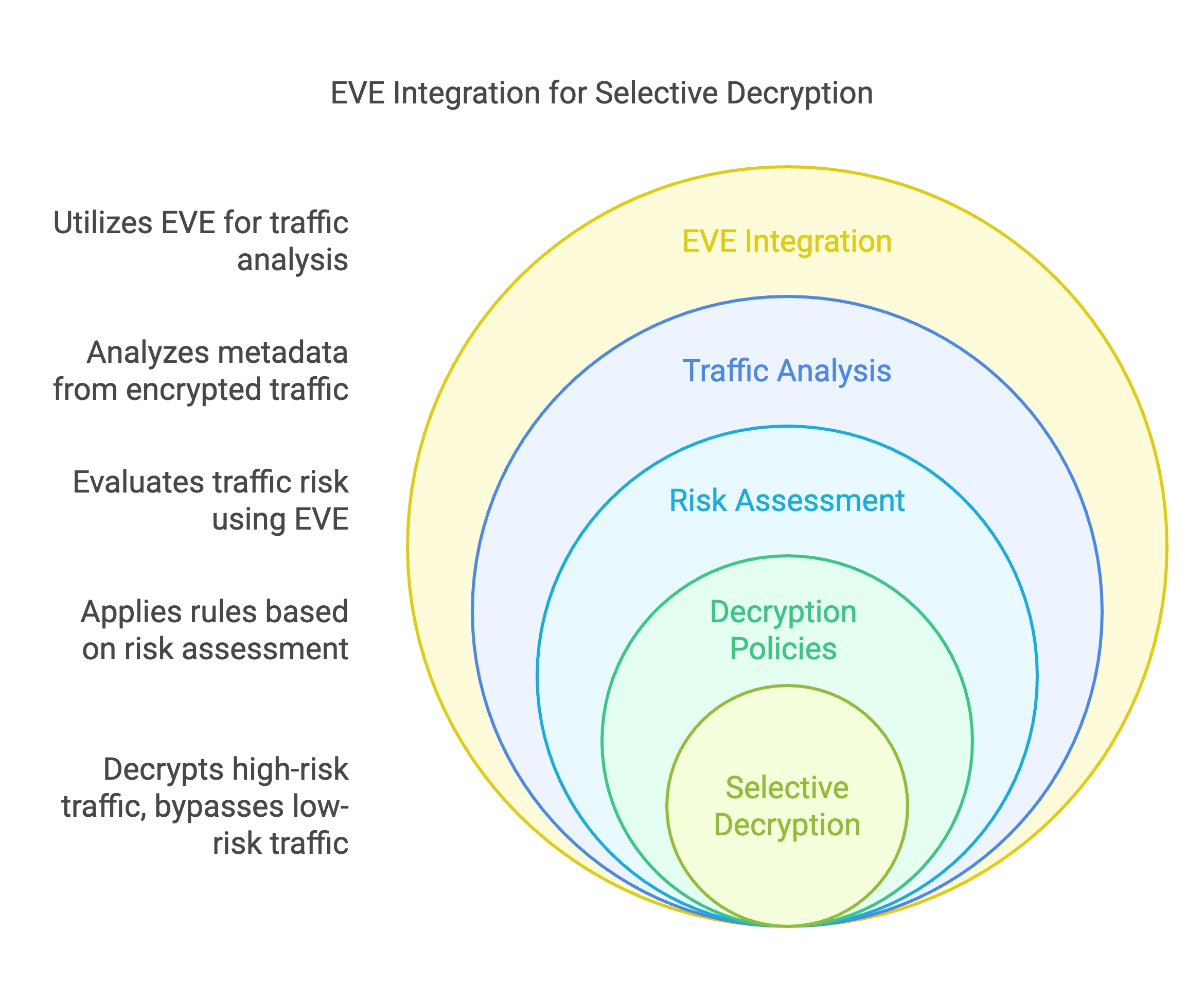
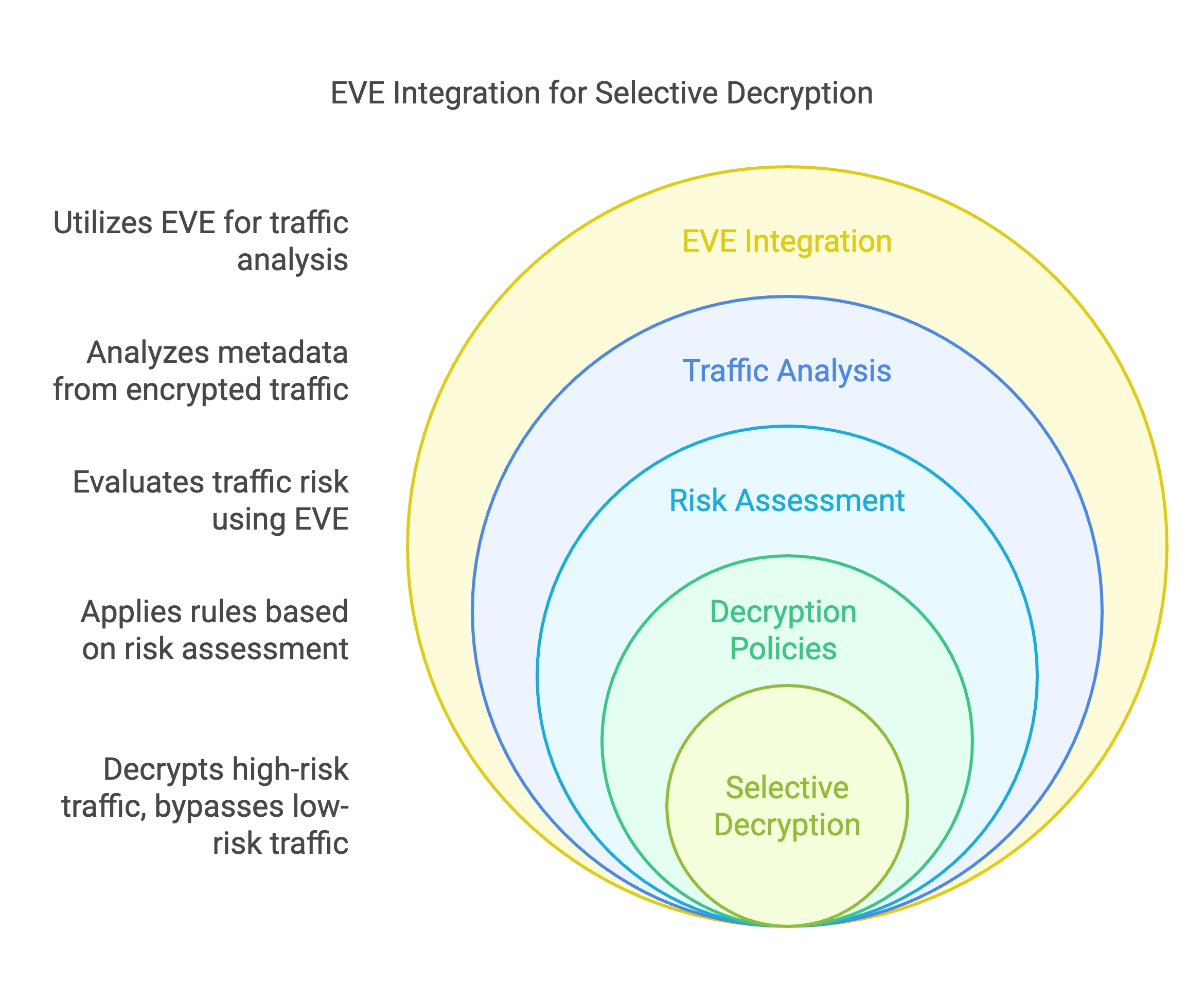
By bypassing decryption for low-risk connections, the characteristic conserves system sources, stopping pointless processing load on gadgets by earlier termination of the TLS handshake for bypassed visitors. This optimization enhances total efficiency and ensures that sources are allotted to decrypting high-risk visitors the place safety positive aspects are most substantial. Bypassing decryption for non-threatening visitors reduces the computational overhead, permitting the system to concentrate on vital areas the place threats usually tend to happen.
