On the Utilized Methods Group within the SEI’s CERT Division, one in all our areas of labor focuses on Docker container pictures that require hardening to take away vulnerabilities. By means of our work, we’ve seen stakeholders encountering issue with hardening open-source container pictures, along with growing routine processes for vulnerability mitigation for Docker container pictures.
Utilizing unvetted container pictures can improve safety dangers by means of the introduction of susceptible software program into a company’s software program provide chain. For instance, unvetted container pictures might include packages with recognized Widespread Vulnerabilities and Exposures (CVEs), introducing a possible exploitation vector. As this weblog put up particulars, hardening these container pictures, or deciding on verified pre-hardened container pictures earlier than utilization, decreases the chance of introducing susceptible software program.
Hardening containers and container pictures entails analyzing their present safety standing after which making use of remediations to iteratively enhance safety. The hardening course of is routine and supplies iterative safety monitoring in the course of the growth course of. A hardened picture supplies a safe sandbox for growth and execution of open-source software program.
The Container Hardening Course of
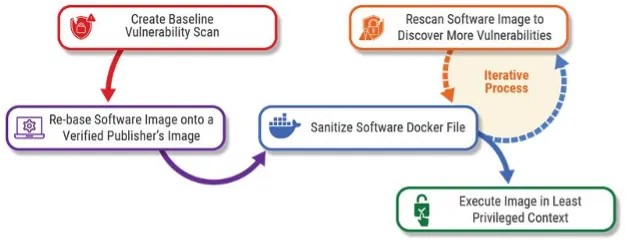
Determine 1: The iterative container hardening course of for vulnerability detection and remediation.
The method of hardening containers and container pictures begins with a baseline safety scan of the unhardened picture to create an inventory of recognized vulnerabilities. As soon as this baseline has been made, engineers ought to analyze the picture Dockerfile and exchange any non-standard base pictures with respected base pictures from verified publishers. Following the rebasing, engineers, utilizing container picture options akin to Docker, ought to start the iterative course of to remediate recognized bugs whereas scanning for brand new vulnerabilities.
It is advisable to switch non-standard pictures utilized in a Dockerfile as a result of, as we talked about earlier, pictures can deliver vulnerabilities that may discover their manner into the tip product. This may take the type of susceptible packages or different dependencies utilized by the picture, however it may additionally come on account of unsecure practices within the picture itself. To counteract this, rebasing the Dockerfile to make use of pictures from Docker verified publishers akin to Pink Hat permits for extra stability in updates and vulnerability mitigation.
These techniques of scanning and substituting pictures is basically the beginnings of a software program invoice of supplies (SBOM), and this makes it simpler to create and monitor an SBOM. The outputs of every safety scan assist establish the place actions are wanted when new vulnerabilities come to mild and might be added to the SBOM to keep up its accuracy.
Decreasing Potential Vulnerabilities in Container Photographs
A number of different practices may also be employed when rebasing a Dockerfile to additional mitigate dangers and vulnerabilities. For starters, if a Dockerfile doesn’t make use of it already, engineers can implement a multi-stage construct course of. This permits the construct course of to put in the dependencies wanted to construct elements of the service, whereas leaving these construct dependencies behind of their respective levels. Doing this enables the construct course of to deliver solely what’s required for the ultimate picture into the ultimate construct stage. Leaving these runtime-irrelevant dependencies out of the ultimate picture can cut back the picture’s risk floor.
In the identical vein, a extra minimal base picture may also be useful. Constructing a container to serve a database, for instance, is unlikely to wish a lot of the options of a full working system (OS) base picture. A number of frequent base pictures akin to Pink Hat Common Base Picture(UBI), Debian, and Rocky Linux provide stripped-down variations leaving fewer superfluous and probably susceptible packages and configurations, and likewise offers the additional advantage of decreasing the scale of the ultimate picture. For extra on the subject of decreasing the scale of pictures, take a look at this SEI presentation by Kevin Pitstick.
There are a number of different tweaks that may additionally assist in decreasing potential vulnerabilities in container pictures. One in every of these is to exchange the usage of the ADD instruction with the COPY instruction wherever attainable. ADD and COPY overlap in that they will each be used to maneuver native information round in the course of the picture constructing course of. Nonetheless, ADD has the extra functionality of with the ability to obtain information referenced by exterior URLs, in addition to unpackage archives. These extra capabilities might be undesirable additions when safety is a priority. Containers also needs to be set to run as a non-root service consumer when attainable, to restrict their capability to carry out malicious duties if compromised. Word that by default, Docker containers run as root. By operating a container as a non-root service, the precept of least privilege is adopted. It’s additionally apply to outline the service consumer early on in a Dockerfile, switching again to root solely as wanted within the construct course of.
The Significance of Vulnerability Scanning
Vulnerability scanning is a vital step in figuring out vulnerabilities in a container picture. Utilizing instruments akin to Grype and Trivy, safety and infrastructure engineers can routinely run safety scans on open-source pictures along with pictures constructed by way of an automatic pipeline. Creating an automatic course of to routinely scan the container picture is a standard a part of most DevSecOps pipelines and can add higher visibility into vulnerability detection. Routine scanning additionally permits for the institution of a vulnerability baseline and incremental mitigation.
Vulnerability scans usually yield an inventory of CVEs, which include details about the vulnerability and any potential mitigations. A CVE often has a Widespread Vulnerability Scoring System (CVSS) rating, which assesses the severity of the vulnerability. Calculating or trying up the CVSS rating can streamline the method of prioritizing the remediation of vulnerabilities.
Hardening of Docker pictures entails inspection of how the picture is constructed, routinely scanning the constructed picture for vulnerabilities, after which making use of mitigations to the picture constructing course of. The continual strategy of scanning new printed pictures helps detect any new vulnerabilities. By establishing a routine course of for hardening pictures, confidence is gained within the manufacturing pipeline ranging from the event stage.


