In 2024, ESET researchers found a number of malicious instruments within the methods utilized by Kurdish and Iraqi authorities officers. The APT group behind the assaults is BladedFeline, an Iranian risk actor that has been energetic since at the very least 2017, when it compromised officers inside the Kurdistan Regional Authorities (KRG). This group develops malware for sustaining and increasing entry inside organizations in Iraq and the KRG. Whereas that is our first blogpost overlaying BladedFeline, we found the group in 2023, after it focused Kurdish diplomatic officers with the Shahmaran backdoor, and beforehand reported on its actions in ESET APT Exercise reviews This fall 2023-Q1 2024 and Q2 2024-Q3 2024.
The array of instruments utilized within the latest marketing campaign exhibits that since deploying Shahmaran, BladedFeline has continued to develop its arsenal. We discovered two reverse tunnels, quite a lot of supplementary instruments, and most notably, a backdoor that we named Whisper and a malicious IIS module we dubbed PrimeCache. Whisper is a backdoor that logs right into a compromised webmail account on a Microsoft Trade server and makes use of it to speak with the attackers by way of e mail attachments. PrimeCache additionally serves as a backdoor: it’s a malicious IIS module associated to what we known as Group 2 in our 2021 paper Anatomy of native IIS malware. Considerably, PrimeCache additionally bears similarities to the RDAT backdoor utilized by the Iran-aligned OilRig APT group.
Primarily based on these code similarities, in addition to on additional proof introduced on this blogpost, we assess with medium confidence that BladedFeline is a subgroup of OilRig, an Iran-aligned APT group going after governments and companies within the Center East. We’ve got beforehand reported on different exercise linked to OilRig. To keep away from confusion, we have now since refined our OilRig monitoring, and we now monitor each of these operations underneath a separate subgroup – Lyceum – inside OilRig.
BladedFeline has labored constantly to keep up illicit entry to Kurdish diplomatic officers, whereas concurrently exploiting a regional telecommunications supplier in Uzbekistan, and creating and sustaining entry to officers within the authorities of Iraq. This blogpost particulars the technical facets of the preliminary implants delivered to BladedFeline’s targets, the hyperlinks between the victims, and lays the groundwork for associating this subgroup with OilRig.
Key factors of the blogpost:
- BladedFeline compromised officers inside the Kurdistan Regional Authorities at the very least as early as 2017.
- The preliminary implants used there may be traced again to OilRig.
- We found BladedFeline after its operators compromised Kurdish diplomatic officers with the group’s Shahmaran signature backdoor in 2023.
- This APT group has additionally infiltrated high-ranking officers inside the authorities of Iraq.
- We assess with medium confidence that BladedFeline is a subgroup inside OilRig.
- We analyze two reverse tunnels (Laret and Pinar), a backdoor (Whisper), a malicious IIS module (PrimeCache), and numerous supplementary instruments.
BladedFeline overview
BladedFeline is an Iran-aligned cyberespionage group, energetic since at the very least 2017 in line with ESET telemetry. We found the group in 2023 when it deployed its Shahmaran backdoor in opposition to Kurdish diplomatic officers. Shahmaran, named after a legendary half-snake, half-woman creature from Iranian folklore, is a 64-bit transportable executable that we discovered within the goal’s Startup listing. This easy backdoor doesn’t use any compression or encryption for community communications. After checking in with the C&C server, the backdoor executes any operator instructions supplied, which embrace importing and downloading further information, requesting particular file attributes and offering file and listing manipulation API.
As evidenced by the marketing campaign toolset we describe on this blogpost; since deploying Shahmaran, BladedFeline has continued to develop its malware with a view to retain and even additional lengthen its entry to the KRG and to excessive ranges inside the authorities of Iraq (GOI). We uncovered the marketing campaign in 2024 after discovering BladedFeline’s Whisper backdoor, PrimeCache IIS backdoor, and a set of post-compromise instruments within the networks of Kurdish diplomatic officers, Iraqi authorities officers, and a regional telecommunications supplier in Uzbekistan.
We detected and picked up one model of Whisper and located one other on VirusTotal, uploaded by a consumer in Iraq. They’re just about similar, and we have been capable of decide the seemingly identification of the VirusTotal uploader, primarily based on information within the Whisper pattern and different samples uploaded underneath the identical submitter ID. PrimeCache, Flog (a webshell), and Hawking Listener (an early-stage implant that listens on a specified port) have been all uploaded to VirusTotal by the identical submitter ID who uploaded the Whisper samples. Primarily based on the Whisper hyperlink and the shut timeframe (each have been uploaded inside a matter of minutes) we consider it was deployed by BladedFeline to a sufferer in Iraq’s authorities. Among the instruments talked about under within the Timeline are mentioned later within the report (e.g., Slippery Snakelet).
Timeline
2017-09-21 ● VideoSRV reverse shell on KRG system
|
2018-01-30 ● RDAT backdoor on KRG system
|
2019-07-09 ● Customized Plink on KRG system
|
2021-05-01 ● Sheep Tunneler on KRG system
|
2023-01-23 ● LSASS dumped on KRG system
|
2023-02-01 ● Shahmaran backdoor on KRG system
|
2023-03-25 ● First sufferer focused at a telecommunications firm in Uzbekistan
|
2023-06-12 ● Shahmaran model 2 on KRG system for entry upkeep
|
2023-12-14 ● BladedFeline operators executing CLI instructions on KRG system
|
2023-12-16 ● Slippery Snakelet backdoor on KRG system
|
2023-12-20 ● P.S. Olala (a PowerShell executor) on KRG system
|
2023-12-20 ● PsExec on KRG system
|
2024-01-07 ● Whisper backdoor on KRG system
|
2024-02-01 ● Laret reverse tunnel on KRG system
|
2024-02-20 ● Pinar reverse tunnel on KRG system
|
2024-02-29 ● PrimeCache malicious IIS module uploaded to VirusTotal
|
2024-03-11 ● Whisper model 2, Flog, and Hawking Listener uploaded to VirusTotal
Attribution
Our attribution of this marketing campaign to BladedFeline is predicated on the next:
- The marketing campaign targets members of the KRG, as have earlier assaults carried out by BladedFeline.
- The unique assault exercise focusing on the KRG group allowed us to determine successive malware, as BladedFeline has tried to keep up and increase entry to the group.
- Additional evaluation of the assaults led us to determine the telecommunications sufferer in Uzbekistan.
- On the identical time, wanting into the Whisper backdoor helped us determine the GOI sufferer.
We assess that BladedFeline is focusing on the KRG and the GOI for cyberespionage functions, with an eye fixed towards sustaining strategic entry to high-ranking officers in each governmental entities. The KRG’s diplomatic relationship with Western nations, coupled with the oil reserves within the Kurdistan area, makes it an attractive goal for Iran-aligned risk actors to spy on and probably manipulate. In Iraq, these risk actors are likely attempting to counter the affect of Western governments following the US invasion and occupation of the nation.