Enhanced Decryption Wizard
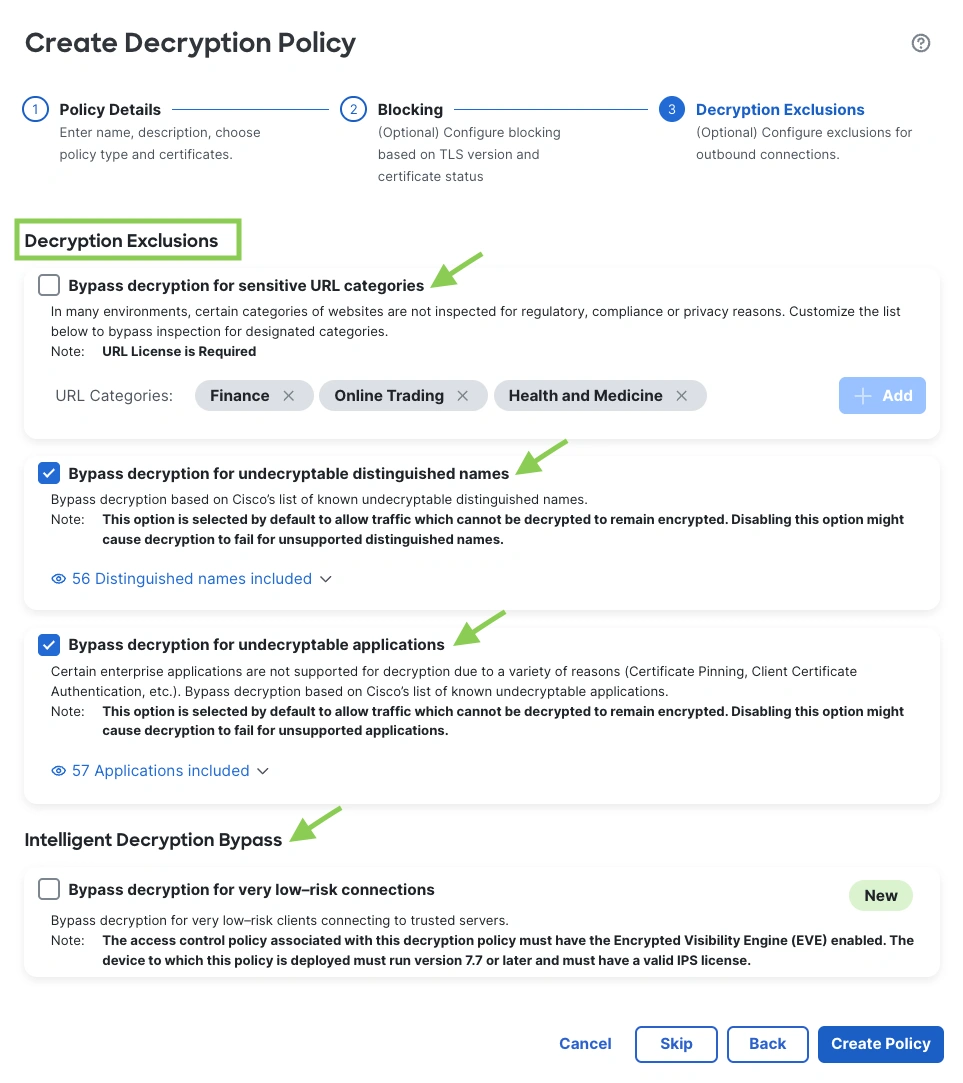
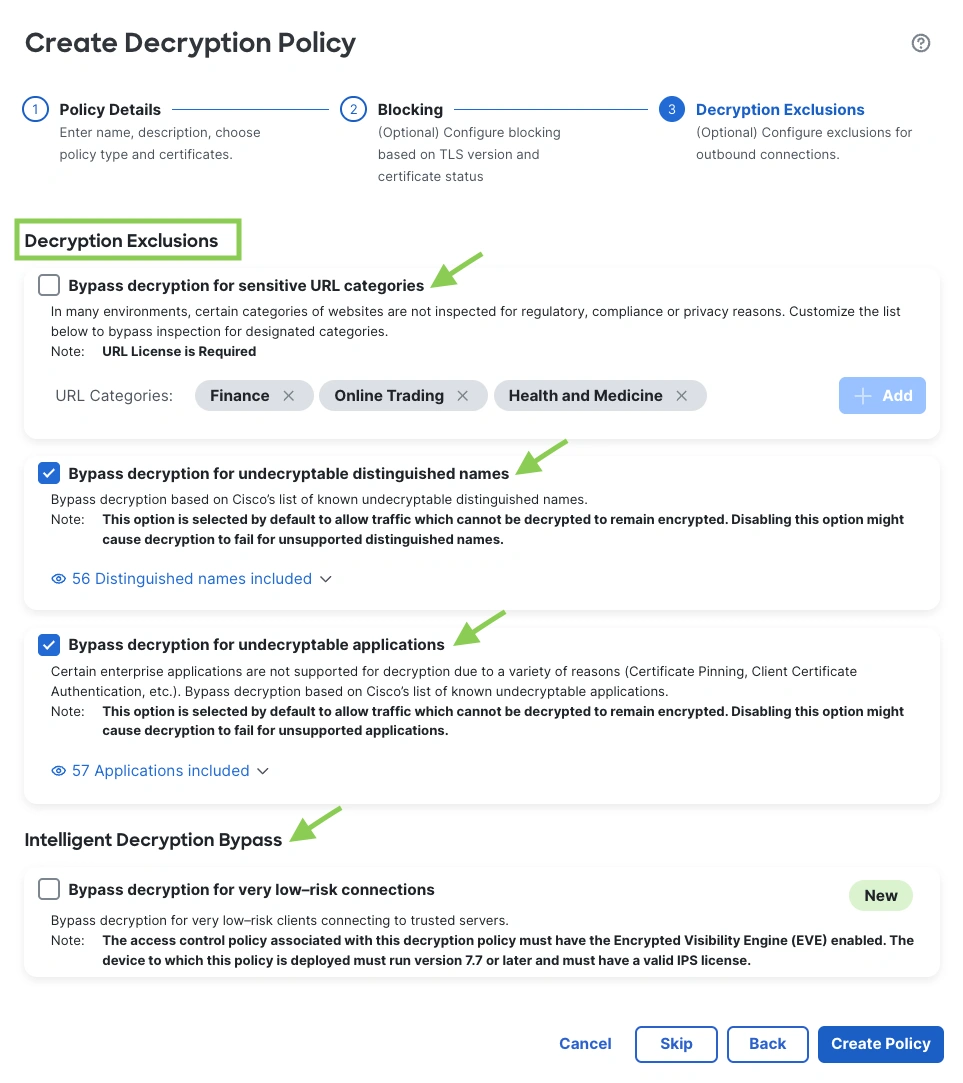
The improved wizard supplies a streamlined interface with single-click choices for configuring decryption insurance policies. This simplicity reduces the complexity sometimes related to handbook coverage tuning.
- Delicate URL Bypassing: The wizard presents easy choices to bypass decryption for URLs related to delicate knowledge, corresponding to finance and healthcare websites, making certain privateness is maintained.
- Dealing with Undecryptable Purposes: It permits straightforward configuration to bypass functions which can be undecryptable as a consequence of protocol limitations or privateness issues, simplifying coverage administration.
The wizard’s intuitive design makes it accessible for directors of all expertise ranges, lowering the effort and time required to arrange efficient decryption insurance policies.
By automating the method of figuring out delicate URLs and undecryptable functions, the wizard minimizes the necessity for ongoing handbook changes. This effectivity ensures that insurance policies stay efficient and updated with out fixed administrative enter.
