
Hackers began exploiting a high-severity flaw that enables bypassing authentication within the OttoKit (previously SureTriggers) plugin for WordPress simply hours after public disclosure.
Customers are strongly advisable to improve to the most recent model of OttoKit/SureTriggers, at present 1.0.79, launched at first of the month.
The OttoKit WordPress plugin permits customers to attach plugins and exterior instruments like WooCommerce, Mailchimp, and Google Sheets, automate duties like sending emails and including customers, or updating CRMs with out code. Statistics present that the product is lively on 100,000 web sites.
Yesterday, Wordfence disclosed an authentication bypass vulnerability in OttoKit, recognized as CVE-2025-3102. The flaw impacts all variations of SureTriggers/OttoKit as much as 1.0.78.
The flaw stems from a lacking empty worth examine within the authenticate_user() operate, which handles REST API authentication. Exploitation to be doable if the plugin is just not configured with an API key, which causes the saved secret_key to stay empty.
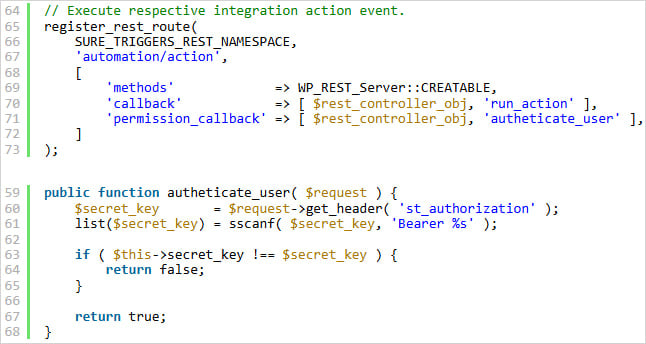
Supply: Wordfence
An attacker may exploit this by sending an empty st_authorization header to go the examine and grant unauthorized entry to protected API endpoints.
Basically, CVE-2025-3102 permits attackers to create new administrator accounts with out authentication, posing a excessive threat of full web site takeover.
Wordfence obtained a report concerning the flaw from safety researcher ‘mikemyers’, who earned a bounty of $1,024 for the invention in mid-March.
The plugin vendor was contacted on April 3 with the total exploitation particulars, and so they launched a repair through model 1.0.79 on the identical day.
Nonetheless, hackers shortly jumped on the alternative to use the difficulty, making the most of directors’ delay in updating the plugin to deal with the safety downside.
Researchers at WordPress safety platform Patchstack are warning that the primary exploitation makes an attempt within the wild had been logged just a few hours after the disclosure of the flaw.
“Attackers had been fast to use this vulnerability, with the primary recorded try occurring simply 4 hours after it was added as a vPatch to our database,” reviews Patchstack.
“This swift exploitation highlights the important want to use patches or mitigations instantly upon the general public disclosure of such vulnerabilities,” the researchers say.
The menace actors try to create new administrator accounts utilizing randomized username/password and e mail handle mixture, an indication of process automation.
If you happen to’re utilizing OttoKit/SureTriggers, improve to model 1.0.79 as quickly as doable and examine logs for surprising admin accounts or different person roles, set up of plugins/themes, database entry occasions, and modification of safety settings.