We consider with medium confidence that BladedFeline is a subgroup of OilRig:
- As does OilRig, BladedFeline targets organizations within the Center East with the aim of cyberespionage.
- We’ve got discovered OilRig instruments (VideoSRV and RDAT) in a compromised KRG system.
- BladedFeline’s malicious IIS module PrimeCache shares code similarities with OilRig’s RDAT.
BladedFeline shouldn’t be the one subgroup of OilRig that we’re monitoring: we have now already been monitoring Lyceum, also called HEXANE or Storm-0133, as one other OilRig subgroup. Lyceum focuses on focusing on numerous Israeli organizations, together with governmental and native governmental entities and organizations in healthcare. Main instruments we attribute to Lyceum embrace DanBot, the Shark, Milan, and Marlin backdoors, Photo voltaic and Mango, OilForceGTX, and a number of downloaders utilizing reputable cloud providers for C&C communication.
We’ll proceed to make use of the identify OilRig to discuss with the mother or father group, also called APT34 or Hazel Sandstorm (previously EUROPIUM). OilRig is a cyberespionage group that has been energetic since at the very least 2014 and is often believed to be primarily based in Iran. The group targets Center Jap governments and quite a lot of enterprise verticals, together with chemical, power, finance, and telecommunications. Notable OilRig campaigns embrace the 2018 and 2019 DNSpionage marketing campaign, focusing on victims in Lebanon and the United Arab Emirates; the 2019–2020 HardPass marketing campaign, utilizing LinkedIn to focus on Center Jap victims within the power and authorities sectors; the 2020 assault in opposition to a telecommunications group within the Center East utilizing the RDAT backdoor; and the 2023 assaults focusing on organizations within the Center East with the PowerExchange and MrPerfectionManager backdoors.
OilRig instruments utilized by BladedFeline
We’ve got discovered two OilRig instruments on the KRG machines compromised by BladedFeline.
RDAT
We found a beforehand unreported model of the OilRig backdoor RDAT on two KRG sufferer methods. Analyzing RDAT, we discovered that the operational circulate (see Unit 42’s report for specifics), compilation timestamp (2017-12-26 10:49:35), and file write time (2018-01-30) align with OilRig exercise and focusing on, significantly with regard to the group’s 2017 exercise. We noticed a file with an SHA-1 of 562E1678EC8FDC1D83A3F73EB511A6DDA08F3B3D and a path of C:WindowsSystem32LogonUl.exe on each methods. The PDB path additionally corroborates that this binary is RDAT: C:UsersVoidDesktopRDATclientx64Releaseclient.pdb. Up to now, we have now solely ever noticed RDAT in use by OilRig. Furthermore, we have now not seen any customized implant sharing between OilRig and different Center Jap teams, and it seldom happens between Iran-aligned risk actors.
Additional bolstering the case that BladedFeline is an OilRig subgroup, as with Lyceum, is the evaluation linking RDAT with PrimeCache, a malicious IIS module that was uploaded to VirusTotal presumably by the GOI sufferer. This hyperlink is explored in additional depth within the Hyperlinks with OilRig part of the blogpost.
VideoSRV
One further information level on the OilRig and BladedFeline connection is a reverse shell deployed to one of many KRG victims (September 21st, 2017) previous to RDAT getting dropped on the identical system (January 30th, 2018). VideoSRV (SHA-1: BE0AD25B7B48347984908175404996531CFD74B7), so named for its filename videosrv.exe, has the PDB string C:Usersv0idDesktopreverseShellclientProxyx64ReleaseConsoleApplication1.pdb, which bears some similarities to the RDAT PDB string C:UsersVoidDesktopRDATclientx64Releaseclient.pdb.
Technical evaluation
Preliminary entry
It’s nonetheless unclear how BladedFeline is creating entry to its victims. What we all know is that within the case of the KRG victims, the risk actors obtained entry at the very least way back to 2017 and have maintained it ever since. As for the GOI victims, we suspect that the group exploited a vulnerability in an utility on an internet-facing internet server, which allowed them to deploy the Flog webshell.
Toolset
PrimeCache – malicious IIS module
PrimeCache, whose identify we derived from the RTTI AVRSAPrimeSelector and its filename (cachehttp.dll), is a passive backdoor carried out as a local IIS module with an inner identify of HttpModule.dll. It was uploaded to VirusTotal by the identical consumer who uploaded one of many Whisper backdoor samples. It’s a 64-bit C++ DLL with a compilation timestamp of 2023-05-14 06:55:52 and has a minimized PDB string of simply HttpModule.pdb. It has a single export: RegisterModule.
PrimeCache is a successor to a set of unattributed IIS backdoors that we have now beforehand reported as Group 2 (easy IIS backdoors) in our 2021 blogpost, Anatomy of native IIS malware. We obtained these authentic samples from VirusTotal the place they have been uploaded by customers from Bahrain, Israel, and Pakistan, between 2018 and 2020. Primarily based solely on the placement of the presumed victims, it’s potential that these instances have been additionally associated to BladedFeline – or, extra broadly, OilRig – actions.
Essential performance
PrimeCache’s most important performance is carried out within the CGlobalModule::OnGlobalPreBeginRequest handler. It is a distinctive implementation, differing from its predecessors, which used the CHttpModule::OnBeginRequest handler. PrimeCache filters incoming HTTP requests, solely processing these from the BladedFeline operators, that are acknowledged by having a cookie header with the construction:
F=
Notice that this worth may be standalone or embedded into an extended cookie, surrounded by semicolon (;) characters.
The backdoor works in an uncommon manner (new with this model as in contrast with our 2021 evaluation). Moderately than accepting a backdoor command and all its parameters inside a single HTTP request, every motion is cut up into a number of requests. First, the BladedFeline operator sends a person request for every single parameter; these parameters are saved in a world construction. Then the operator sends one other request to set off the backdoor command. Lastly, PrimeCache makes use of the beforehand obtained parameters to execute the required motion, after which clears the cached parameters.
Operator instructions
There are three varieties of requests that may be obtained by the backdoor, as proven in Desk 1.
Desk 1. PrimeCache operator instructions
| Parameter | Description | |
| 1 | Format: |
Clears the record of beforehand saved parameters and provides the brand new worth. Most parameters are encrypted; see Encryption under. |
| 0 | Not used. | Triggers the backdoor motion, utilizing beforehand transmitted backdoor parameters. |
| Different | Format: |
Provides the required worth to the record of saved parameters (doesn’t clear the record). Most parameters are encrypted; see Encryption under. |
As soon as the motion is triggered (by way of
The PrimeCache motion is operator command (OpCom) a, the session secret’s OpCom okay, binary information is OpCom b, and the filename is OpCom f.
