At the least 187 code packages made accessible by way of the JavaScript repository NPM have been contaminated with a self-replicating worm that steals credentials from builders and publishes these secrets and techniques on GitHub, consultants warn. The malware, which briefly contaminated a number of code packages from the safety vendor CrowdStrike, steals and publishes much more credentials each time an contaminated bundle is put in.
Picture: https://en.wikipedia.org/wiki/Sandworm_(Dune)
The novel malware pressure is being dubbed Shai-Hulud — after the title for the enormous sandworms in Frank Herbert’s Dune novel sequence — as a result of it publishes any stolen credentials in a brand new public GitHub repository that features the title “Shai-Hulud.”
“When a developer installs a compromised bundle, the malware will search for a npm token within the atmosphere,” mentioned Charlie Eriksen, a researcher for the Belgian safety agency Aikido. “If it finds it, it’s going to modify the 20 hottest packages that the npm token has entry to, copying itself into the bundle, and publishing a brand new model.”
On the heart of this growing maelstrom are code libraries accessible on NPM (brief for “Node Package deal Supervisor”), which acts as a central hub for JavaScript growth and gives the most recent updates to widely-used JavaScript elements.
The Shai-Hulud worm emerged simply days after unknown attackers launched a broad phishing marketing campaign that spoofed NPM and requested builders to “replace” their multi-factor authentication login choices. That assault led to malware being inserted into a minimum of two-dozen NPM code packages, however the outbreak was rapidly contained and was narrowly centered on siphoning cryptocurrency funds.
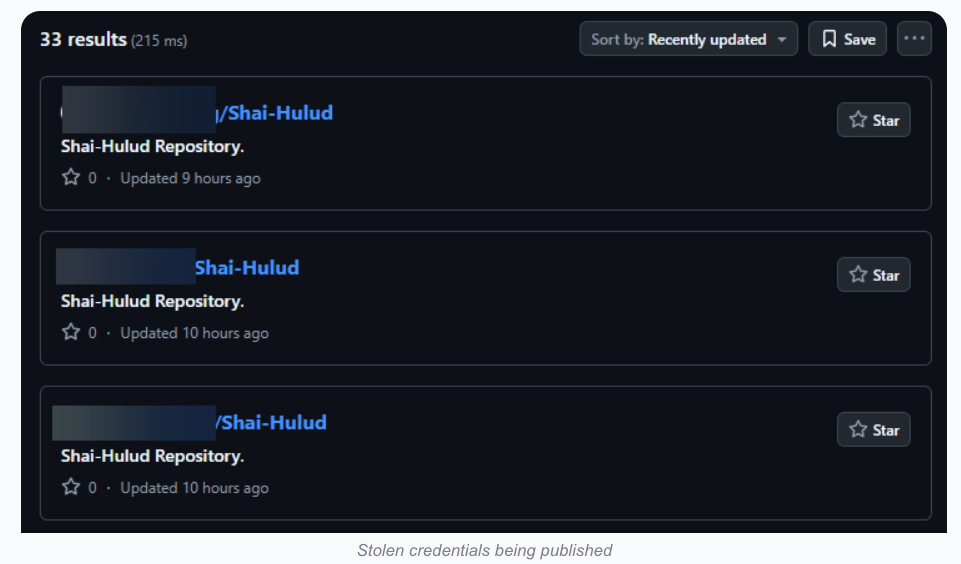
Picture: aikido.dev
In late August, one other compromise of an NPM developer resulted in malware being added to “nx,” an open-source code growth toolkit with as many as six million weekly downloads. Within the nx compromise, the attackers launched code that scoured the person’s machine for authentication tokens from programmer locations like GitHub and NPM, in addition to SSH and API keys. However as a substitute of sending these stolen credentials to a central server managed by the attackers, the malicious nx code created a brand new public repository within the sufferer’s GitHub account, and printed the stolen information there for all of the world to see and obtain.
Final month’s assault on nx didn’t self-propagate like a worm, however this Shai-Hulud malware does and bundles reconnaissance instruments to help in its unfold. Specifically, it makes use of the open-source device TruffleHog to seek for uncovered credentials and entry tokens on the developer’s machine. It then makes an attempt to create new GitHub actions and publish any stolen secrets and techniques.
“As soon as the primary individual acquired compromised, there was no stopping it,” Aikido’s Eriksen informed KrebsOnSecurity. He mentioned the primary NPM bundle compromised by this worm seems to have been altered on Sept. 14, round 17:58 UTC.
The safety-focused code growth platform socket.dev studies the Shai-Halud assault briefly compromised a minimum of 25 NPM code packages managed by CrowdStrike. Socket.dev mentioned the affected packages have been rapidly eliminated by the NPM registry.
In a written assertion shared with KrebsOnSecurity, CrowdStrike mentioned that after detecting a number of malicious packages within the public NPM registry, the corporate swiftly eliminated them and rotated its keys in public registries.
“These packages will not be used within the Falcon sensor, the platform isn’t impacted and prospects stay protected,” the assertion reads, referring to the corporate’s widely-used endpoint risk detection service. “We’re working with NPM and conducting an intensive investigation.”
A writeup on the assault from StepSecurity discovered that for cloud-specific operations, the malware enumerates AWS, Azure and Google Cloud Platform secrets and techniques. It additionally discovered the complete assault design assumes the sufferer is working in a Linux or macOS atmosphere, and that it intentionally skips Home windows programs.
StepSecurity mentioned Shai-Hulud spreads through the use of stolen NPM authentication tokens, including its code to the highest 20 packages within the sufferer’s account.
“This creates a cascading impact the place an contaminated bundle results in compromised maintainer credentials, which in flip infects all different packages maintained by that person,” StepSecurity’s Ashish Kurmi wrote.
Eriksen mentioned Shai-Hulud continues to be propagating, though its unfold appears to have waned in latest hours.
“I nonetheless see bundle variations popping up occasionally, however no new packages have been compromised within the final ~6 hours,” Eriksen mentioned. “However that might change now because the east coast begins working. I’d consider this assault as a ‘residing’ factor nearly, like a virus. As a result of it may possibly lay dormant for some time, and if only one individual is abruptly contaminated accidentally, they may restart the unfold. Particularly if there’s a super-spreader assault.”
Nicholas Weaver is a researcher with the Worldwide Pc Science Institute, a nonprofit in Berkeley, Calif. Weaver known as the Shai-Hulud worm “a provide chain assault that conducts a provide chain assault.” Weaver mentioned NPM (and all different comparable bundle repositories) want to right away swap to a publication mannequin that requires specific human consent for each publication request utilizing a phish-proof 2FA methodology.
“Something much less means assaults like this are going to proceed and develop into much more widespread, however switching to a 2FA methodology would successfully throttle these assaults earlier than they will unfold,” Weaver mentioned. “Permitting purely automated processes to replace the printed packages is now a confirmed recipe for catastrophe.”


