The U.S. authorities right now unsealed felony expenses towards 16 people accused of working and promoting DanaBot, a prolific pressure of information-stealing malware that has been bought on Russian cybercrime boards since 2018. The FBI says a more recent model of DanaBot was used for espionage, and that most of the defendants uncovered their real-life identities after unintentionally infecting their very own programs with the malware.

DanaBot’s options, as promoted on its assist website. Picture: welivesecurity.com.
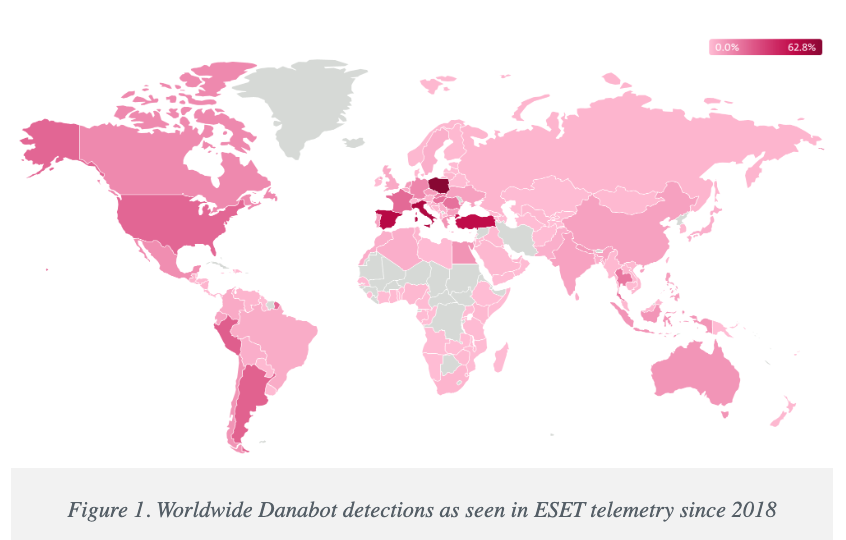
Initially noticed in Could 2018 by researchers on the electronic mail safety agency Proofpoint, DanaBot is a malware-as-a-service platform that focuses on credential theft and banking fraud.
As we speak, the U.S. Division of Justice unsealed a felony criticism and indictment from 2022, which stated the FBI recognized a minimum of 40 associates who had been paying between $3,000 and $4,000 a month for entry to the knowledge stealer platform.
The federal government says the malware contaminated greater than 300,000 programs globally, inflicting estimated losses of greater than $50 million. The ringleaders of the DanaBot conspiracy are named as Aleksandr Stepanov, 39, a.ok.a. “JimmBee,” and Artem Aleksandrovich Kalinkin, 34, a.ok.a. “Onix”, each of Novosibirsk, Russia. Kalinkin is an IT engineer for the Russian state-owned vitality large Gazprom. His Fb profile title is “Maffiozi.”
In line with the FBI, there have been a minimum of two main variations of DanaBot; the primary was bought between 2018 and June 2020, when the malware stopped being supplied on Russian cybercrime boards. The federal government alleges that the second model of DanaBot — rising in January 2021 — was offered to co-conspirators to be used in concentrating on army, diplomatic and non-governmental group computer systems in a number of nations, together with the US, Belarus, the UK, Germany, and Russia.
“Unindicted co-conspirators would use the Espionage Variant to compromise computer systems around the globe and steal delicate diplomatic communications, credentials, and different information from these focused victims,” reads a grand jury indictment dated Sept. 20, 2022. “This stolen information included monetary transactions by diplomatic workers, correspondence regarding day-to-day diplomatic exercise, in addition to summaries of a specific nation’s interactions with the US.”
The indictment says the FBI in 2022 seized servers utilized by the DanaBot authors to regulate their malware, in addition to the servers that saved stolen sufferer information. The federal government stated the server information additionally present quite a few situations wherein the DanaBot defendants contaminated their very own PCs, ensuing of their credential information being uploaded to stolen information repositories that had been seized by the feds.
“In some circumstances, such self-infections gave the impression to be intentionally accomplished with a view to take a look at, analyze, or enhance the malware,” the felony criticism reads. “In different circumstances, the infections gave the impression to be inadvertent – one of many hazards of committing cybercrime is that criminals will typically infect themselves with their very own malware by mistake.”
Picture: welivesecurity.com
A assertion from the DOJ says that as a part of right now’s operation, brokers with the Protection Legal Investigative Service (DCIS) seized the DanaBot management servers, together with dozens of digital servers hosted in the US. The federal government says it’s now working with trade companions to inform DanaBot victims and assist remediate infections. The assertion credit plenty of safety companies with offering help to the federal government, together with ESET, Flashpoint, Google, Intel 471, Lumen, PayPal, Proofpoint, Crew CYRMU, and ZScaler.
It’s not unparalleled for financially-oriented malicious software program to be repurposed for espionage. A variant of the ZeuS Trojan, which was utilized in numerous on-line banking assaults towards corporations in the US and Europe between 2007 and a minimum of 2015, was for a time diverted to espionage duties by its creator.
As detailed on this 2015 story, the creator of the ZeuS trojan created a customized model of the malware to serve purely as a spying machine, which scoured contaminated programs in Ukraine for particular key phrases in emails and paperwork that will probably solely be present in labeled paperwork.
The general public charging of the 16 DanaBot defendants comes a day after Microsoft joined a slew of tech corporations in disrupting the IT infrastructure for an additional malware-as-a-service providing — Lumma Stealer, which is likewise supplied to associates underneath tiered subscription costs starting from $250 to $1,000 per 30 days. Individually, Microsoft filed a civil lawsuit to grab management over 2,300 domains utilized by Lumma Stealer and its associates.
Additional studying:
Danabot: Analyzing a Fallen Empire
ZScaler weblog: DanaBot Launches DDoS Assault Towards the Ukrainian Ministry of Protection
Flashpoint: Operation Endgame DanaBot Malware
Crew CYRMU: Inside DanaBot’s Infrastructure: In Assist of Operation Endgame II
March 2022 felony criticism v. Artem Aleksandrovich Kalinkin
September 2022 grand jury indictment naming the 16 defendants