Desk 2. PrimeCache post-operator command actions
| PrimeCache motion | Session key | Binary information | Filename | Command description | Return worth |
| r | RSA-encrypted session key | AES-encrypted command line | Null | Runs the required command by way of popen. | Command output |
| r2 | Runs the required command by way of CreateProcessW. | ||||
| r3 | (Presumably) runs the required command by sending it to a different (unknown) course of by way of the named pipe .pipeiis, then reads (presumably) the command output from the identical pipe. | ||||
| u | AES-encrypted file content material | Native filename | Creates a neighborhood file with the required identify and content material. | OK | |
| d | Null | Exfiltrates the given file from the compromised IIS server. | File content material |
Encryption
Just like its predecessors, PrimeCache makes use of each RSA and AES-CBC for its C&C communication. The parameters and the return values are at all times AES-CBC encrypted utilizing the session key, then base64 encoded. The session secret’s RSA encrypted; the backdoor has a hardcoded non-public and public RSA key (not a pair) to deal with each instructions of the communication.
A statically linked Crypto++ library is used to deal with the encryption and decryption operations.
C&C communications
Operator instructions are transmitted within the cookie header (one other deviation from earlier variations, which used the URL or the HTTP request physique). PrimeCache responses are added to the HTTP response physique. If a file is being exfiltrated, the Content material-Kind header is ready to attachment, matching the performance of the earlier variations.
The PrimeCache predecessors additionally used the identical encryption scheme, and comparable parameter names (a, c, f, okay), however all have been despatched to the backdoor in a single request. The one supported instructions have been r, u, and d.
Hyperlinks with OilRig
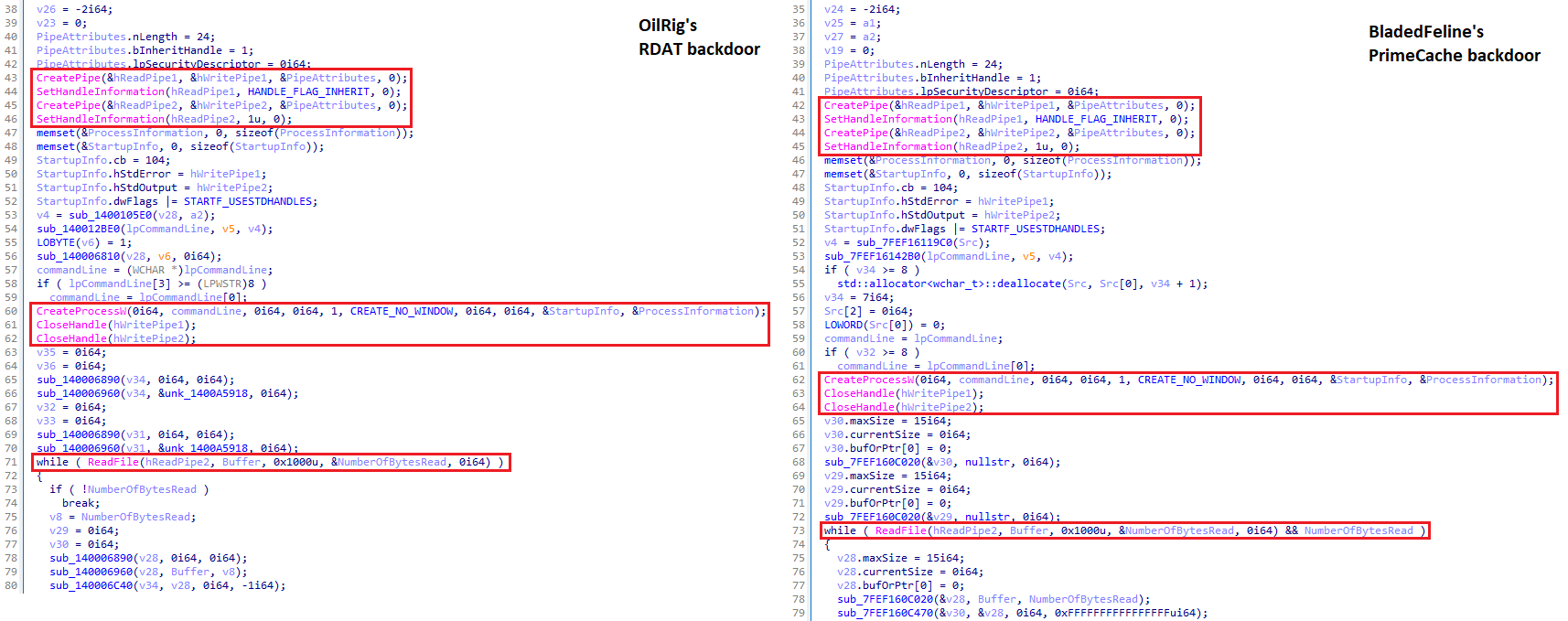
Once we examine PrimeCache with RDAT, as described within the RDAT attribution subsection, we see a number of similarities that help our supposition that BladedFeline is a subgroup of OilRig.
- Each RDAT and PrimeCache use the Crypto++ library, and each parse the backdoor instructions utilizing the common expression [^,]+.
- The payload makes an attempt to parse the decrypted cleartext utilizing the common expression [^,]+ to get the command worth and the command arguments which might be cut up with a comma.
- Each share a operate, proven in Determine 1, that executes a shell command and reads the output, which, throughout our corpus, is discovered solely in these two items of malware.
Whisper backdoor
Whisper is a 32-bit Home windows binary written in C#/.NET, named after its PDB strings G:csharpWhisper_Trojan_winformWhisper_Trojan_winformWhisper_Trojan_winformobjReleaseVeaty.pdb and Z:csharpWhisper_Trojan_winform_for_releaseWhisper_Trojan_winformWhisper_Trojan_winformobjReleaseVeaty.pdb. It makes use of a Microsoft Trade server to speak with the attackers by sending e mail attachments by way of a compromised webmail account. We’ve got seen two variations of the backdoor: we detected and picked up one model, and was uploaded to VirusTotal from Iraq. These samples are just about similar, however we have been capable of decide the seemingly identification of the VirusTotal uploader primarily based on information within the Whisper pattern and different samples uploaded by that consumer.
Each these variations of Whisper have timestomped compilation timestamps (2090-04-11 23:38:14 and 2080-12-11 03:50:47). They’re constructed utilizing Costura, presumably to make sure that the sufferer’s system makes use of the DLLs packaged with the binary and never DLLs within the International Meeting Cache.
Whisper’s operation shouldn’t be the primary time we have now noticed an OilRig subgroup utilizing cloud providers for its C&C protocol. Whereas, in contrast to with Whisper, there have been no emails truly being despatched, Lyceum used e mail drafts for communication between its malware and operators all through 2022, as we described in a earlier blogpost.
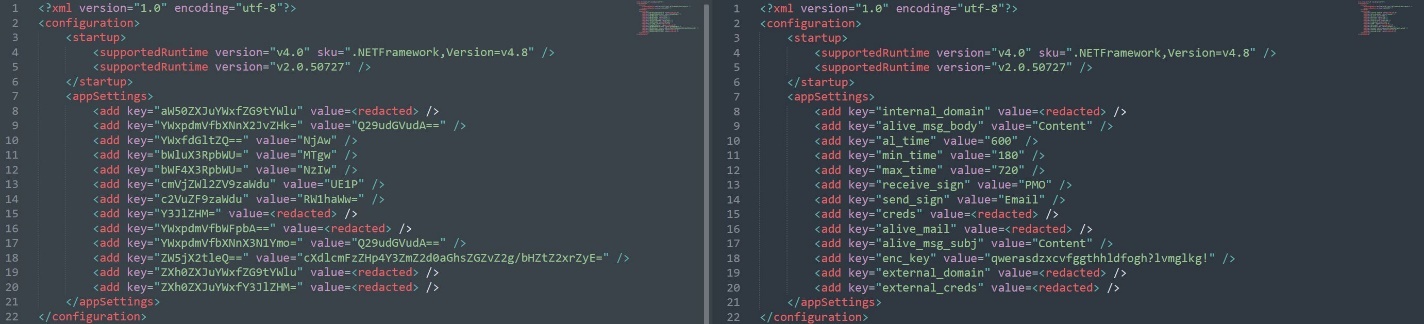
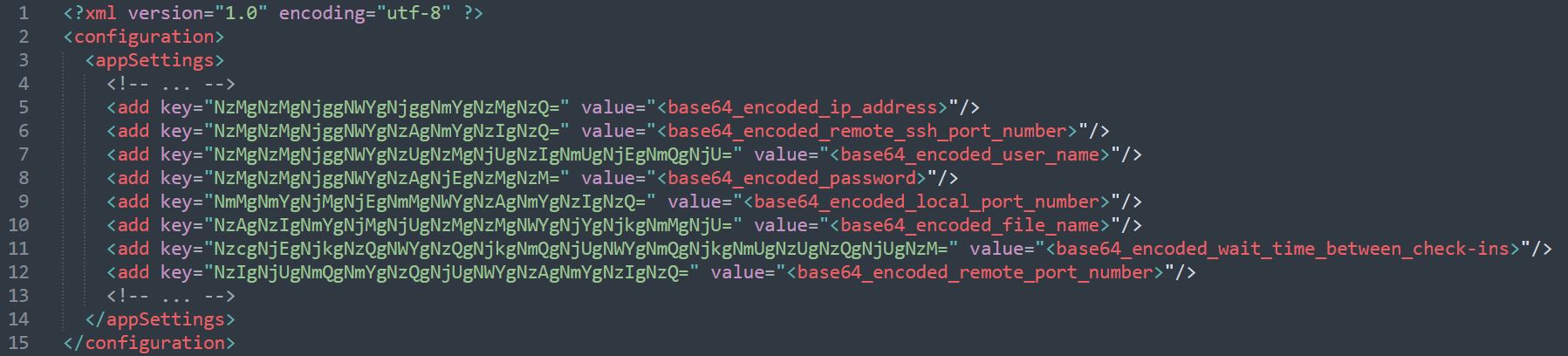
Operational workflow
Whisper doesn’t require or settle for any arguments. As an alternative, its dropper – which we dubbed Whisper Protocol after its filename, Protocol.pdf.exe – writes its configuration file to disk alongside it (see the Whisper Protocol part). The config file, proven in Determine 2, is in XML format with its key and worth strings base64 encoded. It’s known as by the Specs class of Whisper, which makes use of a operate – DelockItems – to base64 decode the config variables.
Determine 3 exhibits the operational circulate of Whisper, which we element within the following paragraphs.
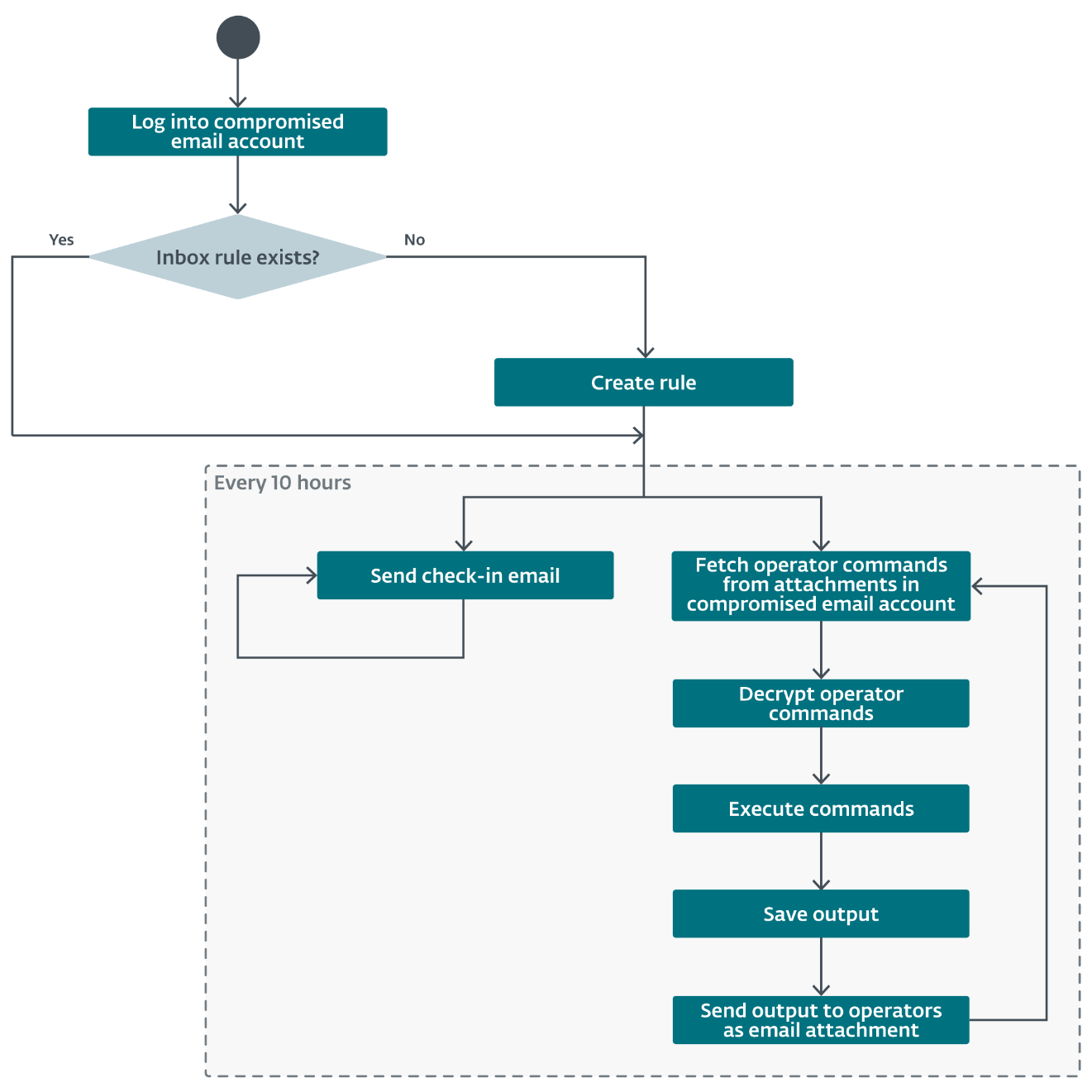
Whisper’s operational circulate may be damaged down into seven steps:
In Step 1, Whisper makes use of the credentials from the config file (line 15 in Determine 2) and the Microsoft Trade Net Providers class ExchangeService to aim to log into compromised webmail accounts. As soon as Whisper efficiently logs into an account, it saves the credentials in reminiscence and writes the next to the log file c:WindowsTempWindowsEventLogs.txt:
———— ItemContext is ready: username [
If no credentials within the config file are legitimate, Whisper logs the next error messages to the log file:
———————————- there was No Strategy to entry any MailBox.
__________ Extraction operate is named.
If an sudden error is caught, Whisper writes the next to the log file (observe the misspelling of the phrase occurred, indicative of a non-native English speaker) and exits utilizing the Atmosphere.Exit(Int32) methodology. Surprisingly, the exitCode used, 0, signifies that the method accomplished efficiently.
———————————-__ an unknown Exception happend. program turned off
Subsequent, in Step 2, Whisper makes use of the credentials from the earlier step to test for inbox guidelines utilizing the ExchangeService.GetInboxRules methodology (which [r]etrieves a set of Inbox guidelines which might be related to the required consumer). Utilizing the worth in line 13 of the configuration file (key=”receive_sign”, worth=”PMO”), Whisper iterates over the inbox guidelines on the lookout for that worth to be laid out in one in all three locations: topic, physique, or subjectorbody and for emails matching that worth to be despatched to a specified location (deleteditems or inbox, relying on the model of Whisper). If the inbox has such a rule, Whisper goes to the subsequent step; in any other case, Whisper creates a rule with the given parameters:
- Rule identify: MicosoftDefaultRules.
- Transfer to folder: deleteditems or inbox.
- One model of Whisper specifies the deleteditems folder; the opposite factors to the inbox. Each are hardcoded within the separate binaries.
- Mark as learn: true.
- Situation: topic incorporates PMO.
- The situation to search for the string, topic, is hardcoded in each variations of Whisper. The string to search for, PMO, is within the configuration file utilized by Whisper; we have been unable to gather the opposite configuration file.
In Step 3, Whisper initiates a unending do loop that sends a check-in e mail message from the compromised e mail account in Step 1 to an e mail deal with specified within the configuration file (line 16, key=”alive_mail”). The check-in message is shipped each 10 hours (line 10 within the configuration file, key=”al_time”; in minutes), the topic (line 17, key=”alive_msg_subj”) is Content material, and the message physique incorporates the string outlined under:
“Content material ID: “ + base64_encode(“COMPUTERNAME:USERDNSDOMAIN:USERNAME”)
Subsequent, in Step 4, Whisper fetches operator instructions. It does so by looking the inbox recognized in Step 1 for information in a given folder (deleteditems or inbox, relying on the model of Whisper) with attachments the place the topic matches a string (equipped within the configuration file; PMO in the one configuration file we collected). For matching emails with attachments, Whisper scrapes the attachment physique (which ought to include encrypted instructions) and shops the sender’s e mail deal with to be used later because the C&C server to which operator command outcomes are uploaded.
In Step 5, Whisper decrypts the operator instructions. It does so by first base64 decoding the string containing the command after which decrypting the end result utilizing the .NET AES class with a 16-byte initialization vector and the encryption key discovered within the configuration file (line 18, key=”enc_key” worth=”cXdlcmFzZHp4Y3ZmZ2d0aGhsZGZvZ2g/bHZtZ2xrZyE=”). Decrypted instructions are within the type of
base64-encoded(
Then, in Step 6, Whisper executes the backdoor instructions and data the outcomes. Attainable instructions embrace:
The information written to disk is:
that is my file content material
The bytes to jot down are base64 encoded (and decoded earlier than writing to disk). Profitable execution returns:
file obtained correctly. wrote to:
- Ship a file to the C&C server
This command is prefixed with that is my required file path adopted by n
that is my required file
- Execute a PowerShell script
This command doesn’t have a prefix and as a substitute solely incorporates a plaintext command that PowerShell is able to executing, postfixed with a pipe after which Whisper appends Out-String. Output is saved on this type:
base64-encoded(
Lastly, in Step 7, Whisper sends the command output in an e mail message to the C&C inbox present in Step 4. The e-mail is formatted with these particulars:
- sending e mail deal with: inbox from Step 1,
- recipient: e mail deal with from Step 4,
- topic: E-mail (from the configuration file, line 14, key=”send_sign”),
- message physique: Hey There! discover your ends in the attachment (hardcoded within the binary), and
- attachment: output from the instructions in Step 6, encrypted with the identical encryption key in Step 5 (configuration file line 18, key=”enc_key” worth=”cXdlcmFzZHp4Y3ZmZ2d0aGhsZGZvZ2g/bHZtZ2xrZyE=”).
Steps 4–7 proceed in a loop utilizing the identical check-in schedule from Step 3 till the credentials hardcoded within the configuration file are modified.
Shahmaran backdoor
The Shahmaran backdoor, named after a legendary half-snake, half-woman creature from Iranian folklore, is a 64-bit PE that was discovered within the startup folder as:
%ROAMINGAPPDATApercentMicrosoftWindowsStart MenuProgramsStartupadobeupdater.exe
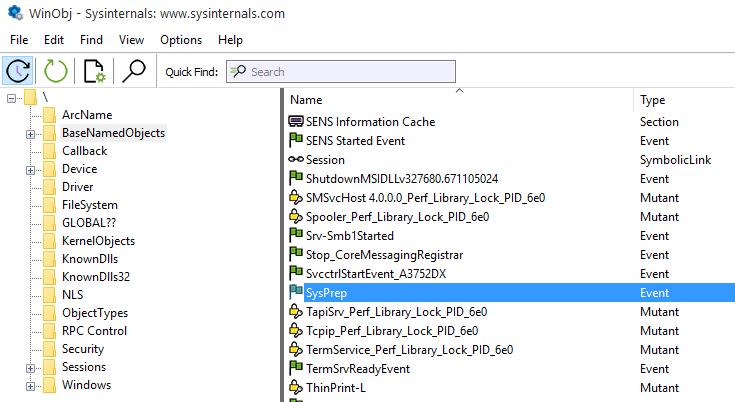
At system startup, Shahmaran creates a Home windows occasion object, SysPrep. It’s potential that the Shahmaran builders selected SysPrep because the occasion identify to mix into the background noise, as SysPrep is a part of the Home windows imaging course of. Home windows admins use it to create a typical Home windows picture (also known as a Gold or Golden picture) earlier than deployment to enterprise methods. Determine 4 exhibits the SysPrep occasion object on a compromised system as seen by Sysinternals’ WinObj.
The C&C area is hardcoded, olinpa[.]com, as is the port, 80, and the Person-Agent string, of which there are two. The preliminary connection to the C&C makes use of an incomplete Person-Agent string (it’s lacking the closing parenthesis):
Mozilla/4.0 (appropriate; MSIE 6.0; Home windows NT 5.0
Subsequent communication with the C&C makes use of the corrected Person-Agent string:
Mozilla/4.0 (appropriate; MSIE 6.0; Home windows NT 5.0)
Shahmaran doesn’t use any compression or encryption for community communications. And whereas the port is hardcoded (80), there are code fragments that test for the port in use and replace communication variables if port 443 is used.
After checking in with the C&C server, Shahmaran executes any operator instructions supplied, returns any output from these instructions, then sleeps for 30 seconds earlier than checking in with the C&C server once more, advert infinitum. Desk 3 exhibits the obtainable operator instructions and their capabilities.
Desk 3. Operator instructions and their descriptions
| Operator command | Description |
| 1 |
Returns the datetime that the required file was written to disk in UTC, prepended with id= and within the format YYYY/MM/DD HH:MM:SS. |
| 2 |
Strikes the required file to the required location. Returns the output of the file transfer operation prepended with id=. |
| 3 |
Deletes the required file. Returns the output of the file delete operation prepended with id=. |
| 4 |
Creates the required listing. Returns the output of the listing creation operation prepended with id=. |
| 5 | Creates a log file within the hardcoded location c:programdata~tmp.log, if it doesn’t exist already. If the file already exists, reads the contents and returns them to the C&C server with the file’s timestamp in UTC and within the format YYYY/MM/DD HH:MM:SS, then deletes the file. If the file doesn’t exist, returns the filename and path. If an error happens, returns the error. All returned information is prepended with s=. |
| 6 |
Checks for the required file. If discovered, writes the supplied information to the file and returns s= |
| 7 |
Creates the required file. Returns s= appended with both the filename (success) or an error code. |
| 8 |
Checks for the presence of the required filename in a compressed folder within the specified location on disk and creates it if it doesn’t exist. Returns s= appended with the filename and the timestamp in UTC within the format YYYY/MM/DD HH:MM:SS. The timestamp is used to find out whether or not the file was already current or was simply created. |
After executing an operator command, Shahmaran sends the output to the C&C server utilizing the format t=
Slippery Snakelet backdoor
Slippery Snakelet is a small Python-based backdoor with restricted capabilities:
1. executes a command by way of cmd.exe,
2. downloads a file from a URL, and
3. add a file to the /newfile/ URI path.
Slippery Snakelet has a hardcoded C&C server, zaincell[.]retailer, and communicates with it by way of URLs of the shape https://zaincell[.]retailer/request/
Slippery Snakelet additionally has this hardcoded Person-Agent:
Mozilla/5.0 (Home windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/88.0.4324.104 Safari/537.36
The C&C server was disguised as an Arabian Gulf E-Studying website and the default HTML touchdown web page doesn’t include any instructions. When Slippery Snakelet provides a appropriately formatted request (e.g., https://zaincell[.]retailer/request/ tags akin to 6wjTyB3Y20KSzU1VUlTagp3aG9hbWkKbnVsbApudWxs into the web page, and Slippery Snakelet collects and decodes these.
Slippery Snakelet base64 decodes all the pieces from the eighth character to the tip of the string (i.e., Y20KSzU1VUlTagp3aG9hbWkKbnVsbApudWxs within the instance above). The decoded output is newline separated and incorporates the 5 objects described in Desk 4
Desk 4. Slippery Snakelet arguments and choices
| Instructions | Choices | Instance |
| Command Kind | cm (execute cmd.exe command) getfl (obtain a file) sendfl (add a file) |
cm |
| Command ID | CMID (a random string) | K55UISj |
| Command | FileUrl | FilePath | Respectively for cm | getfl | sendfl | whoami |
| Null | SavePath | FilePath | Respectively for cm | getfl | sendfl | null |
| Null | Unknown | null |
Laret and Pinar – reverse tunnels
Laret and Pinar, whose names are derived from the inner names in every respective file, are 32-bit Home windows binaries written in C#/.NET. Each have timestomped PE compilation timestamps – a tactic that’s widespread amongst Center Jap (and significantly Iran-nexus) risk teams – of 2058-02-07 00:12:48 and 2072-07-10 18:26:15, respectively. Each have been discovered on two methods on the places in Desk 5.
Desk 5. Areas of Laret and Pinar on disk, together with filenames
| Reverse tunnel | Location |
| Laret | %APPDATApercentLocalLEAP DesktopLEAPForm.exe |
| Pinar | C:Program FilesLEAP OfficeSystemMain.exe |
| C:Program FilesLEAP Officewinhttpproxy.exe |
Within the case the place we do not need a location on disk for Laret however we do have the filename (wincapsrv.exe), we might see that Laret was downloaded from http://178.209.51[.]61:8000/wincapsrv.exe by way of PowerShell. Sadly, we didn’t handle to find the place it was written to disk. Makes an attempt to enumerate the IP and obtain the file have been rebuffed by the C&C server, seemingly indicating that some type of compromised host identification is required within the connection setup (which we do not need).
Concerning writing to disk, BladedFeline operators seemingly timestomped the file creation date of Pinar to 2017-09-14 14:56:00 on one of many two compromised methods. How the file creation date was timestomped is an open query, but it surely exhibits that the attackers have compromised these two methods to such an extent that they in all probability have administrative rights.
At runtime, each Laret and Pinar depend on a configuration file in the identical listing as their binaries for eight required variables, that are listed in Desk 6.
Desk 6. Laret and Pinar configuration parameters with default hardcoded values
| Area | Description | Default worth |
| ssh_host | C&C IP deal with. | N/A |
| ssh_port | 22 | |
| ssh_username | C&C username. | N/A |
| ssh_pass | C&C password. | N/A |
| local_port | 9666 | |
| process_file | File to execute earlier than executing any reverse tunnel actions. | N/A |
| wait_time_minutes | Time to attend between check-ins with the C&C server. | 10f (271) |
| remote_port | Port quantity used for port forwarding. | 1234 |
We’ve got to this point not collected the configuration file however have reconstructed its seemingly content material, present in Determine 5, primarily based on code evaluation. Studying from the configuration file is completed by base64 decoding the encoded string to bytes, which leads to strings of space-delimited, hexadecimal-encoded character values, which in flip are decoded into ASCII strings.
The BladedFeline builders discuss with this as Delocking and the other (writing to the configuration file) as Enlocking. This in all probability signifies a passing familiarity with English, however the builders have been removed from proficient. Different examples of weak translation expertise embrace:
- time Alapsed and consumer not linked
- aerpoo after
- Ready connection …
- error in creaate ssh consumer
Apparently, at one other level within the reverse tunnels, the builders appropriately spelled the phrase elapsed (time elapsed!), which is indicative of poor coding and lax code evaluation, if any is carried out (e.g., there may be numerous command end result textual content output to the command line, as if the reverse tunnels have been shipped instantly after profitable testing was accomplished).
The precise operate and circulate of Laret and Pinar after amassing the parameters from the configuration file is kind of banal, however that’s in all probability an intentional effort to mix in. Each search for a filename within the process_file parameter and, if a file matching the equipped identify is current, execute it and begin two threads:
- Units up an SSH connection to the C&C IP within the configuration file utilizing the Core.Renci.SshNet DLL included inside the binary. Port 22 is hardcoded because the C&C port and port forwarding can be enabled, utilizing the remote_port variable from the configuration file.
- Units up a listener on the port specified within the local_port parameter of the configuration file. Notice that any information despatched to the listener is completed within the clear (i.e., no encryption or obfuscation is used past further � characters which might be eliminated on the time of receipt by Laret and Pinar).
If no file is laid out in process_file, each Laret and Pinar skip establishing a listener port.
Laret and Pinar solely differ considerably in that Pinar units up a service, known as Service1, for persistence previous to executing the 2 threads. Laret has no technique of persistence past its course of working indefinitely.
Supplementary instruments
Flog webshell
Flog is a webshell discovered uploaded to VirusTotal from Iraq by the identical submitter who uploaded one of many variations of Whisper. Primarily based on that and the shut timeframe (each have been uploaded inside a matter of minutes) we consider it was deployed by BladedFeline to the sufferer within the Iraq authorities.
Flog, so named for its filename – flogon.aspx – appears to be like for particular enter from the BladedFeline operators of the shape
Flog hashes the password, which should match the MD5 checksum 4CC88CE123B0DA8D75C0FE66A39339F6.
Variables (a|b|c|d) are command choices:
- a returns, for the trail supplied, a listing itemizing and the byte size of every file,
- b creates a file on disk, utilizing the trail supplied,
- c splits the trail variable on a pipe and writes a file to disk the place the primary a part of the trail is the filename and the second half is the information to jot down, and
- d deletes a specified file given within the equipped path.
Hawking Listener
Hawking Listener, so named for its PDB string – C:Usersg18u04sourcereposHawkingHawkingobjReleaselistner.pdb – is a 32-bit .NET/C# Home windows binary with a timestomped compilation time of 2057-11-14 16:59:12. It was additionally uploaded to VirusTotal by the identical consumer who uploaded Flog and might be a BladedFeline device. It implements the .NET HTTPListener class to arrange a listener with a hardcoded URL (which we can not disclose on this case with out revealing the identification of the sufferer). Alternatively, Hawking may be supplied at runtime with URLs for the listener socket to observe.
Hawking listens for a supplied QueryString (from a BladedFeline operator) with snmflwkejrhgsey as the important thing within the key-value pair. As soon as obtained, Hawking executes the worth in cmd.exe and returns the output. To cease Hawking, operators want solely ship cease as the important thing within the QueryString with a non-null variable within the worth.
Hawking logs all interactions, runtime arguments, and command output to the file log.txt in its working listing.
P.S. Olala
P.S. Olala is a 32-bit .NET binary named for its meant operate (executing PowerShell scripts) and its PDB path G:csharppsExecuterServiceewsServiceobjReleaseOlala.pdb. It doesn’t settle for any runtime arguments. Moderately, at runtime, P.S. Olala makes use of the Run(ServiceBase[]) methodology of the .NET ServiceBase class to register itself as a service with the Service Management Supervisor (for persistence).
When the P.S. Olala service is named, it spawns a thread and executes the operate mainLoop, proven in Determine 6. Basically, P.S. Olala is an executor of the PowerShell script saved in %APPDATApercentLocalMicrosoftInputPersonalizationTrainedDataStore.ps1.
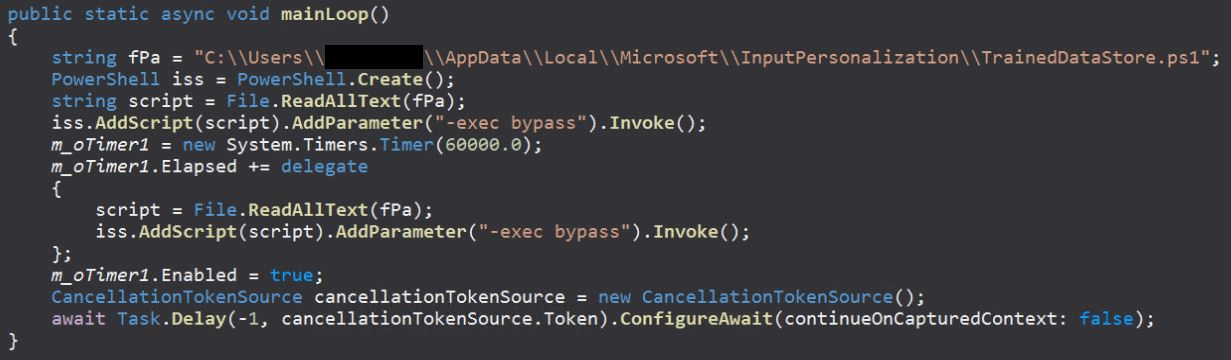
Sadly, we have been unable to gather any of the TrainedDataStore.ps1 scripts. Nonetheless, contextual data signifies it’s seemingly an executor of the Whisper backdoor, or one of many reverse tunnels (Laret or Pinar). The complete circulate (P.S. Olala → TrainedDataStore → Whisper/Laret/Pinar) might be an elongated persistence chain aiming to keep up entry.
Sheep Tunneler
Sheep Tunneler, a customized tunneling utility that we named primarily based on the PDB string C:UserssheepsourcereposMPMPobjReleaseMP.pdb), has been noticed within the two following places:
- %APPDATApercentLocalMicrosoftWindowsRingtonesRingService.exe
- %APPDATApercentLocalMicrosoftWindowsShellmspsrv.exe
Sheep Tunneler may be executed in two modes: community tunneling (through the use of the runtime argument center) or join again (through the use of the arguments cb
Whisper Protocol
Whisper Protocol, so named for its filename (Protocol.pdf.exe) is a 64-bit Python-compiled Home windows binary with a compilation timestamp of 2024-03-11 09:01:20. It creates a folder in C:ProgramDataVeeamUpdate and writes each Whisper and its configuration file to that folder. Whisper Protocol additionally copies itself to %APPDATApercentRoamingMicrosoftWindowsStart MenuProgramsStartupVeeamUpdate.lnk for persistence. Lastly, it executes Whisper and exits gracefully.
Conclusion
BladedFeline is a sophisticated risk group that makes a speciality of focusing on Iraqi and Kurdish victims, particularly governmental officers and organizations. We assess that the group is probably going a subgroup of OilRig. We anticipate finding that BladedFeline will stick with implant improvement with a view to preserve and increase entry inside its compromised sufferer set, seemingly for cyberespionage.
For any inquiries about our analysis printed on WeLiveSecurity, please contact us at [email protected].ESET Analysis affords non-public APT intelligence reviews and information feeds. For any inquiries about this service, go to the ESET Menace Intelligence web page.
IoCs
Information
| SHA-1 | Filename | Detection | Description |
| 01B99FF47EC6394753F9 |
Avamer.pdf.exe | Python/Trojan |
Python-compiled dropper for Spearal |
| 1C757ACCBC2755E83E53 |
Win_Updates.exe | MSIL/Agent.EUM | Spearal, a BladedFeline backdoor. |
| 272CF34E8DB2078A3170 |
scr8B45.ps1 | PowerShell/Trojan |
PowerShell script to put in Spearal. |
| 37859E94086EC47B3665 |
ncms_demo.msi | MSIL/Agent.EUM | MSI contained in the zip archive that drops and executes a PowerShell script that in flip drops and executes Spearal. |
| 3D21E1C9DFBA38EC6997 |
flogon.aspx | ASP/Agent.BI | Flog webshell. |
| 4954E8ACE23B48EC55F1 |
winsmsrv.exe | MSIL/HackTool |
Pinar, a reverse tunnel. |
| 562E1678EC8FDC1D83A3 |
LogonUl.exe | Win64/OilRig_ |
RDAT backdoor. |
| 66BD8DB40F4169C7F0FC |
Protocol.pdf.exe | Python/Trojan |
Whisper Protocol, the dropper that writes and executes the Whisper backdoor. |
| 6973D3FF8852A3292380 |
VeeamUpdate.exe | MSIL/Agent.ERR | Whisper backdoor. |
| 73D0FAA475C6E489B2C5 |
winhttpproxy.exe | MSIL/HackTool |
Pinar, a reverse tunnel. |
| B8AFC21EF2AA854896B9 |
RunExeActionAllowed |
MSIL/Agent.ERR | Whisper backdoor. |
| BB4FFCDBFAD40125080C |
MFTD.exe | MSIL/Tiny.GL | Hawking Listener. |
| BE0AD25B7B4834798490 |
videosrv.exe | Generik.BKYYERR | VideoSRV, a reverse shell. |
| E8E6E6AFEF3F574C1F52 |
wincapsrv.exe | MSIL/HackTool |
Laret, a reverse tunnel. |
| F28D8C5C2283019E6ED7 |
N/A | MSIL/Agent.EUM | Zip archive that incorporates an MSI that drops and executes a PowerShell script that in flip drops and executes Spearal. |
Community
| IP | Area | Internet hosting supplier | First seen | Particulars |
| 178.209.51[.]61 | N/A | 9 Web Options AG | 2023‑12‑18 | Distribution server for BladedFeline’s Laret reverse tunnel. |
| 185.76.78[.]177 | N/A | EDIS GmbH – Noc Engineer | N/A | C&C utilized by Spearal. |
MITRE ATT&CK strategies
This desk was constructed utilizing model 17 of the MITRE ATT&CK framework.
| Tactic | ID | Title | Description |
| Reconnaissance | T1595.002 | Lively Scanning: Vulnerability Scanning | BladedFeline in all probability conducts vulnerability scanning in opposition to targets to determine probably weak, uncovered functions. |
| Useful resource Improvement | T1583.001 | Purchase Infrastructure: Domains | BladedFeline registers domains to make use of for C&C servers. |
| T1583.003 | Purchase Infrastructure: Digital Non-public Server | BladedFeline makes use of VPS providers to host C&C servers. | |
| T1583 | Purchase Infrastructure | BladedFeline makes use of IPs for community infrastructure, together with distributing malware and C&C servers. | |
| T1586.002 | Compromise Accounts: E-mail Accounts | BladedFeline makes use of compromised e mail accounts as C&C servers. | |
| Preliminary Entry | T1190 | Exploit Public-Going through Software | BladedFeline in all probability exploits weak public-facing functions for preliminary entry. |
| Execution | T1059.003 | Command and Scripting Interpreter: Home windows Command Shell | BladedFeline makes use of the Home windows Command Shell to execute instructions on compromised endpoints. |
| T1059.007 | Command and Scripting Interpreter: JavaScript | BladedFeline makes use of JavaScript webshells to execute instructions on compromised endpoints. | |
| T1059.001 | Command and Scripting Interpreter: PowerShell | BladedFeline makes use of PowerShell to execute instructions on compromised endpoints. | |
| T1059.006 | Command and Scripting Interpreter: Python | BladedFeline makes use of Python as a dropper for deploying backdoors to compromised endpoints. | |
| T1559 | Inter-Course of Communication | BladedFeline makes use of IPC as a method of native code execution in its malicious IIS module. | |
| T1569.002 | System Providers: Service Execution | BladedFeline makes use of Home windows providers for malware execution with Whisper and PrimeCache. | |
| Persistence | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder | The Whisper backdoor creates a LNK file within the startup folder for persistence. |
| T1546 | Occasion Triggered Execution | PrimeCache is loaded by an IIS Employee Course of (w3wp.exe) when the IIS server receives an inbound HTTP request. | |
| Protection Evasion | T1078 | Legitimate Accounts | BladedFeline makes use of reputable accounts to exfiltrate information and bypass defenses, and as C&C servers. |
| T1140 | Deobfuscate/Decode Information or Info | The Whisper backdoor makes use of base64 encoding to obfuscate information. | |
| T1070.004 | Indicator Elimination: File Deletion | The Python dropper for Whisper deletes itself and different set up information after a profitable set up. | |
| T1070.006 | Indicator Elimination: Timestomp | BladedFeline routinely timestomps the compilation timestamps of malware that the group develops. | |
| Credential Entry | T1003.001 | OS Credential Dumping: LSASS Reminiscence | BladedFeline dumps LSASS from reminiscence to steal credentials. |
| Command and Management | T1573.001 | Encrypted Channel: Symmetric Cryptography | The Whisper backdoor makes use of AES encryption to ship and obtain information between the malware and the C&C. |
| T1071.001 | Software Layer Protocol: Net Protocols | PrimeCache makes use of normal internet protocols for communication with the C&C server. | |
| T1132.001 | Information Encoding: Normal Encoding | PrimeCache makes use of normal encoding for communication with the C&C server. | |
| T1573.002 | Encrypted Channel: Uneven Cryptography | PrimeCache makes use of RSA and AES-CBC for C&C communication. | |
| T1105 | Ingress Instrument Switch | PrimeCache has the potential to obtain further information from the C&C server for native execution. | |
| Exfiltration | T1048.001 | Exfiltration Over Various Protocol: Exfiltration Over Symmetric Encrypted Non-C2 Protocol | The Whisper backdoor makes use of AES encryption and e mail inboxes to ship and obtain information between the malware and the C&C. |
| T1041 | Exfiltration Over C2 Channel | PrimeCache exfiltrates information to a C&C server. |