The instrument ensures safety insurance policies don’t compromise consumer privateness by simplifying the method of excluding delicate communications from decryption.
Blocking Older TLS Variations
The wizard permits directors to dam visitors utilizing older, much less safe variations of TLS and SSL. This consists of variations like SSL 3.0, TLS1.0 and TLS 1.1, which have identified vulnerabilities and are prone to a number of kinds of assaults. By blocking outdated TLS variations, the firewall prevents potential exploits that focus on vulnerabilities inherent in these older protocols, such because the POODLE assault on SSL 3.0.
Many safety requirements and laws require using up-to-date encryption protocols. Blocking older variations helps organizations adjust to these necessities, making certain that solely safe connections are allowed.
Limiting visitors to trendy TLS variations reduces the assault floor, minimizing the danger of varied malicious assaults corresponding to interception assaults, downgrade assaults, replay assaults, and exploits focusing on vulnerabilities in outdated protocols or weak encryption mechanisms, thereby stopping the interception or manipulation of encrypted communications.
Certificates Standing Administration
The wizard consists of choices to dam visitors based mostly on the standing of digital certificates. This includes checking for Expired, Invalid Signatures, and Not But Legitimate certificates utilized in establishing safe connections.
Invalid or compromised certificates could be exploited in assaults the place an adversary intercepts and manipulates communications. By blocking these, the firewall helps stop such safety breaches. Guaranteeing that solely legitimate certificates are accepted reinforces belief within the integrity of the encrypted classes, stopping unauthorized entities from being impersonated as respectable servers.
Robotically managing certificates standing via the wizard simplifies the enforcement of safety insurance policies, lowering administrative overhead and making certain constant safety throughout the community.


General Impression
These options collectively improve the power of Cisco Safe Firewall to handle encrypted visitors effectively. By using EVE and simplifying coverage creation, the system maintains sturdy safety, optimizes useful resource utilization, and respects consumer privateness, making certain that decryption insurance policies are each efficient and sustainable in dynamic community environments.
Decryption Coverage Wizard Enhancements in Cisco Safe Firewall 7.6 and seven.7
The Decryption Coverage Wizard, launched in Launch 7.4, has been considerably enhanced in Cisco Safe Firewall 7.6 and seven.7. These updates streamline the setup course of by routinely including bypass guidelines, often called Do Not Decrypt (DnD) or often called decryption exclusions, for specified outbound visitors, making coverage configuration extra environment friendly.
In Launch 7.6, the wizard can routinely bypass decryption for delicate URL classes, undecryptable distinguished names, and undecryptable functions.
Launch 7.7 additional extends this functionality to incorporate very low-risk connections, providing a extra complete and user-friendly strategy to handle encrypted visitors, known as Clever Decryption or Selective Decryption. Moreover, the wizard permits directors to dam outdated TLS variations and handle invalid certificates statuses, enhancing safety by stopping vulnerabilities related to older protocols and making certain belief in safe connections.
Beneath Desk summarize the accessible decryption exclusion checklist with Decryption Coverage Wizard


Decryptions Exclusions Choices as accessible in Decryption Coverage Wizard View:


The Decryption Coverage Wizard creates coverage that adhere to safety finest practices by:
- Blocking insecure TLS variations and certificates statuses.
- Bypassing decryption for trusted, delicate, and un-decryptable visitors.
- Implementing each inbound and outbound decryption guidelines.
Conclusion
Cisco Safe Firewall 7.7 presents superior decryption capabilities designed to handle the challenges of pervasive encryption. With options like Clever Decryption Bypass, it intelligently identifies and bypasses very low-risk connections by leveraging EVE and URL popularity, using each consumer and server insights. This ensures extremely correct decision-making and elevated safety consciousness, setting it other than many different distributors. These capabilities empower organizations to keep up sturdy safety visibility and effectiveness in an more and more encrypted world.
References
We’d love to listen to what you suppose! Ask a query and keep related with Cisco Safety on social media.
Cisco Safety Social Media
Share:


